Attackers Using Red Teaming Tools for Cyberattacks
While conducting our routine threat hunting exercises, Cyble Research and Intelligence Labs (CRIL) came across instances of the PowerShell Empire command and control (C&C) infrastructure. The PowerShell Empire is a post-exploitation red teaming tool used for creating stagers that connect to C&C servers after an initial compromise through vectors such as phishing emails, exploiting public-facing IT systems, and watering hole attacks, etc.
For additional clarity, we hunted for PowerShell Empire-related files in the wild and successfully identified multiple infections. The following figure shows the C&C infrastructure of PowerShell Empire.

Windows PowerShell is a popular tool utilized for managing the IT infrastructure in an organization. It comes pre-installed in Windows 7 and higher versions. It can utilize the .NET framework and Win32 APIs using the command line for multiple operations. Being a legitimate tool of Microsoft, PowerShell is typically whitelisted by multiple vendors.
PowerShell Empire was created by the Veris Group security practitioners Will Schroeder, Justin Warner, Matt Nelson, and others in 2015. In the past, various APT groups have used this tool, with a few of the notable groups being Turla, APT19, MuddyWare, APT41, APT33, and FIN10. According to its official GitHub repository page, the project has not been updated since 2019. Because of its capabilities, threat actors and security researchers use it for various post-exploitation activities, such as system information collection, pivoting, running additional reverse shell modules, and searching for file systems, etc.
Technical Details
The PowerShell Empire framework is similar to the tools used by nation-state actors for stealth APT operations. According to SANS Institute, Empire’s C&C traffic is asynchronous, encrypted, and designed to blend in with normal network activity. This makes it difficult for security researchers to identify the Empire’s communication inside an enterprise network.
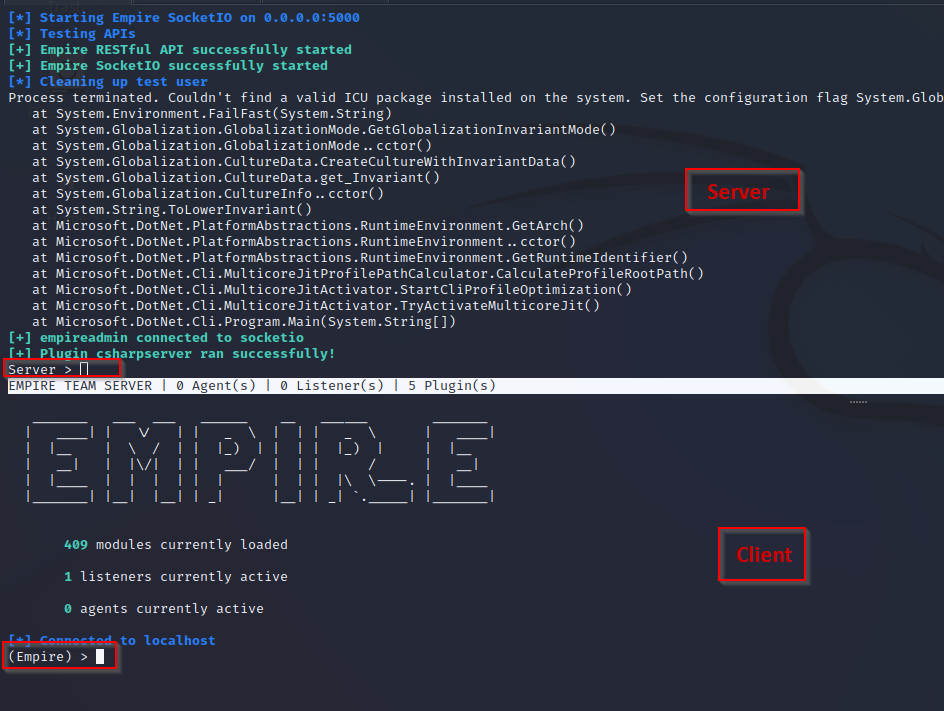
The framework is based on a client and server architecture. To develop the payload and C&C, the PowerShell Empire server and clients should be up and running. The PowerShell Client is used to create a listener and stager for performing the attack.
In the PowerShell Empire framework, the listener is the C&C, and the stager is the payload to be executed on the compromised system. After a successful initial compromise, the victim system will communicate to the C&C and register itself as an agent. Then, using the listener, the attacker can easily manage the compromised system.
The figure below shows the client and server of the PowerShell Empire.
Listener
Before attacking any system, the threat actor needs to set a C&C server. This server is called the listener. It listens to the connection from the victim machine and in return establishes the connection with the stager. The following image shows the listener module of Empire.

Stager
Stagers are similar to the payload, and after the initial compromise, stagers are dropped and executed on the victim system.

Agent
The agent is the compromised system. Empire provides a C&C framework to remotely manage multiple compromised systems at a single point. The image below showcases the Agent panel of the Empire PowerShell.

During our analysis, we generated the .hta stager payload and executed it in the target Windows machine. The .hta stager we generated launched a PowerShell command using wscript.exe. The command contained Base64 encoded shellcode required for ensuring a reverse connection, as shown in the below figure.

The figure below shows the decoded shellcode containing the browser agent and the URL for communication. To avoid detection, the C&C is further obfuscated in the script.

