Keylogger and Gh0st RAT Variant deployed to spy on Users
Threat actors (TAs) have been relentlessly employing diverse techniques to propagate malware by leveraging counterfeit websites of renowned applications. Cyble Research and Intelligence Labs (CRIL) reported on a trojanized version of Telegram specifically aimed at Chinese users. Telegram is a widely used application, and due to its unavailability in China, TAs exploit this condition to deceive users by providing fake Chinese-language versions of the software.
Recently, CRIL found a phishing site, hxxps://telagarm[.]top spreading a malicious Telegram installer. We believe that this installer file targets Chinese users as the default language used in the installer is Chinese.
The figure below shows the phishing site.

This sophisticated malware operates through multiple stages and employs advanced evasion techniques to avoid detection. Unlike typical downloaders that directly fetch payloads, this downloader, used in the current campaign, follows a sequence of requests to obtain the URL for the final stage. The ultimate payload, in turn, utilizes a combination of techniques, including process injection, DLL sideloading, and encrypted shell code, to achieve execution.
While investigating this campaign, we found evidence linking it to the same Threat Actor (TA) behind the SiMay RAT attacks in 2022. The TA uses an updated version of the downloader and final stage payloads in this campaign.
Technical Analysis
This phishing site is distributing a malicious installer file in the form of a .msi file. The language used by default in the installer file (SHA256: 8013a2e9bde9dcfd3f49cc09d5842ad55d21962d7a1216897121ff4d0f344558) is Chinese, suggesting that the TA could be targeting Chinese-speaking users. This installer disguises itself as a legitimate Telegram file while simultaneously dropping and executing a downloader file in the background.
The figure below shows the installer window.

The .msi file consists of two distinct files within it. The first file (iii.exe) contained within the .msi package is a malicious downloader that downloads and executes the next stage payloads. This file is dropped by the installer in the “Documents” folder.
The second file (tsetupx64.4.8.3.exe) is a seemingly legitimate Telegram setup, which appears to be the installation package for the popular messaging application Telegram. This is meant to deceive users into thinking they are downloading and installing authentic Telegram software.
The figure below shows the content of the .msi file.

The figure below shows the process tree.

Downloader
The downloader file (SHA256: 17c2faa7d7e5ecefd6f33a991cd60e9c033b589dd27023bb820cb4ba52ba0c5c) is a 32-bit executable targeting the Windows operating system.
The figure below shows the file details.

The downloader, upon execution, starts connecting to IP addresses “59.111.183.194”, which resolves to a Chinese cloud service provider.
The figure below shows the network TCP requests made by the downloader.

Using the InternetReadFile() function, this malware fetches the content from a specific URL: “hxxps[:]//”. The content retrieved from this URL is then loaded into a buffer, as shown in the figure below.

The content mentioned above is in the form of a JSON object. An analysis of this response identified an email address associated with the threat actor (TA). Delving deeper into the investigation, we found that the same email address was previously linked to a TA mentioned in a report released by K7 researchers in 2022.
Drawing connections from this discovery, it is suspected that the identical TA responsible for the SiMay RAT attacks reported in 2022 is the one executing these current attacks.
The sharetime mentioned in the JSON data, “1685768121180,” resolves to “June 3, 2023,” suggesting that the threat actor (TA) has restarted their attack campaign. In the previous campaign, the share was activated in 2021.
The figure below shows the email ID present in the JSON object.

This downloader utilizes the key values obtained from the previously fetched JSON object to construct URLs for upcoming requests. Now it retrieves content from the URL:
- hxxps[:]//note.youdao[.]com/yws/public/notebook/9fa9db02d7c790b6f9709e3b1605c6cc/subdir/WEB400eaebc293ddb0f58dcafa44f8b74c2
The fetched content is in the form of another JSON object, as shown in the figure below. This JSON object contains crucial details regarding “.dat” files, which are scheduled to be downloaded in the next step of the process.

