Another day, another data breach. This is how the cybersecurity world is waking up every day now.
But at times, some breaches are massive and sensitive enough to talk.
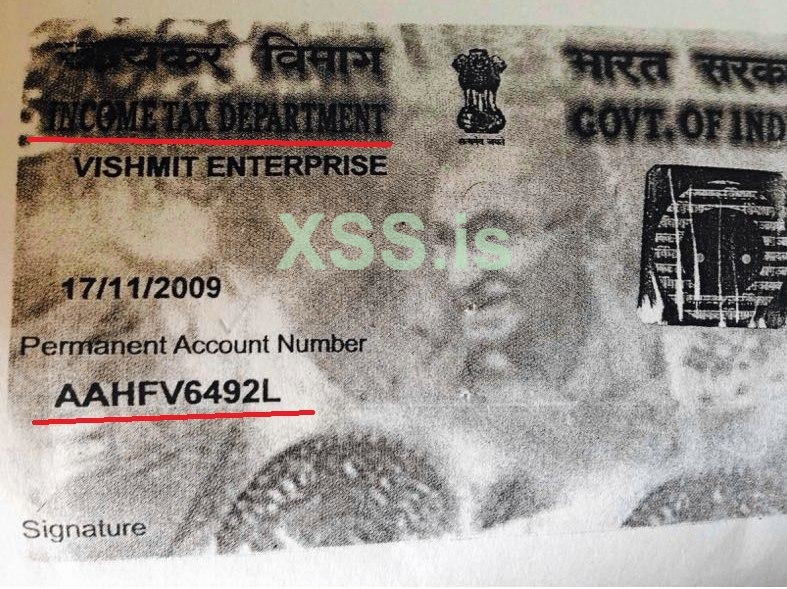
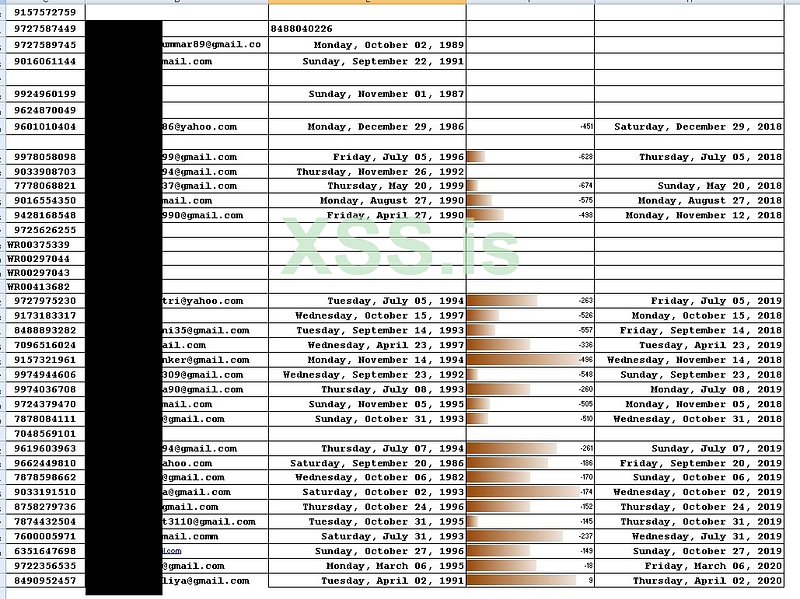
Cyble researchers have uncovered a significant data breach at Indian Tax Office department which has exposed their citizen’s PAN cards etc. While it unclear if the systems of the department were breaches or a third party system connected with it. Regardless, this has lead to massive exposure.
The breach details were shared at a hacking forum and are now available for sale. Based on the details shared, it appears the PAN cards details have been exposed — which is equivalent to tax file number in other countries. This typically has a name, date of birth and signature and other details.
Update — On March 28, 2020, the actor lost access to the server. At this stage, there is no evidence suggesting that the above-said data was exfiltrated.

About Cyble:
Cyble Inc.’s mission is to provide organizations with a real-time view of their supply chain cyber threats and risks. Their SaaS-based solution powered by machine learning and human analysis provides organizations’ insights to cyber threats introduced by suppliers and enables them to respond to them faster and more efficiently.
Cyble strives to be a reliable partner/facilitator to its clients allowing them with unprecedented security scoring of suppliers through cyber intelligence sourced from open and closed channels such as OSINT, the dark web and deep web monitoring and passive scanning of internet presence. Furthermore, the intelligence clubbed with machine learning capabilities fused with human analysis also allows clients to gain real-time cyber threat intel and help build better and stronger resilience to cyber breaches and hacks. Due to the nature of the collected data, the company also offer threat intelligence capabilities out-of-box to their subscribers.





















