1 Platform | 14+ Capabilities | 80+ Use Cases
Step into the future of Autonomous Attack Surface Management Cyber Threat Intelligence Dark Web Monitoring Third Party Risk Management Brand Intelligence Vulnerability Management Digital Risk Protection Physical Security Intelligence Executive Monitoring Cloud Security Posture with Cyble Vision

Trusted by Hundreds of Leading Brands in 50+ Countries
Major enterprises rely on our intelligence-first security approach to strengthen resilience and stay ahead of emerging threats.



























The Future of Cyber Threat Intelligence Product
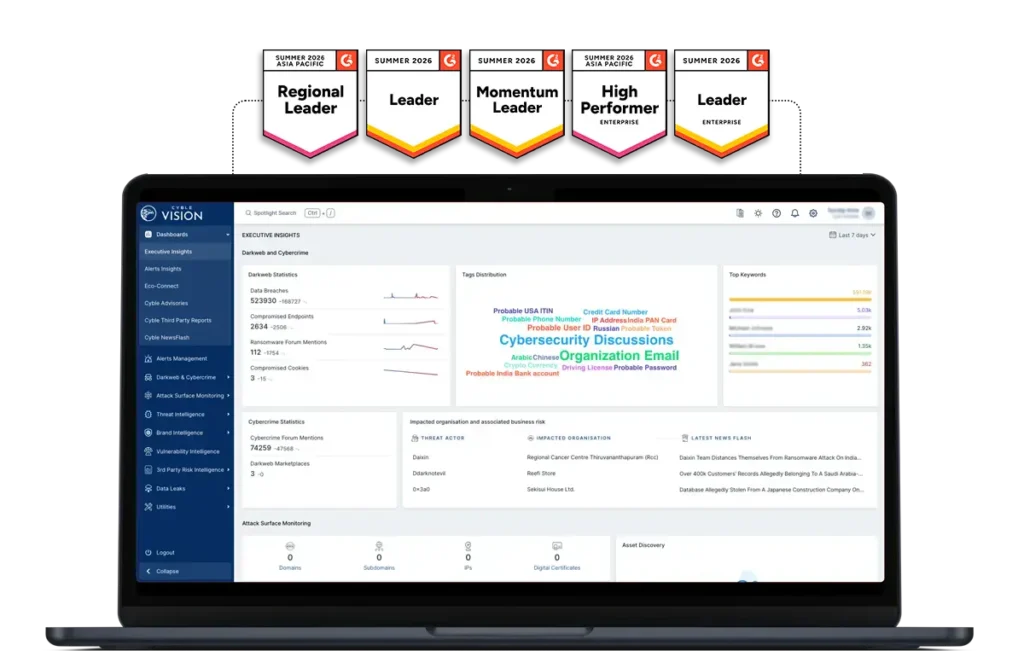
Why Choose Cyble Vision?
Agentic AI at the Core
Autonomous, intelligent systems that continuously learn, adapt, and respond to emerging threats.
Faster Decision-Making
Actionable insights transform raw data into immediate security advantage.
Integrated with Cyble Blaze AI
Supercharge investigations with advanced actor profiling, dark web intelligence, and threat attribution.
End-to-End Visibility
From digital risks to physical security intelligence, gain a 360° threat view.
Who Is Using Cyble Vision?
Financial Services & FinTech
Banks, payment platforms, and digital finance providers monitoring phishing, brand abuse, and exposed credentials.
Healthcare & Life Sciences
Hospitals, health systems, and pharma enterprises detecting patient data leaks and ransomware signals.
Manufacturing & Critical Infrastructure
Industrial and infrastructure operators tracking supply chain exposure and threat actor activity.