The TA has hosted three “.dat” files on hxxps://note.youdao[.]com/ynoteshare/index.html?id=9fa9db02d7c790b6f9709e3b1605c6cc&type=notebook&_time=1686584769284. These .dat files contain a Base64 encoded URL and other details related to next stage payload. These “.dat” files are named using “DU” followed by a number.
The figure below shows the “.dat” files.
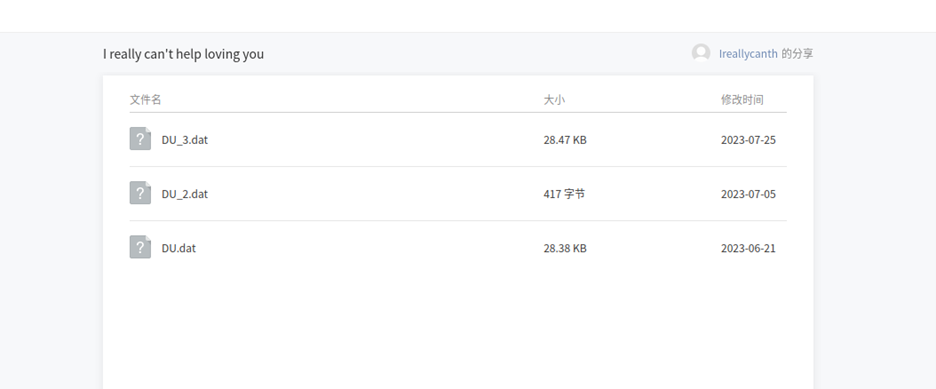
Now this downloader downloads the “DU_3.dat” file from “hxxps://note.youdao.com/yws/api/personal/file/WEB7645e55f5ee27c0802c56881c4c5f356?method=download&shareKey=9fa9db02d7c790b6f9709e3b1605c6cc”
The downloader creates a folder with a random name formed by combining a sequence of 6 characters which contains alphanumeric characters and an underscore under the “C:\\Users\\Public\\Music” directory.
After creating the folder, it saves the “DU_3.dat” file in this folder and sets the file’s attributes to hidden. The “CreateFileA” function is called for this purpose.

The figure below shows the Base64 decoded content of the “DU_3.dat” file. It contains the URL for the next stage, the name of the payload, and the name of the directory to save the payload.
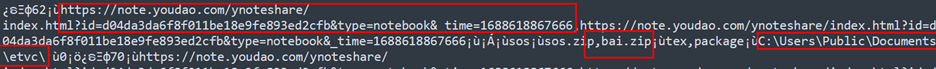
After analyzing all the “.dat” files shown in the figure above, we found that they point to a different URL, as highlighted in the figure below.
- dat
hxxps[:]//note.youdao[.]com/ynoteshare/index.html?id=d04da3da6f8f011be18e9fe893ed2cfb&type=notebook&_time=1688618867666 - dat
hxxps[:]//note.youdao[.]com/ynoteshare/index.html?id=164394dd79b3bea74a76eb8e95976513&type=notebook&_time=1687346123857
- dat
hxxps[:]//note.youdao[.]com/ynoteshare/index.html?id=9f3f644a14316db6b64924e92a813e15&type=notebook&_time=1685772858275

