As usual DopplePaymer ransomware operators add another data breach to their name. In this instance, they breached Kent County Trading Ltd, one of the financial assets trading companies based in England.
Kent County Trading Ltd was founded in 2004. The company’s line of business includes holding or owning securities of companies other than banks. It mainly runs activities of other asset holding companies that are not listed elsewhere. Apart, from being trading in the capital market for the last 15 years it is still trying to strengthen its roots to become the leading asset trader in the market.
The DopplePaymer ransomware operators leaked their files as shown below-:
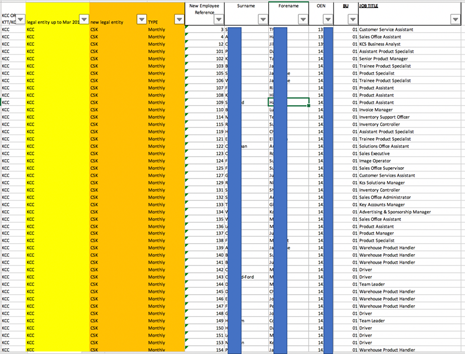
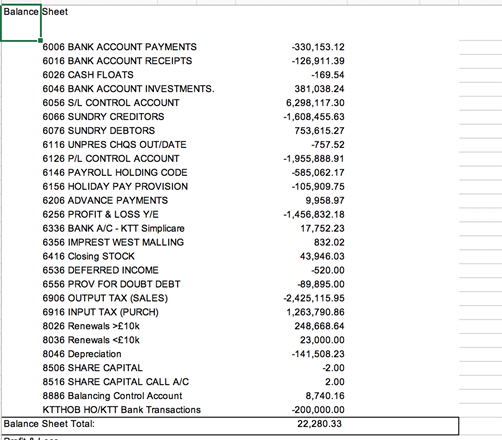
The Cyble Research Team has verified the leak of around 1 GB. The data leak includes multiple financial documents of the company such as their ledger accounts, budgets, invoices, employee data, and many more. Below is a snapshot of a few of the files from the lot being leaked by the ransomware operators.

About Cyble:
Cyble Inc.’s mission is to provide organizations with a real-time view of their supply chain cyber threats and risks. Their SaaS-based solution powered by machine learning and human analysis provides organizations’ insights to cyber threats introduced by suppliers and enables them to respond to them faster and more efficiently.
Cyble strives to be a reliable partner/facilitator to its clients allowing them with unprecedented security scoring of suppliers through cyber intelligence sourced from open and closed channels such as OSINT, the dark web and deep web monitoring and passive scanning of internet presence. Furthermore, the intelligence clubbed with machine learning capabilities fused with human analysis also allows clients to gain real-time cyber threat intel and help build better and stronger resilience to cyber breaches and hacks. Due to the nature of the collected data, the company also offer threat intelligence capabilities out-of-box to their subscribers.




















