Mercurial Grabber is an open-source C# malware builder developed in May 2021 and uploaded on Github as a public repository for educational purposes. However, Threat Actors (TAs) have been using this builder to target people and steal thobserved and reportedeir information by modifying the code given in the repository.
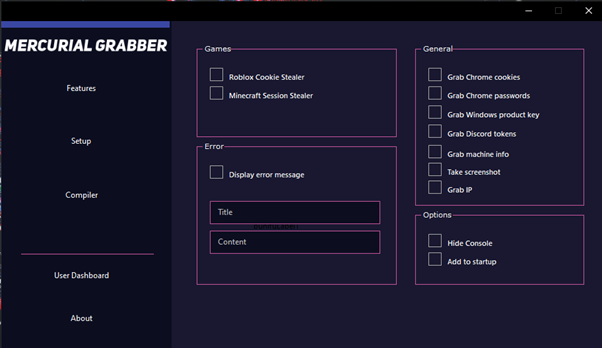
TAs can customize the builder and steal user information such as Chrome browser passwords and cookies, Windows product keys, Discord tokens, victims’ device info with screenshots and IP information. This Stealer can also steal the cookies of Roblox and the session data of the popular game – Minecraft.
The builder provides additional features to any attackers leveraging it. Some of these are hiding the console during execution, creating start-up entries to establish persistence, and using anti-VM techniques to ensure the malware does not run in a virtual environment.
The builder also uses an anti-debugging trick to prevent anyone from debugging it. It also provides additional features for the attacker to use their personalized file icons, file names, and Command and Control (C&C) server details while compiling the malware binary.

Figure 2 shows a screenshot of the Mercurial Grabber Builder dashboard.
Cyble Research Labs has evidenced that Threat Actors have used Mercurial Grabber stealer malware in recent data leaks. The following image shows Mercurial Grabber stealer logs captured by a TA in a major data leak.

Technical Analysis
In this blog post, we will conduct a deep dive analysis of the technical details of Mercurial Grabber.
We have downloaded the publicly available Mercurial Github repository, customized the settings, and compiled the binary for analyzing it. We have also changed the C&C option of the builder to testing.com to understand the C&C communication behaviour.

The static analysis of the compiled binary reveals that the malware is in x86 architecture Windows binary written in C# language (.NETv4.0.30319).

While debugging the sample, we have observed that the stealer malware contains separate classes of code for stealing functionalities, as shown in Figure 6.

Main Function
Figure 7 shows the primary function of the Mercurial Stealer. When the Stealer is executed, it hides its console in the background. Additionally, it checks for the involvement of any anti-debugging techniques and checks for the presence of VM in the user’s machine. If any one of the checks is found positive, the malware terminates itself without executing further.

Stealing Windows Product Keys
The Stealer reads the registry data from the location SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\DigitalProductId anduses the custom logic to get the Windows product key of the victim’s machine. After converting the product key to a readable format, the Stealer then sends it to the C&C server.

Stealing Passwords & Cookies from Chrome Browser
The malware steals saved credentials from the Chrome browser by reading the .db file from the following location:
- Google\Chrome\User Data\default\Login Data\login.db
Additionally, the malware creates a file named “passwords.txt,” appends the stolen credentials in the newly generated file and sends the file to the C&C server.
The malware uses a similar process to steal Chrome cookie details from the below location:
- Google\Chrome\User Data\default\Cookies\cookies.db
The malware then creates a file called “cookies.txt” and copies the details to the newly created file to send to the C&C server.

Stealing IP Address and Geolocation
The Stealer captures the victims; IP address details and other information such as country, country code, region name, city, ZIP code, and ISP using the websites mentioned below:
- https://ip4.seeip.org,
- http://ip-api.com//json/
- https://www.countryflags.io/ given within the code.

Stealing device and Hardware information
The malware also can steal information such as Operating System name, processor information, GPU information, disk, and memory details from the compromised machine.

Stealing captured screenshots
The stealer captures the desktop image of the infected machine and saves it as “capture.jpg” in the “Temp” folder before sending data to its C&C server.

Stealing Minecraft Session
The malware steals Minecraft’s session and account details by reading the JSON files “lanucher_profiles.json”, as shown below.

Stealing Roblox cookies information
The Stealer reads the Robox game cookie information from the registry location mentioned in Figure 14 and sends it to the C&C server.

Persistence Mechanism
Mercurial Grabber stealer creates a start-up entry to ensure the malware runs every time after system reboot.

Embedded SQLite Library
This Stealer has an SQLite library embedded to systematically manage all data and send it to the C&C server.

Anti-VM Techniques
The Stealer checks for the presence of virtualization software such as VMware, VirtualBox, vboxm, qemu, and Xen and terminates its execution if such virtualization software is identified. The Stealer also checks for the presence of a debugger in the machine. It terminates the execution if the condition is found to be “True”.

Encryption Technique
The Stealer uses the AES GCM encryption technique to encrypt the data before exfiltrating and uses the bcrypt.dll file, supporting the encryption process.

Communication with C&C Server
Finally, the stolen data is sent to the Threat Actor’s C&C server, which an attacker can customize accordingly. The Stealer uses two functions, SendContent() and SendData(), to send the stolen data successfully to the C&C server.


Conclusion
Threat Actors have been using similar malware to steal sensitive data from victim devices for some time now. Currently, we have observed Stealer malware becoming increasingly active worldwide.
The primary vectors for spreading this malware are pirated software and targeted phishing campaigns. Cyble Research Labs previously observed and reported Stealer activity aimed at organizations to steal employees’ credentials.
Cyble Research Labs will continue to monitor emerging threats and targeted cyber-attacks.
Our Recommendations
We have listed some essential cybersecurity best practices that create the first line of control against attackers. We recommend that our readers follow the suggestions given below:
- Don’t keep important files at common locations such as the Desktop, My Documents, etc.
- Use strong passwords and enforce multi-factor authentication wherever possible.
- Turn on the automatic software update feature on your computer, mobile, and other connected devices wherever possible and pragmatic.
- Use a reputed anti-virus and Internet security software package on your connected devices, including PC, laptop, and mobile.
- Refrain from opening untrusted links and email attachments without verifying their authenticity.
- Conduct regular backup practices and keep those backups offline or in a separate network.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566 | Phishing |
| Execution | T1204 | User Execution |
| Credential Access | T1555 T1539 T1552 | Credentials from Password Stores Steal Web Session Cookie Unsecured Credentials |
| Collection | T1113 | Screen Capture |
| Discovery | T1087 T1518 T1057 T1007 T1614 | Account Discovery Software Discovery Process Discovery System Service Discovery System Location Discovery |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Exfiltration | T1041 | Exfiltration Over C&C Channel |
Indicators Of Compromise (IoCs)
| Indicators | Indicator type | Description |
| 493fa8da8bf89ea773aeb282215f78219a5401b7 | SHA-1 | Mercurial Builder |
a3b0302fe2074ffb56a07b38209defcf9133b5d055b37e8aaa4e285a95df99e4 | SHA-256 | Mercurial.exe |
| c2603d684ad273865985ea6e7ce27c9236e173d7633a72f2378a1309d9ec77ac | SHA-256 | XdPHZWGz4k.exe |
| aa241e2f1fb8a02c501e19fd1536dc9bba3383ed8240a0e2dc338c40ddc421db | SHA-256 | Instagramm Checker Working 2021.exe |
| e466019483c3f15e67e28bad15601277251e573e28dadb444bacbc71887f21b9 | SHA-256 | All_Games_Hacks.exe |