Stealer impersonating Solution File (.sln) via a fake GitHub repo
GitHub is a web platform that facilitates version control and collaboration for software development projects. This enables users to store and manage their source code repositories, track code modifications, and collaborate with others on the same project. While GitHub serves as a hosting platform for legitimate code, it can also be misused by Threat Actors (TAs) to distribute malware, backdoors, or exploits through repositories. This duality makes GitHub susceptible to both legitimate and malicious code sharing.
GitHub makes it easy for users to clone repositories, which means they can create a local copy of a repository on their own machines. TAs may create repositories that appear to contain useful or legitimate code but actually include hidden malware.
Users inadvertently download and execute malicious code when they clone such repositories. TAs can leverage the collaborative nature of GitHub to trick users into executing malicious code. They may create repositories with enticing names or descriptions, posing as legitimate projects or offering valuable tools. Unsuspecting users who unknowingly clone or download these repositories may become victims of malware infections.
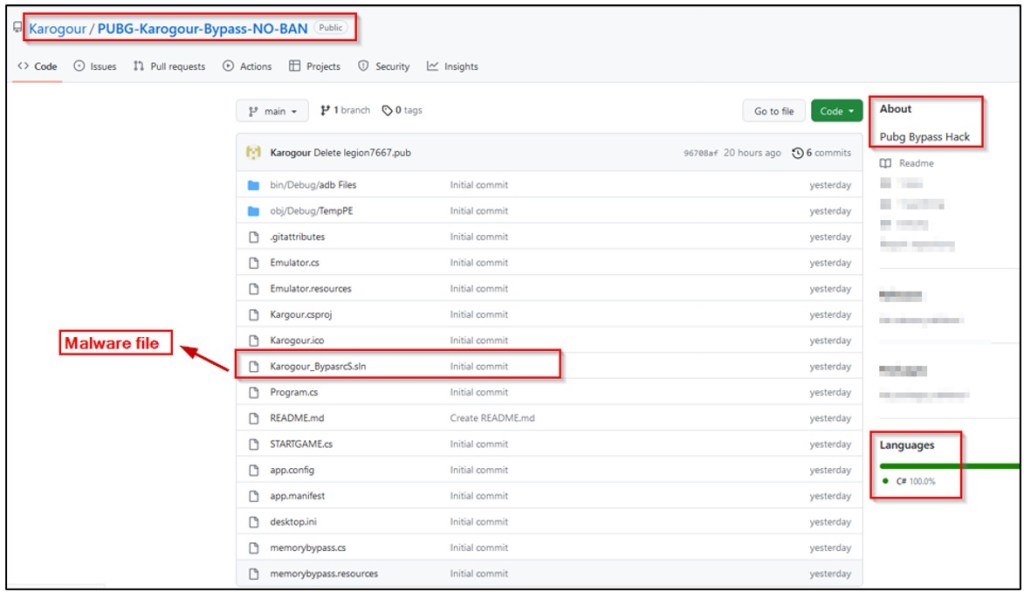
Cyble Research and Intelligence Labs (CRIL) recently discovered a GitHub page that masquerades as a PUBG bypass hack project but distributes a malicious file. When users download the project and execute the solution (.sln) file, it unknowingly deploys an information stealer called “Legion Stealer” onto their systems as a payload.
A PUBG bypass hack refers to a type of cheat or exploit used by players to gain an unfair advantage over other players. Bypass hacks are designed to bypass or circumvent the game’s security measures and anti-cheat systems to enable various cheats and hacks, such as aimbots, wallhacks, speed hacks, and other unfair gameplay advantages.
Hacks such as these can allow players to see through walls, automatically aim at opponents, move faster than normal, and perform other actions that are not possible within the regular gameplay mechanics of the game. Using bypass hacks is against the game’s terms of service and can result in penalties, including temporary or permanent bans.
The image below reveals a GitHub page that falsely presents itself as a source for a PUBG bypass NO BAN script but distributes a malware file instead.
Technical Details
When the user selects the “Download ZIP” option on the “PUBG-Karogour-Bypass-NO-BAN” GitHub page, the project file will be saved to the local system with the name “PUBG-Karogour-Bypass-NO-BAN-main.zip”, as shown below.

