They Manage the Surface. We Redefine Intelligence. Try Cyble Today
Recognized by Forrester & Gartner for External Attack Surface Management and Extended Threat Intelligence. Powered by Agentic AI
SocRadar offers visibility — but visibility without depth is just noise.
Cyble delivers the full spectrum of cyber intelligence, combining threat detection, dark web monitoring, ransomware tracking, vulnerability intelligence, and digital risk protection into one AI-native ecosystem.
Where SocRadar stops at monitoring, Cyble translates intelligence into action — empowering enterprises to predict, prevent, and respond faster.
Schedule a Personalized Demo
See Why Leading Enterprises Choose Cyble Over SOCRadar
See how Cyble’s unified cyber intelligence ecosystem goes beyond conventional monitoring.
The table below highlights how Cyble delivers broader coverage, deeper visibility, and AI-powered automation across threat intelligence, digital risk protection, and attack surface management — setting a new standard for comprehensive cybersecurity.
| Capability |

|
SOCRadar |
|---|---|---|
| Threat Feeds & IOC Management (STIX 2.0+) | ||
| IOC Whitelisting & Enrichment | ||
| Phishing Intelligence | ||
| DDoS Attackers Tracking | ||
| Threat Actor Monitoring & Infrastructure Mapping | ||
| News & Advisory Monitoring | ||
| Vulnerability Intelligence & Risk Scoring | ||
| Vendor / Third-Party Monitoring | ||
| Threat Hunting Rules (SIGMA & YARA) | ||
| Malicious Hash & Suspicious IP Tracking | ||
| Malware Analysis / Sandboxing / Reverse Engineering | ||
| Threat Actor Engagement & Ransomware Negotiation | ||
| HoneyPot / Sensor Intelligence Network | ||
| Intelligence from Stealer Marketplaces | ||
| Analyst Interaction & Investigation Support |
Cyble Advantage
Unmatched threat intelligence coverage — combining actor tracking, ransomware group mapping, malware analysis, and dark web telemetry into a single operational intelligence framework.
| Capability |

|
SOCRadar |
|---|---|---|
| Employee / Customer Account Leak Detection | ||
| VIP / Executive Monitoring | ||
| Credit Card Leak Monitoring | ||
| Typosquat & Phishing Domain Detection | ||
| Deep & Dark Web Monitoring (forums, marketplaces, stealer logs) | ||
| Source Code Leakage (GitHub, paste sites, repos) | ||
| Rogue / Fake Mobile Apps Detection (brand misuse) | ||
| Brand Keyword / Logo / Image Monitoring | ||
| Social Media Account Tracking & Impersonation | ||
| Black Market Credential Sale Detection | ||
| Mobile App Risk Detection | ||
| Breach Data Detection (PII exposure) | ||
| Compromised Endpoint Detection | ||
| Surface Web Exposure Monitoring | ||
| Takedown Services (automated + analyst) | ||
| Supply Chain Monitoring & Risk Scoring | ||
| Incident Response Playbooks / Automation |
Cyble Advantage
Real-time visibility across open, deep, and dark web channels with automated takedown orchestration and global analyst support.
| Capability |

|
SOCRadar |
|---|---|---|
| Automated Asset Discovery (Shadow IT) | ||
| Network Security Configuration Monitoring | ||
| SSL Certificate Monitoring / Grading | ||
| DNS Infrastructure Monitoring (DNS, WHOIS, DMARC, SPF, DKIM, BIMI) | ||
| Cloud Bucket Analysis (S3 / Azure / GCP) | ||
| Vulnerability Detection & Prioritization (Zero-Day, OWASP Top 10) | ||
| Critical Port Detection | ||
| Application Security Assessment (OWASP Top 10) | ||
| Asset Change Tracking & Risk Scoring | ||
| Subdomain Takeover Detection | ||
| Website Monitoring / Tamper Detection | ||
| Continuous & Manual Vulnerability Scanning | ||
| IP / Domain Reputation Monitoring |
Cyble Advantage
End-to-end visibility across the digital perimeter with continuous AI-driven exposure analysis, vulnerability prioritization, and exploit correlation.
| Capability |