Retail & E-Commerce
Global brands and online marketplaces identifying impersonation domains and fraud campaigns.
Government & Public Sector
Federal, state, and public institutions monitoring hacktivist and geopolitical threats.
Security Teams & MSSPs
Enterprise SOCs and managed providers enriching investigations and accelerating response.
What Sets Cyble Vision Apart
Agentic AI for autonomous threat detection and faster response
Unified Intelligence Platform combining cyber, brand, third-party, and physical risk monitoring
Global Dark Web Coverage with unmatched visibility into hidden adversary activity
Real-Time Alerts that enable proactive defense instead of reactive firefighting
Not All Threat Intelligence Platforms Are Built Equal
Don’t just monitor threats—neutralize them faster, smarter, and with less noise using Cyble Vision.
| Feature |
 Blaze AI
Blaze AI
|
Crowdstrike | Microsoft | Mandiant | Palo Alto | Others |
|---|---|---|---|---|---|---|
| Multi-Agent AI Components for Threat Intelligence Queries | ||||||
| Workflow AI Agents (Ethical Validator, Query Validator, Knowledge Base Router, Context Handler, Response Handler) | ||||||
| Full OpenAI Engine Integration (for NLP, Summarization, etc.) | ||||||
| Sophisticated Query Understanding (Intent Parsing, Context Awareness) | ||||||
| End-to-End Automation Across Full Threat Intel Lifecycle | ||||||
| AI-Driven Threat Detection and Response | ||||||
| Deep Integration with Existing Cyble Services (TIP, BotShield, etc.) | ||||||
| Executive/Brand Monitoring with AI Agents | ||||||
| Customizable Knowledge Base and Automated Routing | ||||||
| Continuous Learning and AI Model Updates |
- Strong Capability
- Capability Provided
- Not Provided
Secure the Future with Cyble Vision
Threats are evolving — your intelligence should too. With Cyble Vision, powered by Agentic AI and Cyble Blaze AI, organizations gain the foresight and agility needed to stay several steps ahead of attackers.
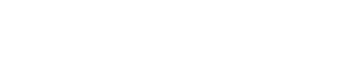
Recognized By Global Analyst Firms
- Cyble Recognized As A Challenger in 2026 Gartner® Magic Quadrant™ for Cyberthreat Intelligence
- Cyble Recognized as 2026 Gartner® Peer Insights™ Strong Performer in “Voice of the Customer” for Brand Protection Software
- Cyble Recognized in the Gartner® Hype Cycle™ for Cyber-Risk Management, 2025
- Cyble Named Sample Vendor in Gartner® Hype Cycle™ for Security Operations 2025
- Cyble Named a Sample Vendor in Gartner® Hype Cycle™ for Managed IT Services 2025
- Cyble Recognized in Gartner Emerging Tech 2025 Report
- Cyble Recognized in Gartner Hype Cycle for Cyber Risk Management 2024
- Cyble Recognized in Gartner Hype Cycle for Digital Risk Protection, 2024
- Cyble Recognized in Gartner Hype Cycle for Managed IT Services, 2024




















Why Cyble?
Cyble leverages proprietary technology to power its cutting-edge cybersecurity platforms, setting a new standard in proactive threat detection.
than others
Dark Web and Cyber Crime Monitoring
Monitor the dark web and cybercrime activities to stay vigilant and one step ahead of cybercriminals. Protect sensitive information from being exploited.
Vulnerability Management
Third-Party Risk Management (TPRM)
Cyber Threat Intelligence
Leverage AI-driven analysis and continuous threat monitoring to gain critical insights and enhance your organization’s defence against emerging cyber threats.
Cyber Threat Intelligence
Leverage AI-driven analysis and continuous threat monitoring to gain critical insights and enhance your organization’s defence against emerging cyber threats.
Cutting-Edge Cybersecurity
Brand Intelligence
Attack Surface Management
Takedown & Disruption
Physical Threat Intelligence
Vision is Not Just Any
Cyber Threat Intelligence
Cyble Vision's Capabilities Span the Entire Breach Life-cycle
Pre-Breach
Detect
During Breach
Validate
Dark Web Chatter.
Brand Mentions on Cyber Crime Forums and Market-places
Ransomware Forum Tracking.
Sensitive Data Leakage Monitoring
Impact Analysis of Third-Party Data Breaches
Post Breach
Closure
Alerts and Advisories
Incident Response
Malware Analysis and Reverse Engineering
Forensic Investigation Support
Threat Actor Engagement
Takedown Services