After unzipping the archive file, it contains various types of files, including source code (.cs), project (.csproj), solution (.sln), icon (.ico), resources (.resources), and other supporting files like app.config, desktop.ini, and Readme.md. Additionally, there are project folders such as bin and obj, as illustrated in Figure 3.
In C# projects, the solution (.sln) file is created by Microsoft Visual Studio. The SLN file acts as a workspace or container that helps organize multiple interconnected projects. The SLN file format is a text-based file that follows a specific structure and contains information about the projects and configurations within a Visual Studio solution.
Inside the downloaded zip file, the “Karogour_BypasrcS.sln” file turns out to be a screen saver (executable) file rather than a text-based solution file (.sln) typically used in C# projects.
The file originally had the name “Karogour_Bypasnls.Scr”. However, in an attempt to deceive users, the TA reversed the last 7 characters of the file name, changing it from “nls.Scr” to “rcS.sln” to make it appear as a solution file, as shown below.

The “Karogour_BypasrcS.sln” is a 32-bit GUI-based executable file that was compiled using a .NET compiler and has a SHA256 hash of 8653df677fc1fb616c082e94f178474c91e62abfffadd2dec4e8d501466a2b8a, as shown below.

Upon execution of the “Karogour_BypasrcS.sln” file, it drops two files directly in the root of the %appdata% folder and runs it. These files are named “Local_ycsNYnaBZ.sln” and “LocalchfRgyVJSk.exe”.
The figure below displays the files that have been dropped in the root of the %appdata% directory.
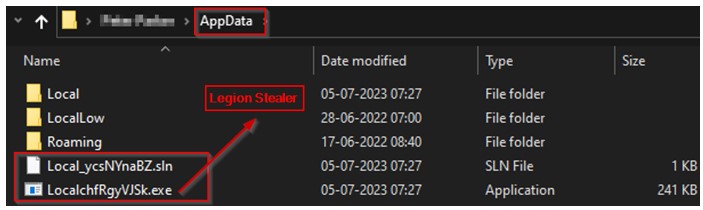
When the “Local_ycsNYnaBZ.sln” is started, it launches the code in the Visual Studio editor. This action is designed to deceive the user into believing they are viewing the content of the “Karogour_BypasrcS.sln” file, creating a false impression, as shown below.

During the display of the SLN file, the “LocalchfRgyVJSk.exe” executable is also executed in the background without the user’s knowledge. This executable is identified as a Legion Stealer malware payload.
The following figure illustrates the process tree associated with the malware infection caused by the malicious counterfeit PUBG-Bypass-NO-BAN script.

Legion Stealer
The Legion Stealer payload has a SHA256 hash of a4b7c26cdfff6f4b055d3f7fd394553917701649f0faabccd7861651d08c59fd.
It is a 32-bit executable compiled using .NET and obfuscated using an unknown obfuscator. The below figure shows the file details of the de-obfuscated Legion payload.

Upon execution, Legion Stealer executes a series of commands, which include manipulating Windows Defender settings, extracting information from the registry, and gathering system details. These actions are aimed at evading detection, unauthorized access, and exploiting vulnerabilities present in the compromised system.
The table below lists the commands that were executed by Legion Stealer.
| Commands | Description |
| “powershell.exe” Add-MpPreference -ExclusionPath ‘C:\Users\<user>\AppData\LocalchfRgyVJSk.exe’ | This command adds an exclusion path to Windows Defender’s preferences, excluding the specified file (chfRgyVJSk.exe) from being scanned for malware by Windows Defender. |
| “powershell.exe” Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend && powershell Set-MpPreference -SubmitSamplesConsent 2 | This command disables several security features of Windows Defender, such as intrusion prevention, real-time monitoring, script scanning, and Controlled Folder Access. It also configures network protection in audit mode, disables MAPS reporting, and sets the consent for submitting malware samples to “Never Send” initially, and then changes it to “2” in the subsequent PowerShell command. |
| “powershell.exe” Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | This command retrieves the value of the “.ROBLOSECURITY” property from the specified registry path of HKCU. This value is related to authentication or session information for the Roblox Studio Browser. |
| “powershell.exe” Get-ItemPropertyValue -Path HKLN:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | This command attempts to retrieve the value of the “.ROBLOSECURITY” property from the specified registry path of HKLM. This value is related to authentication or session information for the Roblox Studio Browser, like the previous one. (It seems there’s a typo in the command; it should be HKLM instead of HKLN.) |
| “wmic.exe” os get Caption | This command uses Windows Management Instrumentation Command-line (WMIC) to retrieve the caption or name of the operating system installed on the system. |
| “wmic.exe” computersystem get totalphysicalmemory | This command uses WMIC to retrieve the total amount of physical memory (RAM) installed on the computer system. |
| “wmic.exe” csproduct get uuid | This command uses WMIC to retrieve the computer system’s product’s UUID (Universally Unique Identifier). |
| “powershell.exe” Get-ItemPropertyValue -Path ‘HKLM:System\CurrentControlSet\Control\Session Manager\Environment’ -Name PROCESSOR_IDENTIFIER | This command retrieves the value of the “PROCESSOR_IDENTIFIER” environment variable from the specified registry path. It provides information about the processor or CPU installed on the system. |
| “wmic” path win32_VideoController get name | This command uses WMIC to retrieve the names of the video controllers (graphics cards) installed on the system. |
The depicted figure below provides an overview of the activities carried out by the Legion stealer upon execution, which includes anti-debugging and anti-VM techniques, the creation of mutexes, as well as the stealing of sensitive information from the victim’s system.

