Insights into Onyx Ransomware’s recent Operations
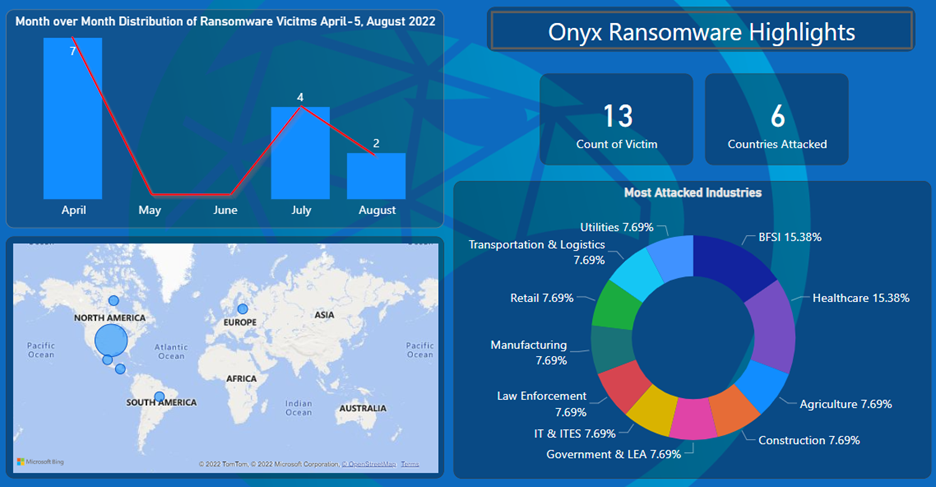
Onyx ransomware was initially identified by researchers in mid-April 2022. The ransomware group uses the double extortion technique to target its victims where it exfiltrates the victim’s data, then encrypts it. If the victim cannot pay the ransom, then Threat Actors (TA) leak the victim’s data on their leak site. The group has a total of 13 victims from 6 different countries to date. The United States remains the most targeted country, with over 60% of the total victims.
According to researchers, Onyx ransomware is based on Chaos ransomware. Onyx encrypts files smaller than 2MB and overwrites files larger than 2MB, rendering them unrecoverable. The figure below shows the highlights of the activities of Onyx ransomware.
Onyx is a .NET-based ransomware. This ransomware, upon successful execution, encrypts the files with the “.ampkcz” extension and drops a ransom note named “readme.txt.”
This note contains instructions given by the TA to recover encrypted files and details of the communication medium. The figure below shows the TA’s message to the victim.

Recent Activities
By the end of April 2022, the Onyx ransomware group had posted details of 7 victims on their leak site. During our research, we found that one of the Onyx ransomware victims was also posted as a victim on the Conti ransomware leak site on 4 April 2022. It is possible that the same victim was attacked twice. But if we heed the sequence of events, the victim was first posted by Conti ransomware, followed by Onyx ransomware.
Conti Ransomware was expected to shut down its operations at that time, which indicates the possibility that Conti’s affiliates/members might be behind Onyx ransomware or may have collaborated to execute this attack.
After announcing 7 victims in April, the Onyx group went silent for nearly two months on their leak site and restarted their operations by July end. The figure below shows the common victim details posted by Onyx and Conti ransomware.

During our Ransomware research and monitoring activities, we found that the ONYX ransomware had renamed its leak site from “ONYX NEWS” to “VSOP NEWS.” The group has not launched a new site but updated the existing site with new names. The figure below compares the old and new ONYX ransomware leak sites.