Cyble Blaze™ AI
Introducing Cyble Blaze AI — the world’s first dual-memory, agentic AI architecture.
AI that hunts, thinks, and protects.
Cyble Blaze AI predicts threats months in advance and automates security operations in real time — helping organizations stay decisively ahead of risk.
Cyble Vision Is Not Just Any Cyber Threat Intelligence Product
Cyble Vision’s Capabilities Span Across the Entire Breach Life-cycle.
External Attack Surface Management
- Infected Endpoints
- Critical Vulnerabilities
- Exposed Credentials
- Vulnerable users
Brand Monitoring
- Threat Intelligence
- Proactive Threat Hunting

Validate
- Dark Web Chatter
- Brand Mentions on Cyber Crime Forums and Market-places
- Ransomware Forum Tracking
- Sensitive Data Leakage Monitoring
- Impact Analysis of Third-Party Data Breaches

Closure
- Incident Response
- Malware Analysis and Reverse Engineering
- Forensic Investigation Support
- Threat Actor Engagement
- Takedown Services

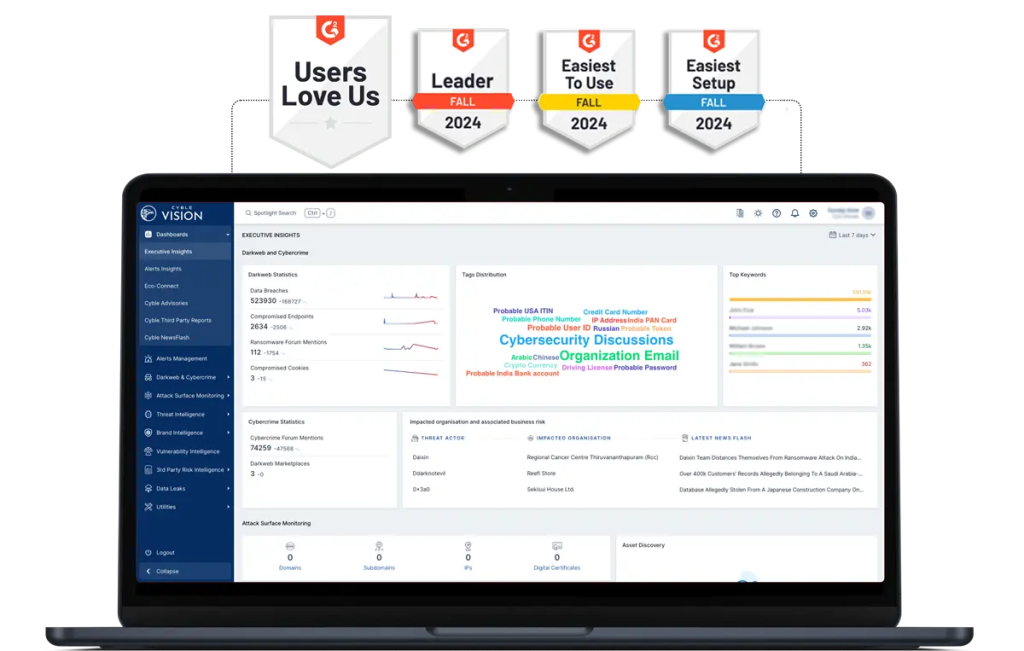
What customers say about Cyble
From Our Customers on Gartner Peer Insights
IT Manager – Miscellaneous