|
SOCRadar |
|---|---|---|
| SIEM / SOAR / TIP Integrations (Splunk, QRadar, Cortex, LogRhythm, etc.) | ||
| API Integration & Notifications | ||
| Custom Dashboards & Executive Reports | ||
| On-demand Analyst Services & Custom Reports | ||
| Named Threat Intelligence Analyst Support | ||
| Ransomware Negotiation / Actor Engagement | ||
| Integrated Takedown Team (Global) | ||
| Incident Response Workflows & Playbooks |
Cyble Advantage
Enterprise-grade integrations and dedicated threat intelligence teams that extend customer SOC capabilities with actionable, analyst-backed intelligence.
*Information gathered from various sources and subject to change based on product innovations.
See What Industry Veterans Have to Say About Us
Hear from cybersecurity experts and industry leaders who trust Cyble to deliver cutting-edge threat intelligence solutions. Discover how we help organizations stay ahead of cyber threats with innovative technology and unmatched expertise.
| Area | Cyble Edge |
|---|---|
| Coverage | Unified CTI + DRP + ASM + Cloud + Endpoint + CRQ visibility across surface, deep, dark web, and supply chain. |
| Data Depth | Proprietary crawlers across 20,000+ dark-web forums, Telegram channels, and stealer marketplaces. |
| Automation | AI/ML-driven risk scoring, exposure ranking & auto-takedown workflows. |
