Key Takeaways
• The blog highlights a new infection technique for distributing STRRAT version 1.6. It involves a spam email with a PDF attachment that, when opened, downloads a zip file containing the malicious JavaScript, which drops STRRAT.
• STRRAT version 1.6 employs two string obfuscation techniques: “Zelix KlassMaster (ZKM)” and “Allatori”, making it more challenging for security researchers to analyze and detect the malware.
• STRRAT version 1.6 has evolved from its previous variants and has been actively distributed since March 2023. It has been detected in the wild using various infection chains.
• The malware retains its key functionalities, which include targeting popular web browsers like Chrome, Firefox, and Internet Explorer, as well as widely used email clients such as Outlook, Thunderbird, and Foxmail.
Overview
In 2020, STRRAT, a Java-based Remote Access Trojan (RAT), emerged with a diverse set of functionalities, enabling activities like keylogging and pilfering credentials from browsers and email clients. Additionally, it has been detected incorporating a “Crimson” Ransomware module. Over time, since its initial discovery, STRRAT has continuously evolved and employed various infection chains.
Cyble Research And Intelligence Labs (CRIL) recently identified a new infection technique used to distribute STRRAT. This new method involves the distribution of STRRAT version 1.6, which utilizes two string obfuscation techniques. Detailed information about these techniques can be found in the technical analysis section.
The figure below shows the infection flow:

Initial Infection
The infection initiates through a spam email sent to the target, which pretends to come from an electronic-based company. The email contains an attached PDF file, which is presented as an invoice.

After opening the PDF attachment, a download image is displayed within the PDF. When clicked, it downloads a zip file named “Invo-0728403.zip” from the URL hxxps://tatchumbemerchants[.]co.ke/Invo-0728403[.]zip.
Inside the downloaded Zip file, there is a JavaScript file that contains the encrypted payload of STRRAT.


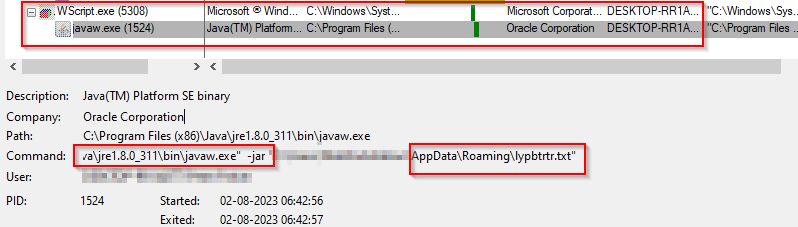
When executed, the Javascript file decrypts the payload within it and drops the file “lypbtrtr.txt” into the “\AppData\Roaming” directory.

Upon checking the file type, it becomes evident that the one with the “.txt” extension is, in fact, a disguised zip (JAR) file. After extracting its contents, a folder named “carLambo” and META-INF is revealed, containing classes, resources, and a MANIFEST.MF file. The presence of the “carLambo” package name indicates that the file is the STRRAT malware.

Technical Analysis
In our analysis of STRRAT, we discovered that the class names had undergone modifications, unlike the previous variant, where all the class names were gibberish. Furthermore, we observed that STRRAT currently utilizes two string obfuscators, namely “Allatori” and “Zelix KlassMaster (ZKM).” The previous variants were observed using only the “Allatori” obfuscator.

As shown in Figure 8, there are two methods for string deobfuscation. First, the string deobfuscation will be executed for “Zelix KlassMaster”.
The figure below shows the code after ZKM deobfuscation.

After completing the ZKM deobfuscation process, the next step involves deobfuscating the strings against the Allatori obfuscator.
The figure below illustrates the JAR file containing the now-readable strings.

Upon analyzing the deobfuscated JAR file, we came across the “ad.class” file, which points to the presence of a new version of the STRRAT malware (version 1.6). This variant has been actively distributed since March 2023 and disseminated through various infection chains. Over 70 samples of this particular version have been identified in the wild.

Persistence mechanism:
To maintain persistence, the RAT creates a task scheduler entry using the name “Skype,” as shown below.

Similar to previous versions of STRRAT, version 1.6 also utilizes an encrypted config.txt file to store the Command and Control (C&C) server information. The config.txt file is encoded with Base64 and encrypted using AES encryption.

The decrypted strings from the config.txt file are shown below:

Our analysis showed that STRRAT version 1.6 retains the same functionalities as its previous versions. It continues to target popular web browsers like Chrome, Firefox, and Internet Explorer, along with widely used email clients such as Outlook, Thunderbird, and Foxmail. It steals sensitive information from the victim’s machine.