Technical Analysis
(Sample SHA256: a7f09cfde433f3d47fc96502bf2b623ae5e7626da85d0a0130dcd19d1679af9b)
Onyx ransomware uses AES and RSA encryption algorithms to encrypt the victim’s files. The ransomware targets the following directories for encryption:
- Desktop
- Links
- Contacts
- Documents
- Downloads
- Pictures
- Music
- OneDrive
- Saved Games
- Favorites
- Searches
- Videos
Onyx ransomware encrypts files that have the following extensions:
.txt, .jar, .dat, .contact, .settings, .doc, .docx, .xls, .xlsx, .ppt, .pptx, .odt, .jpg, .mka, .mhtml, .oqy, .png, .csv, .py, .sql, .mdb, .php, .asp, .aspx, .html, .htm, .xml, .psd, .pdf, .xla, .cub, .dae, .indd, .cs, .mp3, .mp4, .dwg, .zip, .rar, .mov, .rtf, .bmp, .mkv, .avi, .apk, .url, .dib, .dic, .dif, .divx, .iso, .7zip, .ace, .arj, .bz2, .cab, .gzip, .lzh, .tar, .jpeg, .xz, .mpeg, .torrent, .mpg, .core, .pdb, .ico, .pas, .db, .wmv, .swf, .cer, .bak, .backup, .accdb, .bay, .p7c, .exif, .vss, .raw, .m4a, .wma, .flv, .sie, .sum, .ibank, .wallet, .css, .js, .rb, .crt, .xlsm, .xlsb, .7z, .cpp, .java, .jpe, .ini, .blob, .wps, .docm, .wav, .3gp, .webm, .m4v, .amv, .m4p, .svg, .ods, .bk, .vdi, .vmdk, .onepkg, .accde, .jsp, .json, .gif, .log, .gz, .config, .vb, .m1v, .sln, .pst, .obj, .xlam, .djvu, .inc, .cvs, .dbf, .tbi, .wpd, .dot, .dotx, .xltx, .pptm, .potx, .potm, .pot, .xlw, .xps, .xsd, .xsf, .xsl, .kmz, .accdr, .stm, .accdt, .ppam, .pps, .ppsm, .1cd, .3ds, .3fr, .3g2, .accda, .accdc, .accdw, .adp, .ai, .ai3, .ai4, .ai5, .ai6, .ai7, .ai8, .arw, .ascx, .asm, .asmx, .avs, .bin, .cfm, .dbx, .dcm, .dcr, .pict, .rgbe, .dwt, .f4v, .exr, .kwm, .max, .mda, .mde, .mdf, .mdw, .mht, .mpv, .msg, .myi, .nef, .odc, .geo, .swift, .odm, .odp, .oft, .orf, .pfx, .p12, .pl, .pls, .safe, .tab, .vbs, .xlk, .xlm, .xlt, .xltm, .svgz, .slk, .tar.gz, .dmg, .ps, .psb, .tif, .rss, .key, .vob, .epsp, .dc3, .iff, .onepkg, .onetoc2, .opt, .p7b, .pam, .r3d, .dsn, .dmp, .qbw, .imr, .nd, .chw, .spi, .ep, .tlg, .qbb, .msi, .eml, .thmx, .obi, .chm, .pub, .md5, .spf, .spk, .idx, .scc, .jdk, .cnt, .tum, .dsm, .reg, .cfg, .ldf, .bat, .dxf, .SLDDRW, .SLDPRT, .SLDASM, .mil, .dlf, .c4, .pdx
If the size of files with the extensions mentioned above is larger than 2MB, the ransomware destroys the files by overwriting them with random data, making them forever inaccessible.

The ransomware has hardcoded strings such as Ransom note, an extension for appending the encrypted files, and the file name of Ransom Note. The ransomware appends the “.ampkcz” extension to all the encrypted files and drops a ransom note named “readme.txt.” The figure below shows the hardcoded strings.

This ransomware also deletes the volume shadow copies and backup catalogs to prevent the recovery of the victim’s data. Additionally, it modifies the registry’s RunOnce key and creates a shortcut file to establish persistence. It also tries to spread by checking the mounted drives on the victim’s system, as shown in the figure below.

Conclusion
Cyble Research Labs actively monitors emerging ransomware threats. Onyx ransomware updated its leak and renamed it after two months of inactivity.
It is possible that ransomware groups might be trying to restart their malicious activities, as previously, researchers discovered that due to a flaw, the ransomware was destroying files above 2MB during encryption, which might lead to a loss in the ransom earned.
A fresh sample of Onyx ransomware hasn’t been spotted in the wild until now, but we suspect, based on the above assumptions, that TAs might also upgrade the ransomware executable.
Our Recommendations
With Threat Actors and their TTPs increasing in sophistication, the industry is still searching for the proverbial silver bullet to counter this cyber threat. However, there are a few cybersecurity measures that we strongly recommend to organizations to reduce the likelihood of a successful attack:
- Victim organizations should perform incident response activities to minimize the losses and mitigate the exploited vulnerabilities.
- Deploy reputed anti-virus and internet security software package on your company-managed devices, including PCs, laptops, and mobile devices.
- Define and implement a backup process and secure those backup copies by keeping them offline or on a separate network.
- Enforce password change policies for the network and critical business applications or consider implementing multi-factor authentication for all remote network access points.
- Reduce the attack surface by ensuring that sensitive ports are not exposed to the Internet.
- Conduct cybersecurity awareness programs for employees and contractors.
- Implement a risk-based vulnerability management process for IT infrastructure to identify and prioritize critical vulnerabilities and security misconfigurations for remediation.
- Instruct users to avoid opening untrusted links and email attachments without verifying their authenticity.
- Turn on the automatic software update features on computers, mobiles, and other connected devices wherever possible and pragmatic.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Execution | T1106 | Native API |
| Persistence | T1547.001 | Boot or Logon AutoStart Execution: Registry Run Keys / Startup Folder |
| Discovery | T1082 T1083 | System Information Discovery File and Directory Discovery |
| Impact | T1486 | Data Encrypted for Impact |
Indicators of Compromise
| Indicators | Indicator type | Description |
| cf6ff9e0403b8d89e42ae54701026c1f a4f5cb11b9340f80a89022131fb525b888aa8bc6 a7f09cfde433f3d47fc96502bf2b623ae5e7626da85d0a0130dcd19d1679af9b | MD5 SHA-1 SHA256 | Ransomware payload |




















