Another Leak Associated with a prominent Ransomware Group
Cyble Research and Intelligence Labs (CRIL) came across a newly registered Twitter user claiming that their team managed to hack several LockBit servers and acquired a builder of LockBit 3.0 ransomware, also known as “LockBit Black”. This user has leaked the alleged builder for free on Twitter.
LockBit is the most active ransomware group and has over 1000 publicly disclosed victims to date. This ransomware group has evolved quickly and is currently operating version 3.0.
LockBit ransomware operates on a Ransomware-as-a-Service model where the developer leases out their application to affiliates in return for a certain percentage of the ransom earnings.
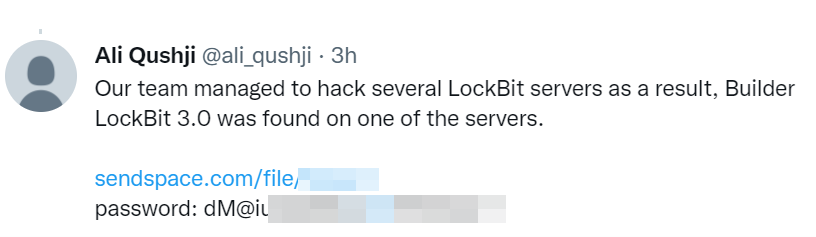
The user posted multiple replies on various ransomware-related posts on Twitter and shared the download link of the LockBit builder. The user appears to have joined Twitter recently, and it is possible that this account was created for the express purpose of leaking the LockBit ransomware builder.

The leaked zip file contains a folder named “Build,” two executables, one batch, and one JSON file, as shown in the below figure. The builder does not have a Graphical User Interface (GUI) and executes via batch file.

The execution workflow is as follows:
- The “Build.bat” file executes “keygen.exe” and “builder.exe.”
- “Keygen.exe” is used to generate cryptographic keys.
- “Builder.exe” creates the payload, decryptor, .txt, and other DLL files and saves them to a folder named “Build”.
The figure below shows the files generated by “builder.exe”

“Builder.exe” uses the “config.json” file to customize the payload as per the Threat Actor’s (TAs) requirement. The configuration file contains various features such as encrypt_mode, encrypt_filename, impersonation, etc.
Additionally, the TAs can define files, folders, and extension names to be excluded from the encryption process. The language check can also be enabled in the config file to exclude CIS (Commonwealth of Independent States) countries.
Apart from these, the configuration file also contains a ransom note. The figure below shows the configuration file.

We tested both the ransomware payload and decryptor generated using the builder. The binary was able to encrypt files, and the decryption process was successful using the decryptor. The below figure shows the ransomware encryption and decryption phases.

Conclusion
The profile behind this leak has not mentioned anything regarding the intent behind the leak. Such leaks can result in the emergence of new Threat Groups, as they can modify leaked files to carry out attacks.
Cyble Research and Intelligence Labs has witnessed a similar incident in the past when the internal data of the Conti ransomware group was leaked on Twitter. This incident is in the initial stage, and it is not yet certain how it might evolve.
Our Recommendations
With Threat Actors and their TTPs increasing in sophistication, the industry is still searching for the proverbial silver bullet to counter this cyber threat. However, there are a few cybersecurity measures that we strongly recommend to organizations to reduce the likelihood of a successful attack:
- Define and implement a backup process and secure those backup copies by keeping them offline or on a separate network
- Enforce password change policies for the network and critical business applications or consider implementing multi-factor authentication for all remote network access points
- Reduce the attack surface by ensuring that sensitive ports are not exposed to the Internet
- Conduct cybersecurity awareness programs for employees and contractors
- Implement a risk-based vulnerability management process for IT infrastructure to ensure that critical vulnerabilities and security misconfigurations are identified and prioritized for remediation
- Instruct users to refrain from opening untrusted links and email attachments without verifying their authenticity
- Deploy reputed anti-virus and internet security software package on your company-managed devices, including PCs, laptops, and mobile devices
- Turn on the automatic software update features on computers, mobiles, and other connected devices wherever possible and pragmatic
- Monitor darkweb activities for early indicators and threat mitigation.








