Bl00dy Ransomware Group, after targeting several universities and colleges in the US with PaperCut NG critical vulnerability in April-May 2023, has claimed its first victim in India on May 28, 2023, and demanded a ransom of USD 90,000. Cyble Research & Intelligence Labs (CRIL) elaborately covered the criticality of this vulnerability and exposed worldwide assets in a blog on April 25, 2023.
Details of the Incident
On May 28, 2023, the Bl00dy ransomware group claimed to compromise an India-based institute offering various undergraduate and graduate courses. The group posted multiple screenshots as proof of compromise, demonstrating administrative access to the organization via RDP.
One of the screenshots shared by the group demonstrates PaperCut MF/NG print management software installed on the machine.

Open-source research suggests that ports 9191 and 3389 are open, and instances of the compromised organization are publicly exposed. The publicly available POC of the PaperCut NG vulnerability demonstrates that port 9191 is targeted when leveraging the vulnerability. Therefore, it is highly likely that the Bl00dy ransomware group leveraged the PaperCut vulnerability to establish an initial network connection.

Another screenshot demonstrates the ransom note asking for USD 90,000 from the organization to decrypt the compromised data.

One of the screenshots demonstrates the organization’s Active Directory, with access to 10,014 systems assigned to students.

Another screenshot demonstrates access to Moodle server, helpdesk server, dummy web server, and ERP server of the organization, which contains 16.4 GB of data in total.

The dummy web server contains 87.8 GB of data consisting of multiple records and backup files.

Figure 7 demonstrates access to a folder dubbed ‘**STAFF’, which contains multiple records and names, possibly of the university’s staff, with the latest timestamp of May 10, 2023.

Overview of Bl00dy Ransomware Group
Bl00dy emerged in the ransomware scene in August 2022. They use Telegram and Twitter to post details of their victims. The group migrated from its earlier C/C++ coded payload to the leaked builder of LOCKBIT 3.0 and subsequently, from November 2022, is understood to be using a new builder based on leaked Conti source code.
Victimology
On April 29, 2023, the Bl00dy ransomware group claimed to have attacked several education institutes in the US on their social media handle. Subsequently, from May 1, 2023, they started revealing the names of these institutions to name-shame them. The group has claimed to have targeted at least six colleges/schools from the start of May. Not stopping there, the ransomware group also leaked negotiation chat screenshots with their victim entities and data samples to pressurize them to pay the ransom.
Prior to these institutes, the group claimed to have targeted a media company in the United Kingdom in mid-April 2023 after a long period of inactivity since December 2022.

Vulnerability Details
The CVE-2023-27350, PaperCut NG critical flaw, has a CVSS v3 score of 9.8 out of 10. A remote attacker can leverage this vulnerability to bypass authentication and execute arbitrary code in the context of SYSTEM.
Recently, the Federal Bureau of Investigation (FBI) and Cybersecurity and Infrastructure Security Agency (CISA) released the joint Cybersecurity Advisory (CSA), illustrating the active exploitation of CVE-2023-27350 by Bl00dy Ransomware Gang.
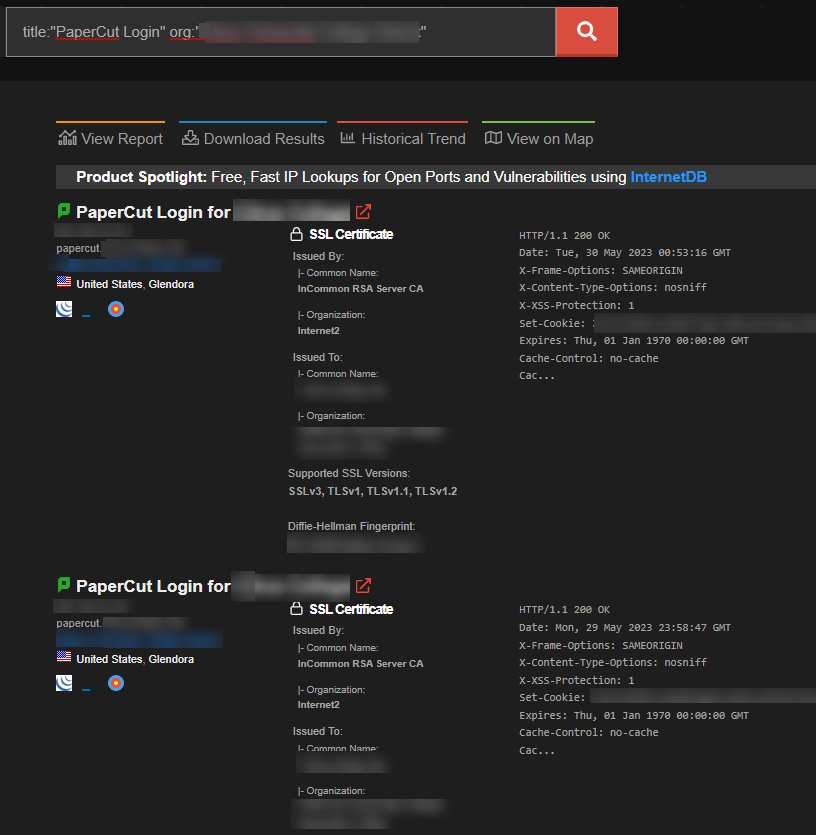
Open-source research suggests that still 1,013 instances are publicly exposed, which can be leveraged by Ransomware and APT groups to target the organizations for illicit purposes.

A few US-based colleges/schools that Bl00dy Ransomware Group announced to have targeted at the beginning of May 2023 still have this vulnerability unpatched.
Recommendations
- Keeping software, firmware, and applications updated with the recent patches and mitigations released by the official vendor is necessary to prevent attackers from exploiting vulnerabilities.
- Implement proper network segmentation to prevent attackers from performing lateral movement and minimize exposure of critical assets over the internet.
- Keep critical assets behind properly configured and updated firewalls.
- We highly recommend locking down network access to the server(s), particularly if you have an older application with no minor patch available.
- Block all inbound traffic from external IPs to the web management port (Port 9191 and 9192 by default)
- Block all traffic inbound to the web management portal on the firewall to the server. Note: this will prevent lateral movement from internal hosts, but the PaperCut service management can only be performed on that asset.
- Apply “Allow list” restrictions under Options > Advanced > Security > Allowed site server IP addresses. Set this only to allow the IP addresses of verified Site Servers on your network.




