C&C communication:
Once STRRAT connects to the C&C server, it can execute the below commands:
| Command | Description |
| reboot | Reboots the system |
| shutdown | Shutdowns the system |
| uninstall | Deleting Scheduled task |
| disconnect | Disconnects socket connection |
| down-n-exec | Downloads and executes the file |
| update | Executes the file received from the server |
| up-n-exec | Executes the file with extension .jar, .js, .vbs, .wsf |
| remote-cmd | Executing commands using cmd.exe |
| power-shell | Executing commands using powershell.exe |
| file-manager | Executing commands related to file operations |
| keylogger | Sends Keylog file |
| o-keylogger | Starts offline keylogging |
| processes | Interacts with running processes |
| h-browser | Creates Strigoi Browser using Firefox or Chrome |
| startup-list | Prepares an autorun list to automatically run during system startup or user logon. |
| remote-screen | Allows remote control of the system |
| rev-proxy | Creates reverse proxy |
| hrdp-new | Installs Hidden RDP Installer |
| hrdp-res | Restore hidden RDP sessions |
| chrome-pass | Retrieve Chrome credentials |
| foxmail-pass | Retrieve Foxmail credentials |
| outlook-pass | Retrieve Outlook credentials |
| fox-pass | Retrieve Firefox credentials |
| tb-pass | Retrieve Thunderbird credentials |
| ie-pass | Retrieve Internet Explorer credentials |
| all-pass | Retrieve credentials for all targeted browser and email clients |
| chk-priv | Check user privileges |
| req-priv | Attempts to get administrator privileges |
| rw-encrypt | Encrypt files and stores with the “.crimson” extension |
| rw-decrypt | Decrypts file |
| show-msg | Show ransom message |
| screen-on | Used to keep the screen on |
Conclusion
The analysis of the STRRAT malware, particularly version 1.6, reveals the continuous evolution and sophistication of this Java-based Remote Access Trojan. Since its emergence in 2020, STRRAT has undergone significant modifications, making it a persistent threat to cybersecurity.
The distribution of STRRAT through spam emails, disguising the payload inside a JavaScript file downloaded via a PDF attachment, showcases the Threat Actor’s (TA’s) efforts to conceal its presence and evade detection. The integration of two string obfuscation techniques, “Zelix KlassMaster” and “Allatori,” further complicates the analysis process and demonstrates the threat actor’s dedication to improving the malware’s evasion capabilities.
The presence of over 70 samples of STRRAT version 1.6 in the wild indicates an active and ongoing campaign by the TA, underlining the urgency for organizations to remain vigilant against this threat.
Our Recommendations
We have listed some essential cybersecurity best practices that create the first line of control against attackers. We recommend that our readers follow the best practices given below:
• Implement strong email filtering solutions to detect and block spam emails, phishing attempts, and malicious attachments.
• Refrain from opening untrusted links and email attachments without verifying their authenticity.
• Deploy robust endpoint security solutions that include antivirus, anti-malware, and anti-ransomware software. Keep these security tools up-to-date to ensure protection against the latest threats.
• Utilize URL filtering mechanisms to block access to known malicious websites and domains. This can prevent users from inadvertently downloading malware from malicious URLs.
• Conduct regular cybersecurity training sessions for employees, educating them about the latest threats, phishing techniques, and the importance of being cautious with email attachments and links. Make them aware of the risks of downloading and executing files from unknown sources.
• Monitor the beacon on the network level to block data exfiltration by malware or TAs.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566.001 | Phishing: Spearphishing Attachment |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1027.009 | Obfuscated Files or Information: Embedded Payloads |
| Credential Access | T1555.003 | Credentials from Password Stores: Credentials from Web Browsers |
