The Maze ransomware operators have struck again, and on this instance they breached Moseley Construction Group, fast-growing, and well-known multi-family home builders based in America.
Moseley Construction Group was founded in the year 2007. From then they have grown and developed its expertise in the multifamily arena, working with local boutique developers, some of the largest apartment REITs in the country, and everyone in between. Moseley Construction Group excels in all aspects of multifamily construction; from apartment repositioning and conversions to historic multifamily renovations, to out of the ground new construction, the Moseley team brings a diversity of experience to help deliver your vision. Their mission is to be a world-class “customer first” construction firm, specializing in multi-family construction, both new and renovations. Renovations include vacant and in-unit occupied apartments, apartment repositioning and conversions, common areas, exterior facades, lobbies, and amenity areas such as fitness centers. New construction includes podium structures with below-grade parking, stick-built up to four stories above grade, and type 3 construction up to 7 stories.
Below is the message been posted by Maze ransomware operators on their website-:

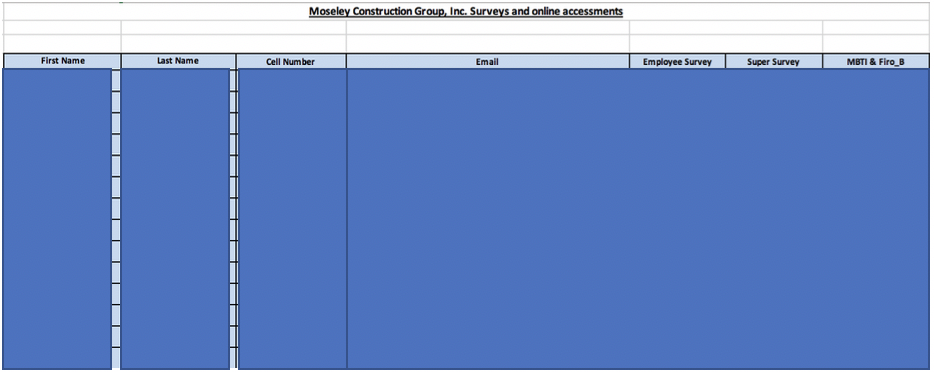
The Cyble Research Team has verified and reported this data leak. The data leak includes highly sensitive and confidential documents and data such as company’s purchase agreements, financial invoices, employee’s survey records, official legal contracts, and many more. Below are the snapshots of a few of the sensitive leaked files from the large lot.


About Cyble:
Cyble Inc.’s mission is to provide organizations with a real-time view of their supply chain cyber threats and risks. Their SaaS-based solution powered by machine learning and human analysis provides organizations’ insights to cyber threats introduced by suppliers and enables them to respond to them faster and more efficiently.
Cyble strives to be a reliable partner/facilitator to its clients allowing them with unprecedented security scoring of suppliers through cyber intelligence sourced from open and closed channels such as OSINT, the dark web and deep web monitoring and passive scanning of internet presence. Furthermore, the intelligence clubbed with machine learning capabilities fused with human analysis also allows clients to gain real-time cyber threat intel and help build better and stronger resilience to cyber breaches and hacks. Due to the nature of the collected data, the company also offer threat intelligence capabilities out-of-box to their subscribers.




















