Ransomware attacks have become one of the most common cybersecurity attacks in the recent years. The ongoing pandemic has significantly contributed to the spike in ransomware. With more employees working from home, there has been an explosion of ransomware attacks in 2020. Following the league, we now have a new ransomware on the market, Sarbloh Ransomware.
Recently, the research team at Cyble found a wild malicious document that delivers the Sarbloh Ransomware. Unlike other ransomware that demands a ransom from the victim to restore access to the data upon payment, the Sarbloh ransomware attack targets India with political agenda associated with the farmers protests in the country rather than asking for ransom money. The attack may be targeting users through spear phishing email campaigns containing malicious documents.
When this ransomware payload enters the system through malicious documents and stays stealthy, it encrypts system documents such Audio, images, video, databases, and other important documents and locks them. After that, it renames the encrypted files with the “.sarfbloh” extension. Finally, the ransomware leaks a ransom note “README_SARBLOH.txt” file or displays a lock screen message for demanding ransom. In this case, the ransomware note is associated with the farmer protests in India.
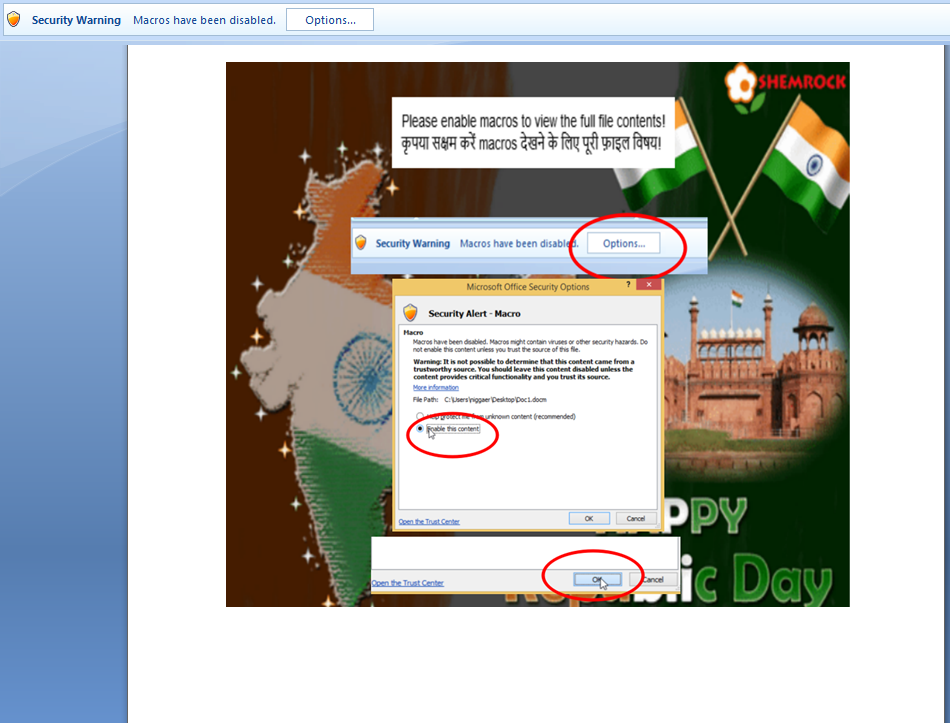
The image below highlights the decoy document that delivers the ransom payload on the victim machine.
Technical analysis:
The file we have identified and analyzed has the hash value: “b8756966cf478aa401a067f14eefb57f34eea127348973350b14b5b53e3eec4f”
This document has the embedded malicious macro that downloads and installs additional payload on the victim machine. The macro has an autopen function to execute subfunctions as soon as users enable security content. The image below highlights the debug view of all macro functions.

Upon further investigation, we found that the macro decodes the download URL runtime and proceeds to download and launch the ransomware payload file named “putty.exe” on the victim’s machine.