| Human Intelligence | 24×7 global research team validating and enriching machine findings. |
| Integrations | Broad connectivity with SIEM, SOAR, TIP, and API pipelines. |
| Compliance | ISO 27001 & SOC 2 certified infrastructure ensuring trusted operations. |
Jira
Splunk
Cortex (Cyble Events V2)
Cortex (Cyble Threat Intel)
Fortinet
Sentinel
LogRhythm
RSA
Securonix
Cyware
QRadar (Cyble Events V2)
QRadar (Cyble Threat Intel)
ServiceNow
Slack
SMS
OpenAPI
MISP
Splunk
Cortex (Cyble Events V2)
Cortex (Cyble Threat Intel)
Fortinet
Sentinel
LogRhythm
RSA
Securonix
QRadar (Cyble Events V2)
QRadar (Cyble Threat Intel)
Splunk
Cortex (Cyble Events V2)
Cortex (Cyble Threat Intel)
Fortinet
Sentinel
Cyware
QRadar (Cyble Events V2)
QRadar (Cyble Threat Intel)
ServiceNow
Jira
ServiceNow
MISP
Slack
SMS
OpenAPI
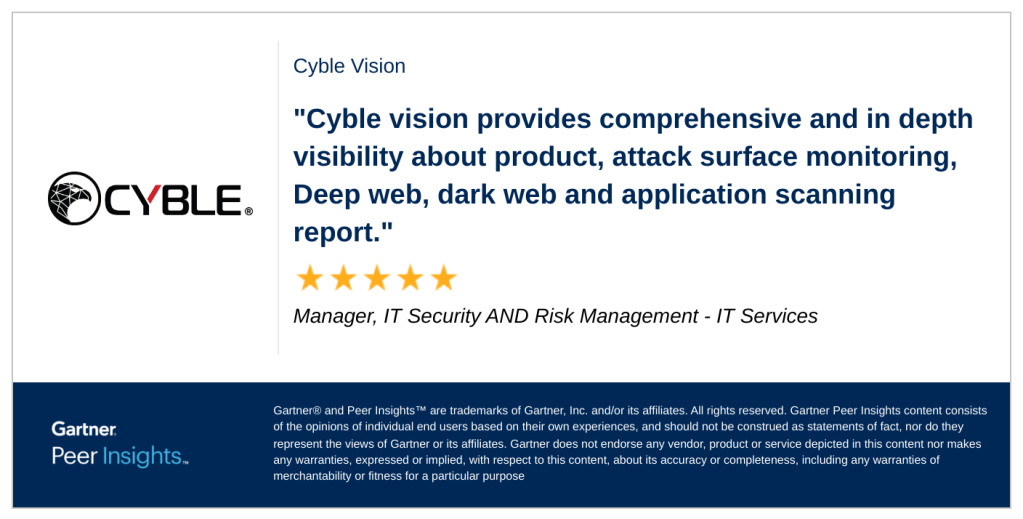
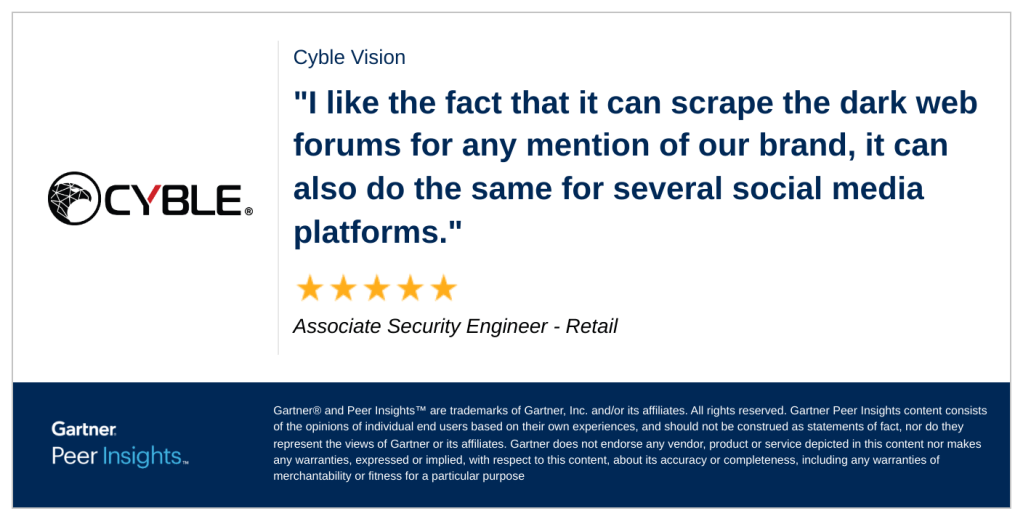
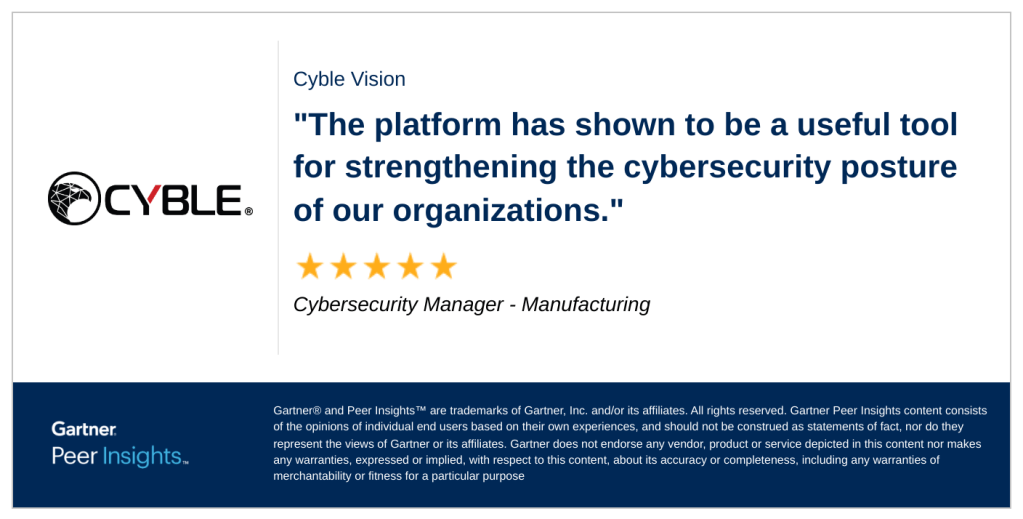
What customers say about Cyble
From Real Users on Gartner Peer Insights







DidYouKnow?
Cyble Visionis the fastest growing and most loved threat intelligence platformIn the Industry
Experience the Cyble Difference
See Cyble in action — experience real-time threat actor tracking, exposure detection, and automated remediation powered by Cyble’s AI-native intelligence platform.