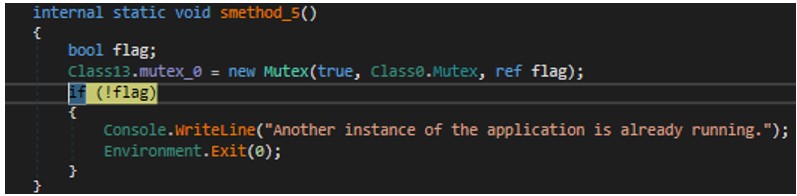
Mutex
When executed, the malware first checks if a specific mutex string, “mRd5kJFGuVrnySeulPsJ,” exists. If it finds the mutex string, it indicates that another instance of the application is already running on the user’s machine. In such cases, the malware terminates its execution to avoid duplicating instances, as shown in the below code.
Killing Processes
Then, the stealer scans against a hardcoded list of application process names associated with virtualization software and malware analysis tools. If any of these processes are detected as active on the victim’s machine, the malware takes action to terminate them.
The applications are mentioned in the figure below.

Detecting Controlled Environments
The stealer also has a list of PC names, usernames, and hardware IDs that it utilizes as identifiers to detect whether it is running in a controlled environment. If there is a match between the PC name, username, or hardware ID in use and any entry in the list, the stealer will terminate its operation. The following figure contains the usernames, PC names, and hardware IDs.

Collecting System Information
After performing the defense evasion techniques, the stealer initiates the process of gathering system information, including computer name, OS name, RAM size, UUID, CPU details, GPU details, and product key. Additionally, it acquires IP-related information such as IP address, region, country, time zone, cellular data connectivity, proxy/VPN usage, and reverse DNS.

Stealing Browser Passwords & Cookies
Subsequently, the stealer examines the system to identify the presence of specific web browsers, namely Brave, Chrome, Chromium, Comodo Dragon, Edge, Epic Privacy, Iridium, Opera, Opera GX, Slimjet, UR Browser, Vivaldi, and Yandex. It aims to extract sensitive information such as passwords and cookies from browsers using the GetPasswords() and GetCookies().
The following figure illustrates the code snippet used to check the existence of Brave browsers and extract passwords and cookies from them.

Grabbing Crypto wallets
Afterward, the stealer retrieves data associated with cryptocurrency wallets such as Zcash, Armory, Bytecoin, Jaxx, Exodus, Ethereum, Electrum, AtomicWallet, Guarda, and Coinomi. It achieves this by querying and reading files located within their respective directories.
The following figure showcases the stealer’s focus on targeting crypto wallets.

