Threat Actor Adopting CHM Files to enhance their latest attacks
Threat actors (TAs) employ diverse file formats to disseminate malicious payloads, primarily to enhance the likelihood of a successful infection. These different file formats are being sent via spam email as an attachment to entice users to download and execute them, thereby exposing themselves to malicious content. TAs typically employ a range of file formats, such as doc, zip, HTML, PDF, ISO, etc., as attachments in their spam campaigns.
OneNote files have also emerged as a recent addition to their repertoire of potential delivery mechanisms. Cyble Research Intelligence Labs (CRIL) has observed that several malware families, such as AsyncRAT, QuasarRAT, DCRAT, etc., have been found using OneNote attachments as part of their tactics. In February 2023, the well-known malware, Qakbot, started using OneNote attachments in their spam campaigns.
CRIL has also noticed a slight change in Qakbot’s delivery mechanisms in its recent spam campaigns. The variation involves the OneNote attachment dropping a CHM file.
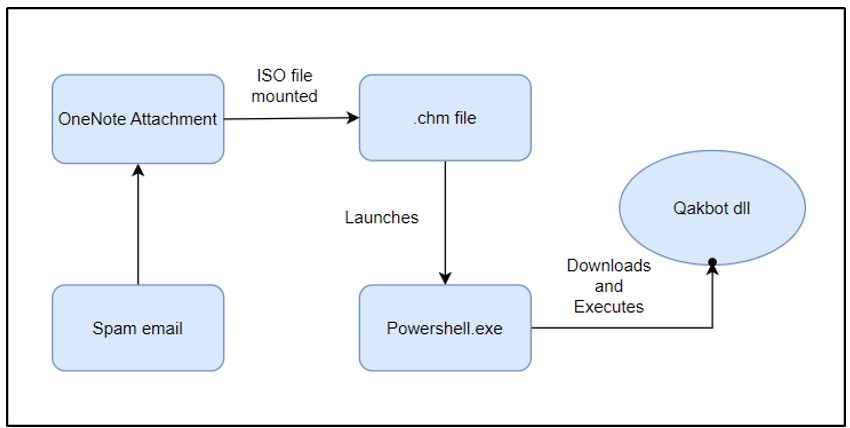
In the first stage of the infection, a spam email is sent with a OneNote attachment. When the recipient opens the attachment, an embedded CHM file is loaded, triggering the execution of a PowerShell script. The PowerShell script is responsible for downloading a DLL containing the Qakbot malware, which is executed using rundll32.exe.
The figure below shows the new delivery mechanism of Qakbot malware using a .chm file.
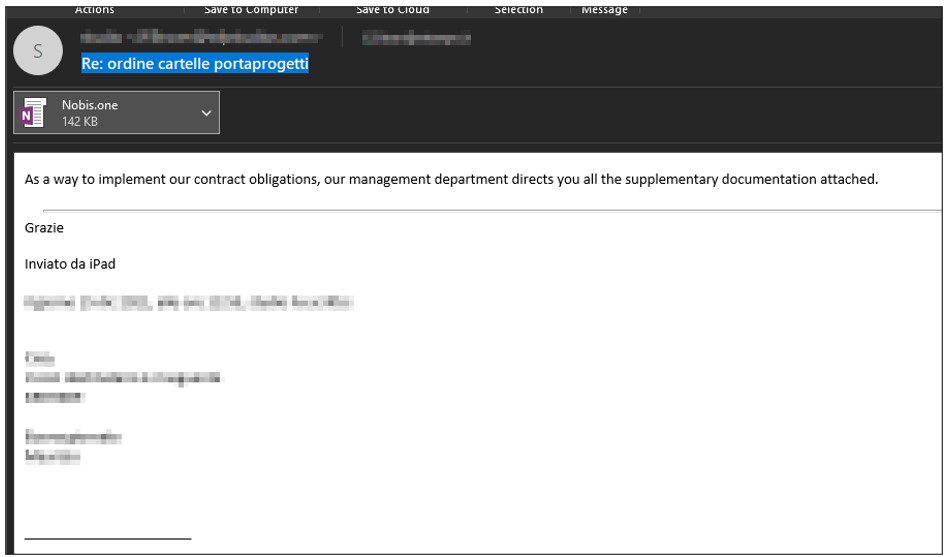
Qakbot is known to use spam email campaigns to distribute itself, and it often uses hijacked email threads to make its messages appear convincing and legitimate. The figure below shows the spam email with the subject line “Re: ordine cartelle portaprogetti” and a OneNote attachment named “Nobis.one”.
