Windows Shortcut files used to deliver payload
Online digital tools are used by many people today simply due to their ease of use and the fact that they provide a platform for the user to perform various operations effectively. These tools are web-based software hosted on websites and can be accessed via the internet without having to download and install anything on the user’s machine. There are many online digital tools to achieve multiple tasks such as sharing files, designing logos, creating flowcharts, converting files, making PDF documents, editing videos & audio, etc.
Recently, Cyble Research and Intelligence Labs (CRIL) discovered a phishing site, “hxxps://convertigoto.net/,” that impersonated a genuine “Convertio” website. Convertio is an easy online tool that converts files into different file formats, including documents, images, spreadsheets, eBooks, archives, presentations, audio, video, etc. The phishing website is well-designed and appears similar to the legitimate Convertio website, as shown in the figure below.

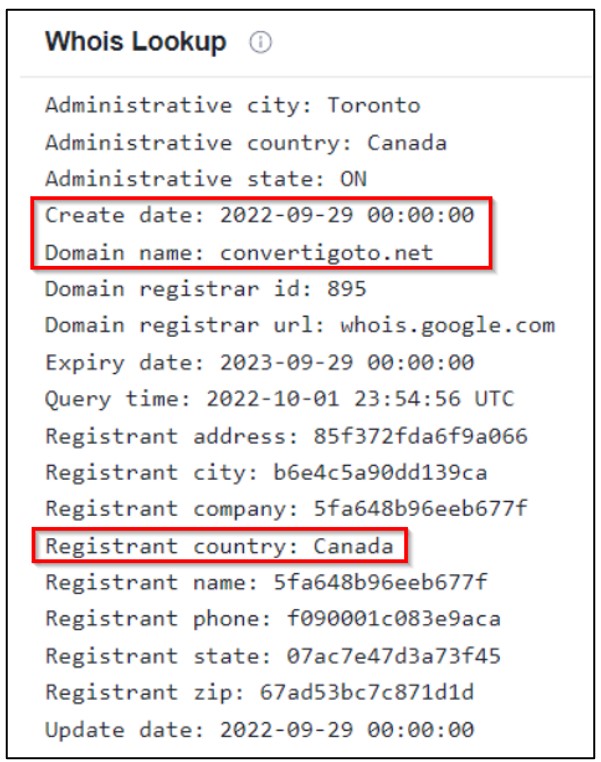
The below figure shows the “Whois” information of the phishing domain, indicating that the domain has been registered recently and has been actively targeting users of online file conversion tools.
Technical Details
When users visit the phishing page, the online tool prompts them to choose the input file that needs to be converted to another file type, as shown below.

Once the file is chosen, the tool allows the users to select a target file extension for conversion, as shown below.

After selecting the file type and clicking the “Convert” button present on the page, users are redirected to the download page and shown the “download” button to get their converted file. The actual infection starts when the user clicks on the “download” button present in the phishing site, which downloads a zip archive file – “YourConvertedFile634643.zip” – as shown below.

The zip archive contains a shortcut file, “YourConvertedFile.lnk,” instead of the actual file type that the user selected for conversion. The below figure shows the extracted shortcut file from the downloaded zip file along with its target command line.

Upon execution of the shortcut file, it downloads two BAT files named “2.bat” & “3.bat” into the “%USERPROFILE%\Downloads” directoryfrom the following URLs using “curl executable” and launches the “3.bat” batch file:
- hxxps[:]//convertigoto[.]net/cc/flesd/3[.]bat
- hxxps[:]//convertigoto[.]net/cc/flesd/2[.]bat
The content of the “3.bat” batch file is shown below.

Once the “3.bat” batch file is launched, it runs the below PowerShell commands to add the file extensions (“exe” & “bat”) and drive path (“C:”) to the exclusion list of Windows Defender.
- PowerShell – WindowStyle Hidden Add-MpPreference -ExclusionExtension “exe”
- PowerShell – WindowStyle Hidden Add-MpPreference -ExclusionExtension “bat”
- PowerShell – WindowStyle Hidden Add-MpPreference -ExclusionPath “C:”
Then, “3.bat” further downloads an executable payload which has a PDF file icon and is named “YourConvertedFile59417.exe” from the below URL using “curl executable” and executed after renaming it to “1.exe”:
- hxxps[:]//convertigoto[.]net/cc/flesd/YourConvertedFile59417[.]exe
The below figure shows the process tree of shortcut file downloads from the phishing site.

