Sodinobiki operators have been lately quite busy in targeting large organizations, such as JN Bank, Gaiedi.com, Brooks International and many others.
This time they have targeted a non-profit organization, National Eating Disorders Association (NEDA), headquartered in the US. According to the Wikipedia (which we know is not the most reliable place to research!), the organization devoted to preventing eating disorders, providing treatment referrals, and increasing the education and understanding of eating disorders, weight, and body image. The National Eating Disorders Association organizes and sponsors National Eating Disorders Week. Also known as NEDAwareness Week, it takes place during the last week of February, and is “a collective effort of primary volunteers, including eating disorder professionals, health care providers, students, educators, social workers, and individuals committed to raising awareness of the dangers surrounding eating disorders and the need for early intervention and treatment.
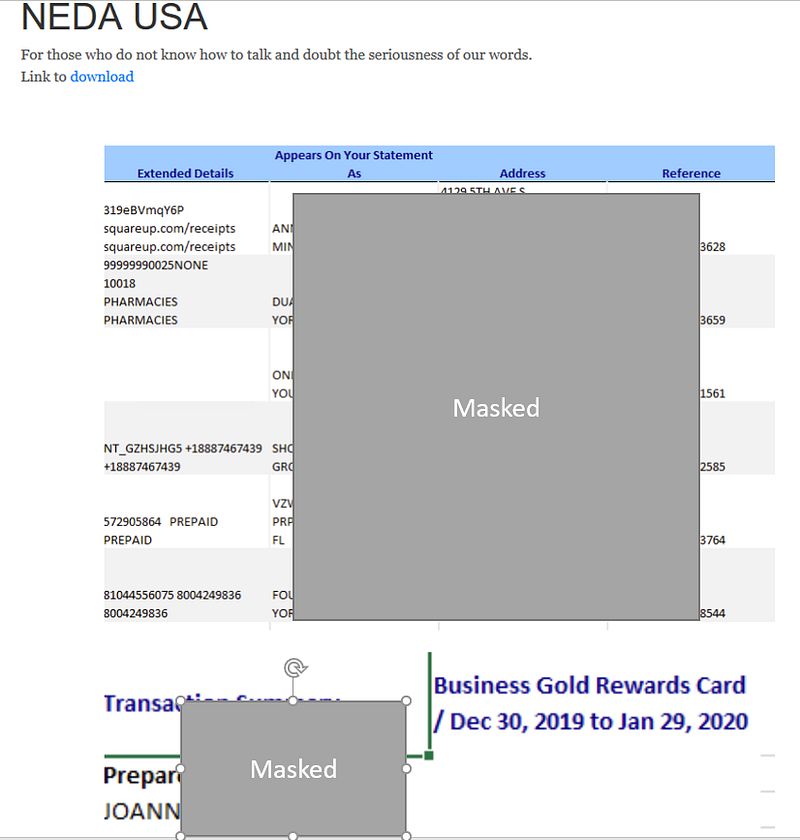
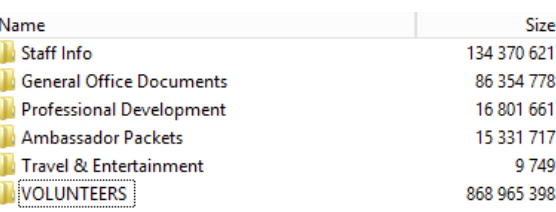
The ransomware operators have shared the screenshots of the files they have been able to gain access, and are threatening to release them should the ransom payment is not made.
Update: April 4 — The ransomware operators have leaked the files of the company.




About Cyble:
Cyble Inc.’s mission is to provide organizations with a real-time view of their supply chain cyber threats and risks. Their SaaS-based solution powered by machine learning and human analysis provides organizations’ insights to cyber threats introduced by suppliers and enables them to respond to them faster and more efficiently.
Cyble strives to be a reliable partner/facilitator to its clients allowing them with unprecedented security scoring of suppliers through cyber intelligence sourced from open and closed channels such as OSINT, the dark web and deep web monitoring and passive scanning of internet presence. Furthermore, the intelligence clubbed with machine learning capabilities fused with human analysis also allows clients to gain real-time cyber threat intel and help build better and stronger resilience to cyber breaches and hacks. Due to the nature of the collected data, the company also offer threat intelligence capabilities out-of-box to their subscribers.





















