Threat Actors Target Multiple Sectors in Wide-Ranging Attacks
Ransomware poses a significant risk to cybersecurity and remains a highly successful form of cybercrime that presents serious challenges for organizations. It has emerged as a lucrative enterprise for cybercriminals, leading to profound implications, including financial and data losses, as well as detrimental effects on the reputation of the organizations targeted.
Cyble Research and Intelligence Labs (CRIL) have recently shared crucial details about the activities of a newly identified ransomware group known as “Akira.” This group is actively targeting numerous organizations, compromising their sensitive data. It is worth noting that Akira ransomware has expanded its operations to include the Linux platform. CRIL came across a sophisticated Linux variant of the Akira ransomware.
Since its emergence in April 2023, Akira ransomware has already compromised 46 publicly disclosed victims, with an additional 30 victims identified since our previous blog post. The majority of these victims are located in the United States. Here is a breakdown of the countries where the victims have been identified.

The Akira ransomware specifically targeted a wide range of industries during its attacks, encompassing sectors including Education, Banking, Financial Services and Insurance (BFSI), Manufacturing, Professional Services, and more.
The figure below shows industries targeted by the Akira ransomware.

Technical Details
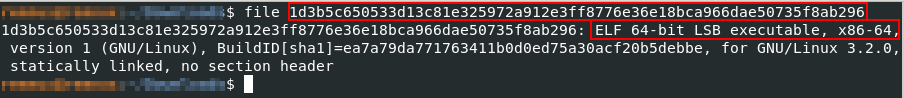
The malicious Linux executable is a 64-bit Linux Executable and Linkable Format (ELF) file with SHA256 as 1d3b5c650533d13c81e325972a912e3ff8776e36e18bca966dae50735f8ab296.
In order to execute the Akira executable, specific parameters need to be provided. The required parameters for running the Akira executable are as follows:
- “-p” / “–encryption_path” – Path of files/folder to be encrypted.
- “-s” / “–share_file” – Path of the shared network drive to be encrypted
- “-n” / “–encryption_percent” – Percentage of the files to be encrypted.
- “-fork” – Creating a child process for encryption.

Upon execution, the Akira ransomware loads a pre-determined RSA public key to encrypt files in the system.
The figure below presents the hardcoded public key utilized by the Akira ransomware.

Following the initialization of the public key, the Akira ransomware loads a list of predetermined file extensions that it intends to target and encrypt.
The figure below illustrates the file extensions that are specifically targeted by the Akira ransomware.

The table provided below encompasses a comprehensive list of the file extensions targeted by Akira ransomware.
| vdi | vhd | vmdk | pvm | vmem | vmsn | vmsd | nvram |
| vmx | raw | qcow2 | subvo | bin | vsv | avhd | vmrs |
| vhdx | avdx | vmcx | iso | mar | odb | scx | wdb |
| 4dd | cma | dqy | frm | mas | oqy | sdb | wmdb |
| accdb | cpd | dsk | gdb | mav | orx | sdc | wrk |
| accdc | dacpac | dsn | grdb | mdb | owc | sdf | xdb |
| accde | dad | dtsx | gwi | mdf | p96 | sis | xld |
| accdr | dadiagrams | eco | hdb | mpd | p97 | spq | xmlff |
| accdt | daschema | ecx | his | mrg | pan | sqlite | abcddb |
| accft | db-shm | edb | idb | mud | pdb | sqlite3 | abs |
| adb | db-wa | epim | ihx | mwb | pdm | sqlitedb | abx |
| ade | db3 | exb | itdb | myd | pnz | temx | accdw |
| adf | dbc | fcd | itw | ndf | qry | tmd | adn |
| adp | dbf | fdb | jet | nnt | qvd | tps | db2 |
| arc | dbs | fic | jtx | nrmlib | rbf | trc | fm5 |
| ora | dbt | fmp | kdb | ns2 | rctd | trm | hjt |
| alf | dbv | fmp12 | kexi | ns3 | rod | udb | icg |
| ask | dbx | fmps | kexic | ns4 | rodx | usr | icr |
| btr | dcb | fp3 | kexis | nsf | rpd | v12 | kdb |
| bdf | dct | fp4 | lgc | nv2 | rsd | vis | lut |
| cat | dcx | fp5 | lwx | nwdb | sas7bdat | vpd | maw |
| cdb | dlis | fp7 | maf | nyf | sbf | vvv | mdn |
| ckp | dp1 | fpt | maq | mdt | |||
The ransomware incorporates routines associated with multiple symmetric key algorithms, including AES, CAMELLIA, IDEA-CB, and DES. When encountering a file with an extension listed in the previously mentioned extensions, the ransomware proceeds to encrypt the file.
The image below illustrates the routine specifically implemented for AES encryption within the ransomware.

Next, to successfully encrypt the files, the ransomware adds the “.akira” file extension to each compromised file and deposits a pre-defined ransom note onto the victim’s system.
The figure below displays the exact contents of the ransom note, which have been hardcoded into the ransomware.

Conclusion
Akira Ransomware, which was initially focused on Windows systems, has now expanded its target range to include Linux platforms. This shift in tactics reflects a growing trend among ransomware groups, indicating an upcoming surge in attacks targeting Linux environments. The fact that a previously Windows-centric ransomware group is now turning its attention to Linux underscores the increasing vulnerability of these systems to cyber threats.
CRIL maintains vigilant monitoring of emerging ransomware campaigns to ensure our readers are well-informed, providing regular updates on our latest discoveries.
Our Recommendations
We have listed some essential cybersecurity best practices that create the first line of control against attackers. We recommend that our readers follow the best practices given below:
Safety Measures Needed to Prevent Ransomware Attacks
- Conduct regular backup practices and keep those backups offline or in a separate network.
- Turn on the automatic software update feature on your computer, mobile, and other connected devices wherever possible and pragmatic.
- Use a reputed anti-virus and Internet security software package on your connected devices, including PC, laptop, and mobile.
- Refrain from opening untrusted links and email attachments without verifying their authenticity.
Users Should Take the Following Steps After the Ransomware Attack
- Detach infected devices on the same network.
- Disconnect external storage devices if connected.
- Inspect system logs for suspicious events.
Impact of Akira Ransomware
- Loss of valuable data.
- Loss of the organization’s reputation and integrity.
- Loss of the organization’s sensitive business information.
- Disruption in organization operation.
- Financial loss.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Execution | T1204 | User Execution |
| Discovery | T1082 T1083 | System Information Discovery File and Directory Discovery |
| Impact | T1486 T1490 | Data Encrypted for Impact Inhibit System Recovery |
Indicators of Compromise (IOCs)
| Indicators | Indicator Type | Description |
| 302f76897e4e5c8c98a52a38c4c98443 9180ea8ba0cdfe0a769089977ed8396a68761b40 1d3b5c650533d13c81e325972a912e3ff8776e36e18bca966dae50735f8ab296 | MD5 SHA1 SHA256 | Akira Ransomware ELF |