Now, the downloader performs requests in a manner similar to how it downloaded the “.dat” file. It initiates the process by making a request to the following URL:
- hxxps://note.youdao[.]com/yws/api/personal/share?method=get&shareKey=d04da3da6f8f011be18e9fe893ed2cfb
The content received from this initial URL is then utilized to form the URL for the next request, as highlighted in the figure below. It makes a request to the following URL to fetch details of files hosted on the server.
- hxxps://note.youdao[.]com/yws/public/notebook/d04da3da6f8f011be18e9fe893ed2cfb/subdir/WEB4c64cfb83b69382247b8bc37425e47ac
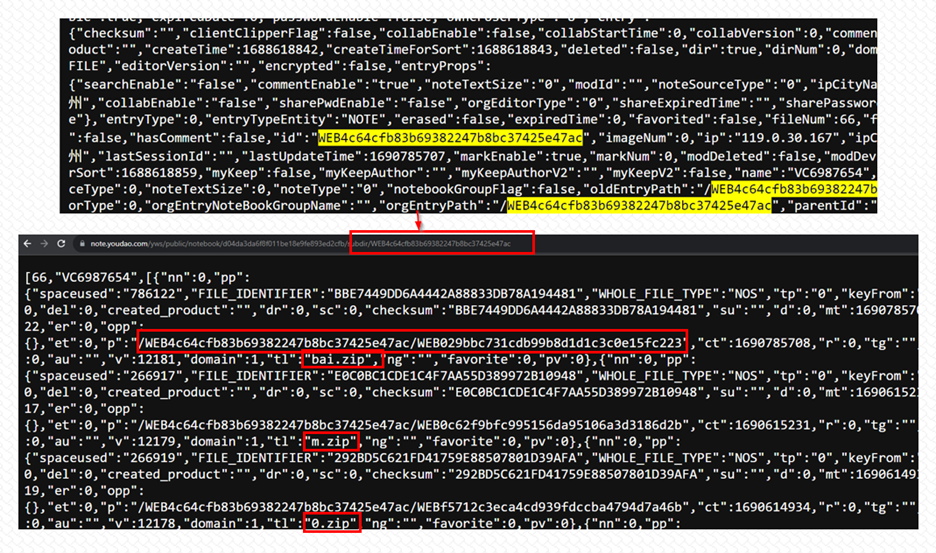
Afterwards, it downloads the next stage payload from:
- hxxps://note.youdao[.]com/yws/api/personal/file/WEB029bbc731cdb99b8d1d1c3c0e15fc223?method=download&shareKey=d04da3da6f8f011be18e9fe893ed2cfb
Compressed Payload
The compressed payload file “bai.zip” is downloaded and temporarily stored as “sl2VMF” in the root of the “C:\Users\Public\” location. This ZIP-compressed file comprises four folders: “package,” “static,” “txtCode,” and “winzipper,” as shown below.

The “package” folder contains two files: “afedf.trg” and “GetSkype.dll.” The “static” folder contains a file named “png.1413131.” The “txtCode” folder holds a file called “out.bin,” while the “winzipper” folder contains a file named “fdafvdav.fdafda,” as shown below.

After being extracted, the main malware file proceeds to write the contents of the “package” folder to specific predefined locations on the system. The files from the “package” folder are copied to the below path:
- C:\Users\Public\Public Documents\etvc\<random_foldername><random_filename>
This directory includes the malicious DLL file (GetSkype.dll) and a legitimate executable named “afedf.trg.” The executable “afedf.trg” is copied and renamed with a random filename like “TDtng6.exe.” While running, the DLL will be loaded alongside the renamed executable using side-loading techniques.

The content of the “winzipper” folder, with the name “fdaf1.fda1gfq,” is copied to the “%Appdata%<random_foldername>” location, named “_wdJ.exe.” This copied file is a WinRAR file.
Next, the malware downloads a ZIP file named “xhn.zip” and extracts its contents, which include a shortcut file named “VCsite_ingcure.lnk.” The purpose of this shortcut file is to execute the following command line when executed:
- C:\Users\Public\Documents\etvc\b4VOly\TDtng6.exe
To ensure persistence, the malware copies the lnk file into the Startup folder, enabling it to automatically run the ” TDtng6.exe” executable every time the system starts. The figure below illustrates the files generated during execution to achieve persistence.

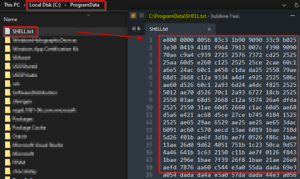
During the execution process, the file “png.1413131” from the “static” folder is copied to the “C:\ProgramData” directory. The copied file is subsequently renamed as “SHELL.TXT,” a shell code with an encrypted payload that the malware decrypts and uses to perform the malicious activity.
The figure below shows the malware’s process of creating a file and copying the content from the temporary ZIP file.