Cyber Security Operations Manager – Miscellaneous

CISO – Manufacturing

Deputy General Manager – Consumer Goods

Director of Engineering – IT Services

Manager of IT Services – IT Services

Compare Cyble Capabilties
Cyble and Recorded Future
Cyble and Zerofox
Cyble and Crowdstrike
Cyble and Flashpoint
Cyble and Cyberint
Cyble and Rapid7
Cyble and Cloudsek
Cyble and Ctm360
Cyble and GroupIB
Cyble and Socradar
Cyble and iZoologic
Cyble and Others
Cyble Vision Integration
Jira
Splunk
Cortex (Cyble Events V2)
Cortex (Cyble Threat Intel)
Fortinet
Sentinel
LogRhythm
RSA
Securonix
Cyware
QRadar (Cyble Events V2)
QRadar (Cyble Threat Intel)
ServiceNow
Slack
SMS
OpenAPI
MISP
Splunk
Cortex (Cyble Events V2)
Cortex (Cyble Threat Intel)
Fortinet
Sentinel
LogRhythm
RSA
Securonix
QRadar (Cyble Events V2)
QRadar (Cyble Threat Intel)
Splunk
Cortex (Cyble Events V2)
Cortex (Cyble Threat Intel)
Fortinet
Sentinel
Cyware
QRadar (Cyble Events V2)
QRadar (Cyble Threat Intel)
ServiceNow
Jira
ServiceNow
MISP
Slack
SMS
OpenAPI
FAQs
What is Cyble Vision?
Cyble Vision is an AI-driven SaaS threat intelligence platform that delivers unified visibility across digital, physical, and brand ecosystems.
- Powered by Blaze AI, it transforms security from reactive response to proactive, predictive defense
- It collects, enriches, correlates, and delivers actionable intelligence across multiple risk vectors
How is Cyble Vision different from other cyber threat intelligence platforms?
Cyble Vision stands out in several key ways:
AI-native intelligence engine
- Powered by Blaze AI for contextualization and correlation
- Moves beyond raw data to decision-ready intelligence
Multi-vector, unified visibility
- Covers cyber + physical + brand + human risks in one platform
- Eliminates fragmented tools and siloed intelligence
End-to-end intelligence lifecycle
- Combines:
- Data collection
- AI-driven enrichment & correlation
- Delivery + action (alerts, workflows, APIs)
Built for action, not just insights
- Provides incident workflows, alerts, and integrations for real-time response
- Enables automated orchestration, not just reporting
What threats does Cyble Vision detect and monitor?
Cyble Vision detects and monitors a wide range of cyber threats across digital, cloud, brand, and physical environments. It provides visibility into:
- Dark web and cybercrime activity, including data leaks, credential exposures, and threat actor discussions
- Phishing and brand impersonation attacks, including malicious domains and fake assets
- Ransomware, malware activity, and emerging threat campaigns
- Attack surface exposures, such as exposed assets, misconfigurations, and vulnerable services
- Cloud security risks, including misconfigurations and compliance gaps
- Executive threats, including impersonation and targeted attacks
- Third-party and supply chain risks, based on external exposure and breach intelligence
- Physical risk signals, such as geopolitical events and location-based threats
These capabilities are powered by Cyble’s proprietary AI engine, BlazeAI, which enables contextual enrichment, correlation, and prioritization of threats to help organizations respond faster and more effectively.
Which industries and teams use Cyble Vision?
Cyble Vision is used by organizations across industries that require continuous threat visibility and intelligence-driven security operations.
Industries
- Financial Services & Banking
- Healthcare & Pharmaceuticals
- Government & Critical Infrastructure
- Retail & E-commerce
- Technology & SaaS
- Manufacturing & Supply Chain
Teams
- Security Operations Centers (SOC) for threat monitoring and response
- Cyber Threat Intelligence (CTI) teams for threat analysis and tracking
- Risk and compliance teams for third-party and regulatory risk visibility
- Security leadership (CISOs) for strategic security decision-making
What security tools and platforms does Cyble Vision integrate with?
Cyble Vision integrates with a wide range of enterprise security tools, enabling organizations to operationalize threat intelligence within existing workflows.
It supports integration with:
- SIEM platforms (Security Information and Event Management)
- SOAR platforms (Security Orchestration, Automation, and Response)
- EDR/XDR solutions for endpoint detection and response
- Threat Intelligence Platforms (TIPs) for intelligence sharing and enrichment
- ITSM tools for incident and ticket management
- Communication channels such as email, SMS, and messaging platforms
Cyble Vision also provides API-based access for seamless integration with internal systems and automated workflows.
What is the scale of Cyble Vision's threat intelligence coverage?
Cyble Vision provides large-scale, global threat intelligence coverage through continuous monitoring and AI-driven processing.
Its coverage includes:
- Surface, deep, and dark web intelligence sources
- Threat actor activity, malware campaigns, and vulnerability intelligence
- Attack surface visibility across domains, IPs, and cloud environments
- Brand, executive, and third-party risk monitoring
Powered by its Blaze AI engine, Cyble Vision processes large volumes of structured and unstructured data to deliver contextual, actionable intelligence with reduced noise.
What makes Cyble Vision a leading Threat Intelligence Product?