| Collection | T1056.001 | Input Capture: Keylogging |
| Discovery | T1418 | Software Discovery |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
| Impact | T1486 | Data Encrypted for Impact |
Indicators of Compromise (IOCs)
| Indicators | Indicator Type | Description |
| 3d3cb10a1a9059900ddeb58209edcfa52461806558ebbee422c417c6535aa3a5
4651326299d02ac07c0b51c0abb7067f24293a65 9af7e66c85e07a1e182fcb024e7048a2
|
SHA256
SHA1 MD5
|
Spam email |
| 8250d324bbc14e3b3a7abc032b6b55aa0699ff9bc784d6c67fdd381edc3b9e56
8fa3c76f427f73cbfa864c380769825018cf72f5 c7130bf8bca520792f6eff1592a112b2 |
SHA256
SHA1 MD5 |
PDF attachment |
| c9380f51f0dd7167f833669eda3063a1a8f34cc3e2d536f29153952772dc8b20
f726bf1b6bc380c02d76d273765c888f6b41f197 61522d1e3290906215d580b8b59e6341 |
SHA256
SHA1 MD5 |
JavaScript Dropper |
| 9714dce49616e48fc4851d05453056939ab08bf140fe9a786616fa914debb4f4
433b6ac1169a9bd7e0cfe7029954070cc2b4ebdf 9bc8ac6d3a38357488de33952e929143 |
SHA256
SHA1 MD5 |
STRRAT1.6 |
| talibangeneral[.]dynamic-dns[.]net | Domain
|
C&C server |
| hxxp://jbfrost[.]live/strigoi/server/?hwid=1&lid=m&ht=5 | URL
|
C&C server |
| c9380f51f0dd7167f833669eda3063a1a8f34cc3e2d536f29153952772dc8b20
6ec3e682fbbd0c23fb4e3a2c2b28f03431b90a88651d227ae3f33b6fadf507cf 058c764614c8b0b457852a71ab93b559f81abb9e13b7fc2d6c6a4962881bf062 5536bd8910de7571b6e14b2dd8af6da658f0f702321966d5bef85e9d41f6de21 5536bd8910de7571b6e14b2dd8af6da658f0f702321966d5bef85e9d41f6de21 cbe7d5663fd5359a72f88e44d083703d9625235929c31e0f5b16a0b42cb44d35 8cae71910574fa96fdf20ddab8897e90d155e50036ddb2f3d033a7b13a45b90f c9380f51f0dd7167f833669eda3063a1a8f34cc3e2d536f29153952772dc8b20 b74a0e8adc5f0681405c94a684d6b887fdc20cd6d198d069f0981d6ba7d658c6 31c2e51efcbff0aa489aa6af1a48cf78f6a9febfb449a19d029f8cc8ebb4495f |
SHA256 | JavaScript Dropper |
| ab6f8c51d1f15a18cd23e1ad5a34c82c83746befb7d11cce2860c971be35adaa
d634982709d3ebf1641b1160ed6452fa9e3bf2cc8d28f397e56ca9687b28ec84 a0670c21968e2b1256d72799c22a512e503597ab375d20c49d9ec43428c4c3b2 3a74d083e1c4e30f1eedcb90c842bf1a7e65a979edab40e37885607bd566bee8 569f5f6de156bec90f9b0b0e4e707a702c0fea26ab6a0711e32f4a413995ae7c 176e45016749ec233b8fe1ce32ce2cd47dd5bc8da3663f1c6cf054f6ad58a187 3094952f4e4c826cdfbc7b146212eec6094f5104b4ba0d70d3b2920a263add27 4bf781354d02ca0d67a3a180fd6f0d183c6fba763caa660f986752be8b4bb586 6f7180a451691ee975f516cfc6fb3f0c983bc80aebd1d662a899ff4344e4077e b364c066e0aa794dd34c7a67ef08e83782c01be225edb5533f3a51f855d5e34 |
SHA256 | STRRAT 1.6 |
ET Rules
2030358 — ET MALWARE STRRAT CnC Checkin
2030359 — ET MALWARE STRRAT Initial HTTP Activity
2030360 — ET MALWARE STRRAT Requesting License Check
2044912 — ET DELETED Hash – STRRAT (ja3)
YARA Rules
rule strrat_javascript_dropper
{
meta:
author = “Cyble”
description = “Detects STRRAT Javascript Files”
date = “2023-08-04”
os = “Windows”
threat_name = “strrat”
severity = 100
reference_sample = “c9380f51f0dd7167f833669eda3063a1a8f34cc3e2d536f29153952772dc8b20”
strings:
$a = “tcejbOetaerC”
$b = “noitisoP”
$c = “teSrahC”
$d = “txeTdaeR”
$e = “sH1n3k0”
condition:
($a or $b or $c or $d) and $e
}
rule strrat
{
meta:
author = “Cyble”
description = “Detects STRRAT jar Files”
date = “2023-08-04”
os = “Windows”
threat_name = “strrat”
severity = 100
reference_sample = “9714dce49616e48fc4851d05453056939ab08bf140fe9a786616fa914debb4f4”
strings:
$a = “carLambo/WinGDI.class”
$b = “carLambo/FirstRun.class”
$c = “carLambo/resources/config.txt”
condition:
uint16(0) == 0x4b50 and all of them
}
Detection Guidance
Create a rule that blocks the execution of the “javaw.exe” process if it originates from “Wscript.exe.” Additionally, the rule should target cases where the command line parameter of “javaw.exe” is directed to the “%appdata%” path and the file extension being executed is “.txt”.
Disclaimer: The provided detection guidance rules are purely illustrative and should not be directly implemented in a production environment without proper testing, validation, and consideration of potential impacts on system performance and security. Always exercise caution when implementing security rules or policies, and ensure you fully understand the consequences of any changes made to your system or network.




















