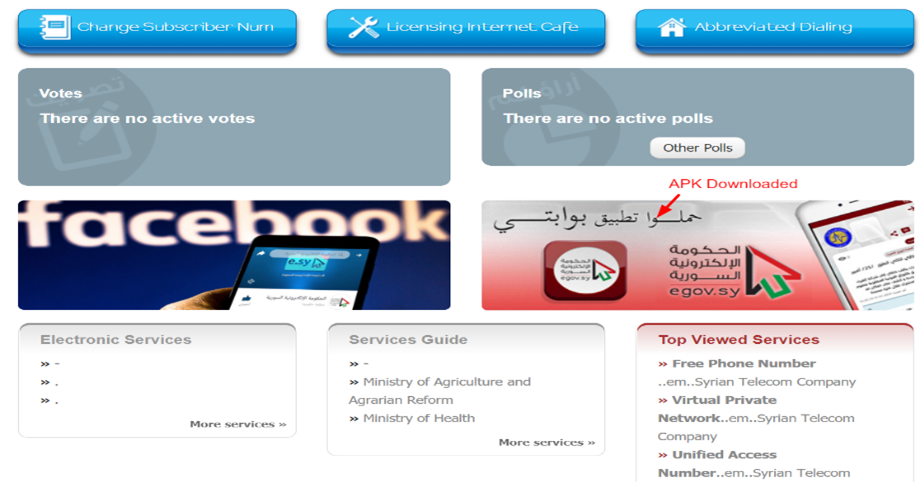
In a recent tweet, security researchers spoke about a Trojanized version of a Syrian E-government android app available from the e-gov web portal. Our investigation indicated that this malware campaign targets Syria and its surrounding countries struggling with the ongoing onslaught of the COVID-19 pandemic. We discovered that once installed, this app collects victim’s data such as contact lists and uploads selective file types from the user’s device to their C2 link. In our search to find the source of the app, we discovered that the site from where the APK file has been downloaded is the official government site which links to governmental organizations that provide services to people, as shown in Figure 1.

Figure 1 Objective details of the website
On downloading the APK file from their official website, we saw that the file gets downloaded directly from the website to the user machine without redirecting users to any official app stores, as shown in the image below.

Figure 2 Source of the APK downloaded from the Website
On finding the source link of the file from where the APK is downloaded, we observed that the website has a Directory Traversal vulnerability, enabling us to see the earlier versions of the APK files, as shown in Figure 3.

Figure 3 Earlier version of APK files found from the website server
On comparing the latest version of the APK file with the old version hosted on their website and scanning it through VirusTotal, we found the old version to be clean. The latest version was found to be a Spyware variant with the inclusion of multiple permissions and services.
Following are the snippets of the comparison:
- VirusTotal
Old Version:

Figure 4 VirusTotal Result for Old Version APK file
Latest Version:

Figure 5 VirusTotal Result of New Version APK file
- Permission and Services
Earlier Version:

Figure 6 Permissions and Services used in Old Version
New Version:

Figure 7 Permissions and Services Used in Latest Version
Technical Analysis:
Digest used for our analysis: fd1aac87399ad22234c503d8adb2ae9f0d950b6edf4456b1515a30100b5656a7
Package Name: com.egov.app
Main Activity: com.egov.app.ui.SplashActivity
As per our analysis, we found that the malicious application under the latest version includes many permissions and services, as shown in Figure 7. Some of the list of malicious permissions, services and receivers observed from the APK file have been listed below:
Permissions:
- android.permission.ACCESS_FINE_LOCATION
- android.permission.CHANGE_WIFI_STATE
- android.permission.READ_PHONE_STATE
- android.permission.WRITE_EXTERNAL_STORAGE
- android.permission.INTERNET
- android.permission.READ_CONTACTS
Services:
- com.egov.app.NetworkStatusService
Receivers:
- com.egov.app.Receiver
- com.egov.app.UserPresentHandler
Intent Filters by Action:
- android.intent.action.MAIN
- android.intent.action.BOOT_COMPLETED
- android.intent.action.BATTERY_LOW
- android.intent.action.USER_PRESENT
- android.intent.action.BATTERY_CHANGED
Using the above permissions granted by users, the following activities are performed in the user’s devices:
- Using the internet permissions and WiFi manager service, the application checks for internet connectivity from the device, and disables the WiFi accordingly.

Figure 8 Performing a Check on WIFI Connectivity

Figure 9 Performing a Check on Internet Connectivity
- Collects device and sensitive phone information from the device like phone build, OS type, model, and company information

Figure 10 Steals Sensitive Phone Information
- Reads phone contacts and fetches and stores the contacts and contact list information of the users

Figure 11 Queries Phone Contact Information
- Reads victim’s files and storage and collects selective file types from the device.

Figure 12 Filters Particular File Types from the Device
The collected information from the victim’s device is uploaded to the remote server as per the attacker’s instruction. However, our research shows that this remote server has already been taken down and now displays a connection-refused error.
C2 Link: https://internetwideband.com/user/definition
Safety Recommendations:
- Keep your antivirus software updated to detect and prevent malware infections.
- Keep your system and applications updated.
- Use strong passwords and enable two-factor authentication during logins.
- Verify the privileges and permissions requested by apps before granting access.
- People concerned about the exposure of their stolen credentials in the dark web can register at AmIBreached.com to ascertain their exposure.
MITRE ATT&CK® Techniques- for Mobile
| Tactic | Technique ID | Technique Name |
| Défense Evasion | T1406 | 1. Obfuscated Files or Information |
| Discovery | T1421 T1430 T1426 | 1. System Network Connections Discovery 2. Location Tracking 3. System Information Discovery |
| Collection | T1432 T1430 T1507 | 1. Access Contact List 2. Location Tracking 3. Network Information Discovery |
| Command and Control | T1573 T1071 | 1. Encrypted Channel 2. Application Layer Protocol |
| Network Effects | T1439 | 1. Eavesdrop on Insecure Network Communication |
| Impact | T1447 | 1.Delete Device Data |
Indicators of Compromise (IoCs):
| IOC | IOC Type |
| fd1aac87399ad22234c503d8adb2ae9f0d950b6edf4456b1515a30100b5656a7 | SHA256 |
| 5b4f345c9cef3814b9497600104d3e325ecaa59b5a93922de641aa4b519da58f | SHA256 |
| hxxps://internetwideband[.]com | Interesting URL |
| hxxp://e[.]sy/ | Interesting URL |
| hxxp://egov[.]sy/ | Interesting URL |
| hxxps://egov[.]sy/mobile/ | Interesting URL |
| 82.137.201[.]71 | IP address |
| 142.250.186[.]163 | IP address |
About Cyble:
Cyble is a global threat intelligence SaaS provider that helps enterprises protect themselves from cybercrimes and exposure in the darkweb. Cyble’s prime focus is to provide organizations with real-time visibility into their digital risk footprint. Backed by Y Combinator as part of the 2021 winter cohort, Cyble has also been recognized by Forbes as one of the top 20 Best Cybersecurity Startups to Watch In 2020. Headquartered in Alpharetta, Georgia, and with offices in Australia, Singapore, and India, Cyble has a global presence. To learn more about Cyble, visit www.cyble.com.