The figure below displays the content of “SHELL.TXT,” which is a shellcode with encrypted payload XORed by the value ‘0x25.’
Additionally, the malware drops several internet shortcut files with randomly generated names. These shortcut files are utilized to execute the “TDtng6.exe” when a user runs it. This tactic aims to deceive users into thinking that the shortcut points to a legitimate website or resource when, in fact, it leads to the execution of a malicious file (TDtng6.exe) stored in the specified location.

DLL SideLoading
DLL side-loading is a technique used by TAs to execute their malicious code within a legitimate application to evade detection, maintain persistence, and gain elevated privileges on a targeted system. By leveraging trusted processes, the malware can blend in with legitimate activities, making it harder to detect. This method allows attackers to distribute and update malware while bypassing security measures, ensuring prolonged control over compromised machines.
In this case, the malware employs the genuine “GetSkype” product executable named “TDtng6.exe” to facilitate the side-loading of the malicious “GetSkype.dll” into the victim’s system, as shown in the figure below.

The “GetSkype.dll” file, identified by the SHA256 hash: 67ebe6b782bf613a444fc20fca7002bfb9aa6b468a7f7b2b075953d65cf9ba93, is a 32-bit DLL executable that was compiled using Visual C++, as shown below.

Upon execution, the “TDtng6.exe” file performs side-loading of the “GetSkype.dll” which exhibits characteristics of a keylogger malware. It performs a range of functionalities, including evasion of antivirus detection by specifically targeting antivirus processes. The malware is designed to detect virtual machine environments, thereby concealing its malicious behavior during analysis. The presence of version information suggests its ability to adjust actions according to the target system’s operating system. Furthermore, it can gather system information, establish persistence by manipulating the registry, communicate with the C&C server, manipulate files, and capture keyboard inputs from the victims.
Remote Access Trojan (RAT)
Subsequently, the malware accesses the “SHELL.TXT” file, which contains the shell code responsible for importing modules, along with an encrypted PE file. Each byte of the encrypted PE file is XORed by the value 0x25. The figure below shows the decrypted PE file obtained by applying XOR with the value 0x25.
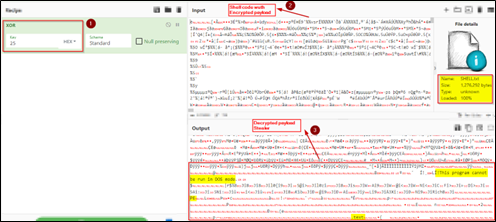
While executing, the malware decrypts the encrypted content in the “SHELL.TXT,” which is a malicious DLL executable file. The malware then loads and executes this decrypted DLL payload into the process memory. The observed payload’s behavior is similar to that of the Gh0st RAT.
The decrypted PE file, identified by the SHA256 hash: 2c16df586856e0d5ef10f27b6bafdf9c2445aa877d6a139f2eb4cd88a26f4003, is a 32-bit DLL executable that was compiled using Visual C++, as shown below.

This RAT has been in existence for several years as open-source software. Despite its long history, it remains actively distributed even today. As a RAT, it is utilized by TAs for unauthorized access and control of compromised computer systems. This malware possesses formidable capabilities and poses significant risks.
Its functionalities include remote control, keylogging, screen capture, file management, system surveillance, and data theft. Due to its versatility and ability to operate discreetly, this RAT is frequently employed in targeted attacks, cyber espionage, and data breaches to extract sensitive information.
The figure below displays the hardcoded strings found in the decrypted malware payload, which are utilized to execute various malicious activities of the RAT.

In addition to its functionalities, the malware payload includes a list of antivirus processes to evade detection and defense mechanisms, as shown below.