When a user launches the OneNote attachment, a page is displayed to the user with a message featuring a cloud-based attachment. This fraudulent message is intended to entice the user to double-click on it and view the attachment, which in turn triggers the Qakbot infection.
The figure below displays the fraudulent OneNote page.
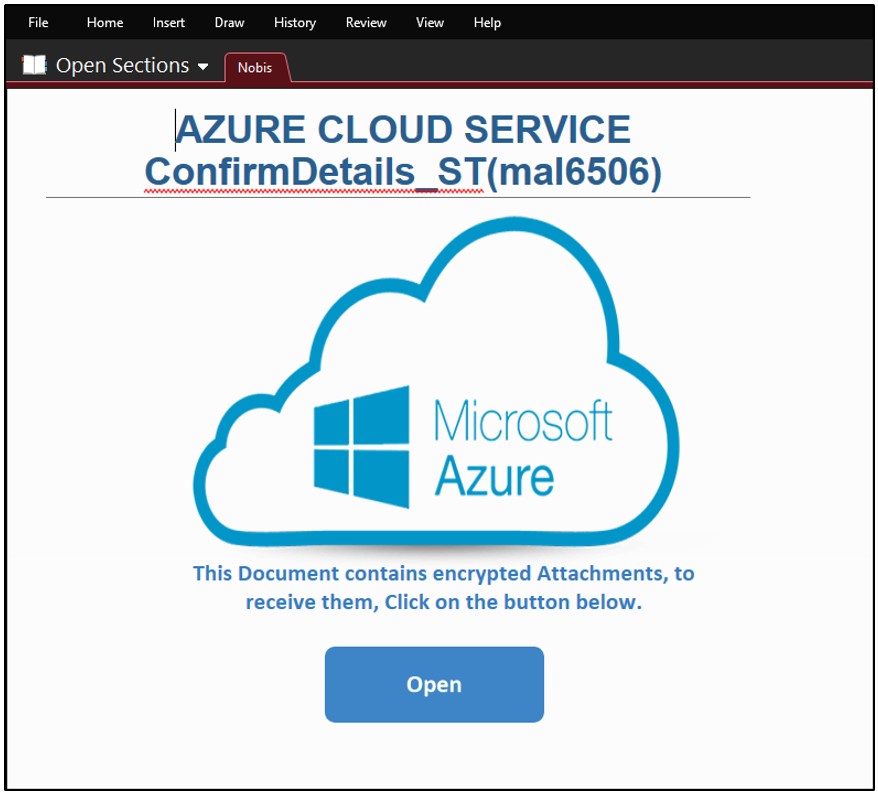
When the user double-clicks on the “Open” button, an embedded ISO file is executed, which creates a virtual drive on the user’s machine by mounting the ISO file. Upon mounting the ISO file, a specially crafted CHM file is shown in the mounted drive, allowing the user to open it.
The figure below shows the CHM file in the mounted virtual drive.

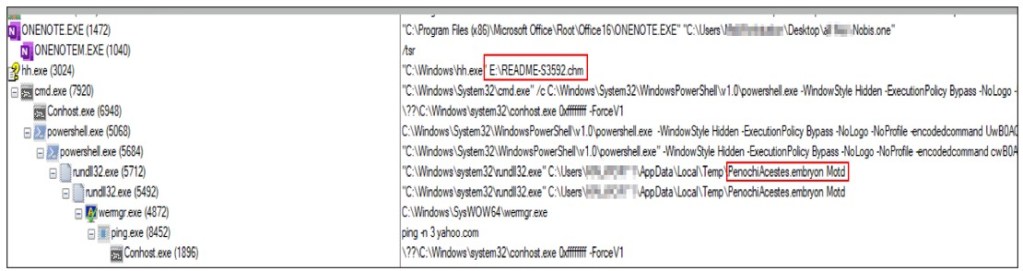
The CHM file acts as a container for several files, such as HTML pages, HTML Help Content (HHC) files, etc. When a user opens the CHM file, it triggers the execution of an htm file called “README-S3592.htm” saved within the container.