The image above showcases that the malicious document macro uses Bits transfer to the download payload file which is hosted on Amazon AWS. Interestingly, this ransomware employs the “living off the land” technique by using malicious macros with BITS transfer to deliver its actual payload on victim’s machine. BITS is a “Background Intelligent Transfer Service” that manages file uploads and downloads, to and from the HTTP(S) and SMB shares in a more controlled and balanced way. In the recent past, we have observed that this method is used by multiple targeted attacks (Banking trojans) to deliver payload as well as carry out data exfiltration because it provides a greater security evasion from being captured by antiviruses. The following is the payload download link which is on AWS cloud.
s3.ap-south-1[.]amazonaws[.]com/ans.video[.]input/transcode_input/profile16146815778005vw0qb[.]png
The delivered payload file with the hash value:
“acbe95f70f7d8e20781841cfd859d78575ccd36720c68b60789251a509e1194d”
This is a Borland Delphi compiled executable of the Sarbloh ransomware. Based on our static analysis, it clearly shows the ransom note of Sarbloh on the payload file along with the hardcoded public key. The Sarbloh ransomware uses the Windows function named “ZwcreateMutant” to create a mutant named “40691290-71d5-45bc-b86a-e714496f4bf2” for marking its presence on the Victims machine. The image below shows the debugger view of the mutant creation.

Upon execution, the payload file enumerates through the victim’s file system to find out the target documents, which are then encrypted and locked. The following are the documents targeted by the Sarbloh ransomware.

Finally, the ransomware renames all encrypted file with the . Sarbloh” extension, and the ransom note and message shown by Sarbloh ransomware is as follows.

Cyble is actively monitoring similar targeted attacks and will be updating further details as and when we procure more information.
Indicators of Compromise (IOCs):
| Indicator | Type | Description |
| b8756966cf478aa401a067f14eefb57f34eea127348973350b14b5b53e3eec4f | SHA256 | Malicious document |
| 5a7da8e180cbf700634d753635e9c89bdf7448cde913abdc384276c1cdab4d4c | SHA256 | Suspicious document (macro content is removed and uploaded to VT) |
| s3.ap-south-1.amazonaws.com/ans.video.input/transcode_input/profile16146815778005vw0qb[.]png | URL | Payload delivery URL |
| acbe95f70f7d8e20781841cfd859d78575ccd36720c68b60789251a509e1194d | SHA256 | Sarbloh Ransomware payload |
| \40691290-71d5-45bc-b86a-e714496f4bf2 | Mutant | Mutex value |
Yara Rules:
1.rule Sarbloh_Ransomware
{
meta:
author= “Cyble Research”
date= “2021-03-08”
description= “Coverage for paload file”
hash= “acbe95f70f7d8e20781841cfd859d78575ccd36720c68b60789251a509e1194d”
strings:
$header= “MZ”
$string1 = ” YOUR FILES ARE LOCKED! ” ascii wide
$string2 = ” Khalsa Cyber Fauj ” ascii wide
$string3 = ” README_SARBLOH ” ascii wide
condition:
$header at 0 and (all of ($string*))
}
Security Recommendations:
- Ensure that antivirus software and associated files are up to date.
- Search for existing signs of the indicated IOCs in your environment.
- Consider blocking or setting up detection for all URL and IP-based IOCs.
- Keep applications and operating systems running at the current released patch level.
- Exercise caution while opening attachments and links in emails.
- Keep systems fully patched to effectively mitigate vulnerabilities.
About Cyble
Cyble is a global threat intelligence SaaS provider that helps enterprises protect themselves from cybercrimes and exposure in the darkweb. Cyble’s prime focus is to provide organizations with real-time visibility into their digital risk footprint. Backed by Y Combinator as part of the 2021 winter cohort, Cyble has also been recognized by Forbes as one of the top 20 Best Cybersecurity Startups To Watch In 2020. Headquartered in Alpharetta, Georgia, and with offices in Australia, Singapore, and India, Cyble has a global presence. To learn more about Cyble, visit https://cyble.com




