Conclusion
The discovery of the advanced multi-stage malware campaign, coupled with the attribution of the TA behind this campaign to the same entity responsible for spreading the SiMay RAT in 2022, highlights a sophisticated and persistent cyber threat. By capitalizing on the absence of Telegram in China, TAs deceive users by offering fake versions of the application. The wide popularity of Telegram as a communication platform only exacerbates the impact of these malicious campaigns.
Our Recommendations
We have listed some essential cybersecurity best practices that create the first line of control against attackers. We recommend that our readers follow the best practices given below:
Safety Measures Needed to Prevent Malware Attacks
- Do not open suspicious links in emails.
- Do not download the software from untrusted sources.
- Use a reputed antivirus and Internet security software package on your connected devices, including PC, laptop, and mobile.
- Refrain from opening untrusted links and email attachments without verifying their authenticity.
Users Should Take the Following Steps After the Malware Attack
- Detach infected devices on the same network.
- Disconnect external storage devices if connected.
- Inspect system logs for suspicious events.
Impact And Cruciality of Malware
- Additional malware can be dropped into the system.
- Infected systems could attack other systems.
- Loss of valuable data.
- Loss of the organization’s reputation and integrity.
- Loss of the organization’s sensitive business information.
- Disruption in organization operation.
- Monetary loss.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566 | Phishing |
| Execution | T1204 | User Execution
Command and Scripting Interpreter |
| Persistence | T1547.001 | Registry Run Keys / Start-up Folder |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or
Hide Artifacts Hijack Execution Flow: DLL Side-Loading Obfuscated Files or Information Process Injection |
| Privilege Escalation | T1055 | Process Injection |
| Credential Access | T1555 | Credentials from Password Stores
Steal Web Session Cookie Unsecured Credentials Keylogging |
| Collection | T1113 T1056 |
Screen Capture
Input Capture |
| Discovery | T1087 | Account Discovery
Software Discovery Process Discovery System Time Discovery System Service Discovery System Location Discovery Peripheral Device Discovery |
| Command and Control | T1071
|
Application Layer Protocol |
IoCs
| Indicator Type | Description | |
| hxxps://telagarm[.]top | URL | Phishing Site |
| d7c022eba7332279f6a4fa1aa1889a0e
21d82cf117983fd28c8a305fc36017275aa7dcdf 8013a2e9bde9dcfd3f49cc09d5842ad55d21962d7a1216897121ff4d0f344558 |
Domain | MSI File |
| 63ba00fef9994af47f9807bd1387df7b
fb07113a3f5e7137c9912d952dd8d419d1722e05 17c2faa7d7e5ecefd6f33a991cd60e9c033b589dd27023bb820cb4ba52ba0c5c |
MD5
SHA1 SHA256 |
Downloader |
| be49ea943a795b8cc239206448f4f074
31db6c6ab4e1a9f7c420ddb5596f9364f4839d83 3451348334f58217fbc49f0e1861dd67ec9cb54a4b8b50c2ad9082d07d69fa30 |
MD5
SHA1 SHA256 |
DU_3.dat |
| da15a7babf3ca046304246fb043f4d16
52741b8d5e321288c9f9301be5dfa011594d9f0c a565efb19a67514ba010fa358421505960970ab7e51db8925051558a10d274d6 |
MD5
SHA1 SHA256 |
DU_2.dat |
| 03b2515177d524fe36420fd1e42d2f6f
09ab64a9a505aa8fcf0cb3ca3a1a19d23171a1fa 075f59c3c7858c61e4c14dce5a4cb8092402616753734acbb3e3a07665cf3696 |
MD5
SHA1 SHA256 |
DU.dat |
| 4c429b202abc2b790b8a439b05edb63c
69b4dd97c836bcfd07df99a20c45cd276c00b231 67ebe6b782bf613a444fc20fca7002bfb9aa6b468a7f7b2b075953d65cf9ba93 |
MD5
SHA1 SHA256 |
GetSkype.dll |
| 3fd34181978cd402ac4d79febf8cf38a
47666948796987008e2ded94baa9185d2e79dc26 2c16df586856e0d5ef10f27b6bafdf9c2445aa877d6a139f2eb4cd88a26f4003 |
MD5
SHA1 SHA256 |
RAT |
| b3a99b97d4be5f824fbb7000f6087c80
3f89a11433070eea3bfe1d9c254a619833396483 ba8620420a59d04c62e8bcabde853ce806e6722e6627e9deebd0a0e98b4b812e |
MD5
SHA1 SHA256 |
SHELL.TXT |




