After execution, the client gets the reverse connection using the listener and retrieves the compromised system details. The following figure shows the reverse shell from the victim’s system.

The figure below shows the C&C communication. The network traffic is encrypted and designed to be mixed with the normal network activity. The agent continuously sends the GET request to receive commands from the C&C for performing other malicious activities.

From the communication, we can see that the three requests listed below are continuously used for C&C communication.
- /login/process.php
- /admin/get.php
- /news.php
Conclusion
Red teaming tools are critical for mimicking adversaries in order to garner insights for strengthening the cyber infrastructure of an organization. Contrary to intended users, threat actors also employ these tools to perform highly stealthy and dangerous attacks against their targets. This makes it imperative for security leaders and defenders to have a detailed understanding of such tools for securing their organizations. In the course of our threat research, we have observed similar trends earlier, wherein malware developers were seen providing highly sophisticated tools to cybercriminals for financial gain. CRIL will continue monitoring the latest threat actors and trends across the surface, deep, and darkweb and keep our readers informed on the latest cybersecurity challenges and updates.
Our Recommendations
We have listed some essential cybersecurity best practices that create the first line of control against attackers. We recommend that our readers follow the best practices given below:
How to prevent malware infection?
- Download and install software only from official app stores like Play Store or the iOS App Store.
- Use a reputed antivirus and internet security software package on your connected devices, such as PCs, laptops, and mobile devices.
- Use strong passwords and enforce multi-factor authentication wherever possible.
- Enable biometric security features such as fingerprint or facial recognition for unlocking the mobile device where possible.
- Be wary of opening any links received via SMS or emails delivered to your phone.
- Ensure that Google Play Protect is enabled on Android devices.
- Be careful while enabling any permissions.
- Keep your devices, operating systems, and applications updated.
How to identify whether you are infected?
- Regularly check the Mobile/Wi-Fi data usage of applications installed on mobile devices.
- Keep an eye on the alerts provided by Antiviruses and Android OS and take necessary actions accordingly.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Execution | T1059.001 | PowerShell |
| Privilege Escalation | T1055 | Process Injection |
| Defense Evasion | T1027 | Obfuscated Files or Information |
Indicators of Compromise (IoCs)
| Indicators | Indicator Type | Description |
| 1fc72f675e034b42dfb64cdb248acfa3 3bb3d7e5c8c1512b182800eb11318a092713361a 8860f5e08eb98f72f9e48bf2075b0dfef5362d3216f1b05d09fe079c20fd9445 | MD5 SHA1 SHA256 | 4.bat |
| d91c3f4a6dbc04e84643afc9d0c54bb9 189f56de0cf5e5defd1837cebaf0819e1381d868 48427bd9d53ca745fc82cf2264b7af8bcceecf12524dd8769f21ecd8c64038b0 | MD5 SHA1 SHA256 | delme.txt |
| 59ec8d082118c700a7aa8a336abcdc88 002ed091722554067367445ace0e4e7ca7837512 7e370d3d24b29f1459fab9c736e480f98bd47c47b717cdd039de7d6d748c1503 | MD5 SHA1 SHA256 | jnkpl.vbs |
| 1bc0994b30306078161664e5a8199918 779036c4496209717bbf07a481557189858ecb76 cdb019c73dccc5c7a087e600c4139f6db3899d0dbbf8380f06b496b4b95f589f | MD5 SHA1 SHA256 | Netflix Checker by GOD Cracked By GM`ka.rar |
| 3c7fbb1615b577b04806978d5171d98d 8d25d681f69ed3bad78cdf8a5ad65e91312e9be5 2ba0174e6d1b4b6f2d3a741558380c26ef0ab56999bfa8e00354622b078d77eb | MD5 SHA1 SHA256 | msvchost.exe |
| 6fd1fae59a7e4164aca384d98b20c0de b4b1967429dc3b23afd6f732499f08f9fed7f1c7 8bb575a85a1cc82cb6990c6b2cc15af174dff0fa93a1c8728678c5c3c5c28664 | MD5 SHA1 SHA256 | updater.exe |
| 2e2dfb589f4363b08338a54fe10570cd 59ecca905ab7aa54e13d295bea3d6a69e2fa8d3a e8356d83f5179f1e2cec68ad9f755286da721b5c1a6691d323b759b87f800db6 | MD5 SHA1 SHA256 | sys4.exe |
| c0f618d88e5f065bebbfa1ee655500d5 16057702af44cdecd3f755488512a8503932d1a0 b8123e9a7ab77b5814f5eb35f5d036dc2bd056282b48e90232f5e027e322ba0c | MD5 SHA1 SHA256 | clickme.lnk |
| 584171e0cae2e0e1d7e2aafd28004eae 54829f34b2c28e5f0f35bbc1bfc478f25f330dda c90d57feec3d22cc840ac5d9008355012bcd381dd97877ebc495e3494380238f | MD5 SHA1 SHA256 | winvbsJnkPlus.vbs |
| 8d665aa30c6fabebde0791e5434ebfed f1a913dfac7ece7c2319221064ce330fe86a525b 6862e9cdcfbded8d7f405a1437b1a036e5101f3245f392200d5fbacc96a4681c | MD5 SHA1 SHA256 | launcher_protected.exe |