The figure below shows the content of the CHM file.

Upon execution, the “README-S3592.htm” file executes a base64 encoded PowerShell content. The below figure shows the deobfuscated PowerShell content.

Once the PowerShell script is launched, it attempts to download the malicious content from the list of hardcoded URLs using the wget command. The downloaded file is then saved in the user’s temporary directory and named “PenochiAcestes.embryon”.

The downloaded file is a DLL (Dynamic Link Library) file which is the actual Qakbot malware. The PowerShell script further verifies if the downloaded file size is 100 KB or higher. If the condition is met, the script proceeds to execute the downloaded file by calling the rundll32.exe command. The PowerShell command to run the downloaded dll file is:
powershell – WindowStyle Hidden – ExecutionPolicy Bypass – NoLogo – NoProfile – encodedcommand “start rundll32 $env:TEMP\PenochiAcestes.embryon,Motd;
If the download fails, the PowerShell script will sleep for 4 seconds using the “Start-Sleep” command and tries the next URL in the list for downloading the Qakbot malware.
The figure below shows the process tree of Qakbot.
Once the Qakbot file is executed, it has the capability to steal sensitive data such as login credentials and financial information. Although it originated as a banking trojan, it has evolved into a powerful tool for gaining initial access to devices and networks in recent years. Furthermore, Qakbot can download and install other malware onto the infected system, including Cobalt Strike, Brute Ratel, and other malicious tools, which can be used to carry out further attacks.
Conclusion
In recent campaigns, we have observed a consistent pattern in which threat actors increasingly rely on OneNote to deliver Qakbot malware. These campaigns involve the use of various new techniques primarily geared towards evading detection, with only the embedded content varying. OneNote attachments with CHM files are a notable feature of this latest campaign. Despite ongoing efforts to combat it, Qakbot retains its status as a major threat in the current threat landscape due to its formidable and ever-expanding capabilities.
Cyble Research and Intelligence Labs continue to monitor the activity of Qakbot and other malware and will provide timely updates to our readers.
Our Recommendations
- Do not open emails from unknown or unverified senders.
- Avoid downloading pirated software from unverified sites.
- Use strong passwords and enforce multi-factor authentication wherever possible.
- Keep updating your passwords after certain intervals.
- Use reputed anti-virus solutions and internet security software packages on your connected devices, including PCs, laptops, and mobile devices.
- Avoid opening untrusted links and email attachments without first verifying their authenticity.
- Block URLs that could be used to spread the malware, e.g., Torrent/Warez.
- Monitor the beacon on the network level to block data exfiltration by malware or TAs.
- Enable Data Loss Prevention (DLP) Solutions on employees’ systems.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566 | Phishing |
| Execution | T1059 T1204 T1218 T1059 | Command and Scripting Interpreter User Execution Rundll32 PowerShell |
| Defense Evasion | T1140 T1564 T1055 | Deobfuscate/Decode Files or Information Hidden Window Process Injection |
| Command and Control | T1071 | Application Layer Protocol |
Indicators of Compromise (IOCs)
| Indicators | Indicator Type | Description |
| ee4abe2bfbb1e212a52a42933c6f0a4361f3e146e9180f07753012da38762253 58b54ac8687169e4f92da3446b433adc39af5820 238412e542f07d53c630929cd3f3c6d3 | Sha256 Sha1 Md5 | .eml file |
| e030ea871e4ef05f0b9a75f8fc2ef4a1a90a42f46f5ec5f9a7ec199bd49e1e47 4232915f680e8aeaf3a83c08f8f9fd38d00647e2 948ed50640dda430e45bd45880260934 | Sha256 Sha1 Md5 | .one file |
| 2598dd1019aee192c357567e92f9b45622ad789e60f20ed3df26d32952b3a1ef cb0679e56e658d8b177e2170222d08ba827ef0d8 dd15e366adb83b9307cfc1d938e7e0bd | Sha256 Sha1 Md5 | .chm file |
| 2ec633b615864d6a8fc7fd7f1c906f1b6538af5719d671f8459d4a5627be6fa7 b98738b6e0051b4fd730596b4d2dfe2a678b0a2b ca58c1be5da0d84d1d4616637e351d77 | Sha256 Sha1 Md5 | .one file |




