The behavior of the executable indicates that the payload is a known malware strain called “RedLine Stealer.” Redline Stealer is a piece of malware written in C# and uses a SOAP API to communicate with its C&C (Command-and-Control) server. This stealer is capable of stealing information from web browsers, cryptocurrency wallets, and applications such as FileZilla, Discord, Steam, Telegram, and VPN clients.
It also collects information about the infected machine, such as OS, system hardware, running processes, antivirus products, installed programs, and system language. After collecting the victim’s information, it exfiltrates all the stolen details to the remote C&C server.
This malware can also upload and download files, execute commands, and periodically send information about the infected computer to the C&C server. You can read CRIL’s in-depth analysis of the Redline stealer blog here.
Conclusion
Online tools are widely used for professional and personal uses because of their highlights, such as convenience, accessibility, feasibility, and ease of operation. TAs often target web applications with a wide user base or audience. They create a phishing website that looks similar to a genuine website to lure their victims into downloading malware.
In this particular case, the TA created a fake file converter phishing website to deliver RedLine malware payload since many users leverage the online converter tool to convert files for day-to-day work. RedLine Stealer malware stands out in the stealer family because of its rich and diverse capabilities. Additionally, the TA behind RedLine Stealer is active and selling this under the Malware as a Service (MaaS) model.
Cyble Research and Intelligence Labs (CRIL) continuously monitors phishing campaigns and malicious attacks, whether they are ongoing or emerging. We will continue to update our readers with our latest findings and analysis.
Our Recommendations
- Avoid downloading pirated software from Warez/Torrent websites. The “Hack Tool” present on sites such as YouTube, Torrent sites, etc., contains such malware.
- Use strong passwords and enforce multi-factor authentication wherever possible.
- Turn on the automatic software update feature on your computer, mobile, and other connected devices.
- Use a reputed antivirus and internet security software package on your connected devices, including PC, laptop, and mobile.
- Refrain from opening untrusted links and Email attachments without first verifying their authenticity.
- Educate employees on protecting themselves from threats like phishing attacks and untrusted URLs.
- Block URLs that could be used to spread the malware, e.g., Torrent/Warez.
- Monitor the beacon on the network level to block data exfiltration by malware or TAs.
- Enable Data Loss Prevention (DLP) Solutions on the employees’ systems.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566 | Phishing |
| Execution | T1204 T1064 T1059 T1047 | User Execution Scripting PowerShell Windows Management Instrumentation |
| Privilege Escalation | T1055 | Process Injection |
| Defense Evasion | T1562 T1497 | Disable or Modify Tools Virtualization/Sandbox Evasion |
| Credential Access | T1003 | OS Credential Dumping |
| Discovery | T1057 T1082 T1518 | Process Discovery System Information Discovery Security Software Discovery |
| Collection | T1005 | Data from Local System |
| Command and Control | T1071 T1573 T1105 | Application Layer Protocol Encrypted Channel Ingress Tool Transfer |
Indicators of Compromise (IOCs)
| Indicators | Indicator Type | Description |
| 0350d40da8135fe9c8c61a939602dedd 6e30860d6b5c6348d7143f74b2ad734eee716da3 1089a26c46bb0e5a247593e5defd80503dc0d4950ee522f1de54fca99b1c21f6 | MD5 SHA1 Sha256 | Zip file |
| 8be13313460c5f1befb20a1051f9f850 9e1dafcd668cb89d82ae85806d5b67f54509cb55 f74b170a7f8258bc8824f0f5efad26e8081f793cc1c4d5282a5fcc43c3d71368 | MD5 SHA1 Sha256 | LNK file |
| 209b97fe681f86b71162153b4ddbce32 18ddf2b3f414a970cc3915dc69b8d06eff55d4da 70f56299a49fdb0994adfff42b3d4b74f7036193d8a783ee8223180bf0b30bed | MD5 SHA1 Sha256 | BAT file “3.bat” |
| 303c63a7c8d3b15c72e079e720fc4ae4 9dac60afed2565c94ed3e1716032a9d989f82307 eb7d31a5a641b057aa250442dc5252d4214ca282632ebd24a79644fe358fbe18 | MD5 SHA1 Sha256 | Exe file |
| hxxps[:]//convertigoto[.]net/ | URL | Phishing site |
| hxxps[:]//convertigoto[.]net/cc/flesd/3[.]bat | URL | Malware distribution URL |
| hxxps[:]//convertigoto[.]net/cc/flesd/2[.]bat | URL | Malware distribution URL |
| hxxps[:]//convertigoto[.]net/cc/flesd/YourConvertedFile59417[.]exe | URL | Malware distribution URL |