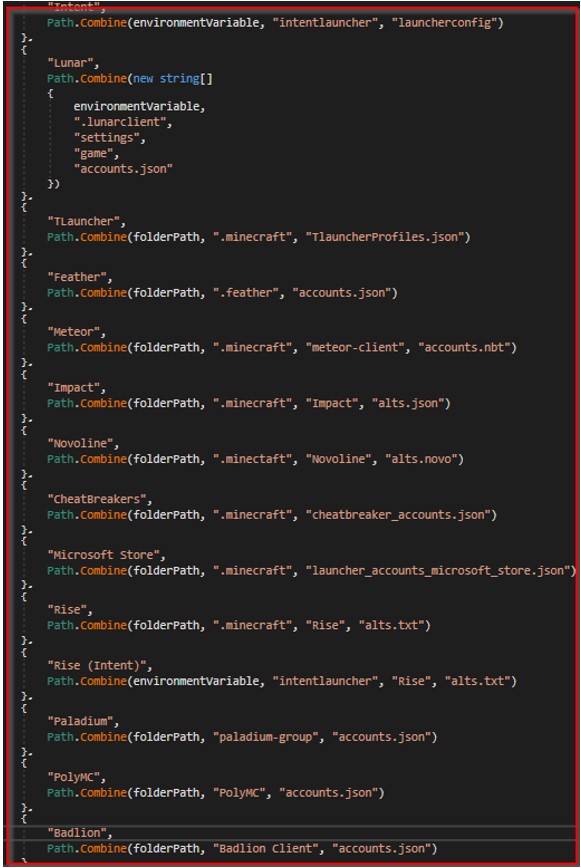
Stealing Minecraft Session Files
Furthermore, the stealer specifically targets Minecraft session files. It incorporates a routine to extract the configuration and credentials from application files associated with Minecraft, such as Lunar, TLauncher, Feather, Meteor, Impact, Novoline, CheatBreakers, Microsoft Store, Rise, Palladium, PolyMC, and Badlion, as shown below.
Additionally, the malware collects sensitive session files from messaging applications such as Discord and Telegram. Furthermore, it collects Roblox cookies, captures webcam images, and takes screenshots of the victim’s system.
Exfiltration
Finally, the malware generates a list and includes an overview of the stolen data, as depicted in the below figure. Subsequently, it transmits this list to a Discord server.

The stealer compresses the folder containing the stolen data and exfiltrates it to the Discord server. The collected data is sent to the attacker through Discord webhooks, as illustrated in the below image.

Conclusion
Video games, such as the widely popular PlayerUnknown’s Battle Grounds (PUBG), attract a significant number of users, creating a larger target audience for distributing malware. Gamers, who often place trust in gaming-related content, are more vulnerable to downloading files or running scripts without proper caution. Due to their desire for an unfair advantage in games, many gamers are tempted to use cheats or hacks. TAs exploit this demand by camouflaging their malware as game cheats or bypasses.
In this case, we have observed that TAs are utilizing a GitHub-hosted PUBG bypass hack script as a medium to distribute the Legion Stealer malware. It is a newly emerged Information stealer. While established and widely used InfoStealers exist in the cybercrime market, TAs opt for newer strains to stay updated. The rise of InfoStealers is concerning as they aid TAs in obtaining initial access, enabling them to compromise corporate networks, thus amplifying the threat landscape.
CRIL will continue monitoring the new malware strains and phishing campaigns in the wild and update blogs with actionable intelligence to protect users from such notorious attacks.
Our Recommendations
- Avoid downloading files from untrusted sources.
- Clear browsing history and reset passwords at regular intervals.
- Turn on the automatic software update feature on your computer, mobile, and other connected devices.
- Use a reputed anti-virus and internet security software package on your connected devices, including PC, laptop, and mobile.
- Refrain from opening untrusted links and email attachments without first verifying their authenticity.
- Educate employees on protecting themselves from threats like phishing/untrusted URLs.
- Block URLs that could be used to spread the malware, e.g., Torrent/Warez.
- Monitor the beacon on the network level to block data exfiltration by malware or TAs.
- Enable Data Loss Prevention (DLP) Solutions on the employees’ systems.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Execution | T1204 T1059 T1047 | User Execution Command and Scripting Interpreter Windows Management Instrumentation |
| Defense Evasion | T1497 T1027 T1562 | Virtualization/Sandbox Evasion Obfuscated Files or Information Disable or Modify Tools |
| Credential Access | T1003 | OS Credential Dumping |
| Discovery | T1057 T1012 T1082 T1083 T1518 | Process Discovery Query Registry System Information Discovery File and Directory Discovery Security Software Discovery |
| Collection | T1005 T1113 | Data from Local System Screen Capture |
| C&C | T1071 T1573 | Application Layer Protocol Encrypted Channel |
Indicators Of Compromise
| Indicators | Indicator Type | Description |
| f810afdfb042daa0a0acb7b1239a3a95 cdbcabfdf8f90df54b646a0365ae250f77d4d1e3 8653df677fc1fb616c082e94f178474c91e62abfffadd2dec4e8d501466a2b8a | MD5 SHA1 SHA256 | Karogour_Bypasnls.Scr (Main exe file) |
| c571b3895af61c2c90d4cdde6b91a64f 902cb9d246878b3fbbccaa93909d9112676fd62e a4b7c26cdfff6f4b055d3f7fd394553917701649f0faabccd7861651d08c59fd | MD5 SHA1 SHA256 | Legion Stealer Payload |




















