Read Cyble’s analysis of ChamelGang, a threat actor that camouflages its attacks using spoofed domains and SSL certificates to infiltrate networks and steal data.
In Q2 2021, the PT Expert Security Centre’s incident response team uncovered a cyberattack targeting an energy company. The investigation revealed that an unknown group had infiltrated the company’s network with the intent of stealing sensitive data. The team named the threat actor “ChamelGang,” inspired by the word “chameleon,” due to the group’s ability to cleverly camouflage their malware and network infrastructure under the guise of legitimate services from well-known companies like Microsoft, TrendMicro, McAfee, IBM, and Google.
The attackers employed a two-pronged approach to disguise their operations. First, they registered domains that closely mimicked legitimate ones, such as newtrendmicro.com, centralgoogle.com, microsoft-support.net, cdn-chrome.com, and mcafee-upgrade.com. Additionally, they deployed SSL certificates on their servers that imitated those from trusted sources like github.com, http://www.ibm.com, jquery.com, and update.microsoft-support.net. To further their attack, the group leveraged a trending technique—supply chain compromise—by infiltrating a subsidiary and using it as a gateway to breach the target company’s network.
Traditionally, state-sponsored cyberespionage groups have avoided using ransomware, but this trend is shifting as they now exploit ransomware to mask their activities. A SentinelOne report reveals that ransomware attacks on Brazil’s presidency and India’s AIIMS in 2022 were likely the work of the China-linked group ChamelGang (aka CamoFei).

Figure 1 – Cyble Vision Threat Library
Country of Origin
ChamelGang is a China-nexus APT threat group.
Targeted Countries
ChamelGang is recognized for its extensive cyber espionage endeavors, which encompass a diverse array of countries and regions. These include Afghanistan, Brazil, India, Japan, Lithuania, Nepal, Russia, Taiwan, Turkey, USA and Vietnam.

Figure 2 – Origin and Targeted Countries
Aliases
CamoFei.
Targeted Sectors
- Aviation
- Energy
- Government
ChamelGang Lifecycle
The attackers leveraged vulnerabilities to remotely execute commands on compromised hosts as part of their initial infection vector. To establish control and perform reconnaissance, they deployed tools such as a single-line reverse shell and Tiny Shell. An older DLL hijacking technique, specifically targeting the MSDTC service, was also utilized. For command-and-control (C&C), the attackers employed HTTPS beacons for hosts with direct internet access and SMB beacons to communicate with systems within isolated network segments. They maintained control over compromised machines using FRP (Fast Reverse Proxy), an open-source tool written in Golang. The attackers also used specific data collection techniques, applying custom filters to gather information from the compromised systems.
Initial Infection
In late March 2021, attackers compromised a subsidiary to infiltrate the target energy company’s network, exploiting a vulnerable web application on the JBoss Application Server platform. They leveraged a chain of vulnerabilities known as ProxyShell in Microsoft systems, which had been publicly disclosed at the Black Hat conference on August 5, 2021. Shortly after, various APT groups, including ChamelGang, began exploiting these vulnerabilities to penetrate victim infrastructures.
Exploited Vulnerabilities
ChamelGang has leveraged a range of vulnerabilities in its campaigns. The following are key examples of the vulnerabilities exploited by the group.
CVE-2021-34473: Microsoft Exchange Server Remote Code Execution Vulnerability.
CVE-2021-34523: Microsoft Exchange Server Privilege Escalation Vulnerability.
CVE-2021-31207: Microsoft Exchange Server Security Feature Bypass Vulnerability.
CVE-2017-12149: Red Hat JBoss Application Server Remote Code Execution Vulnerability.
Persistence
ChamelGang utilizes a variety of techniques to execute malware and maintain persistence on target systems. To establish persistence and escalate privileges on infected hosts, the attackers deployed a classic DLL hijacking method associated with the MSDTC service, which is responsible for coordinating transactions between databases, such as SQL servers and web servers. On another compromised host, they again employed this DLL hijacking technique to maintain their foothold.
ChamelGang is known to wield an extensive arsenal of tools, including BeaconLoader, Cobalt Strike, and backdoors such as AukDoor and DoorMe. Notably, they have also deployed a ransomware strain known as CatB, which has been linked to attacks on Brazil and India. This connection is evident from shared characteristics in the ransom notes, the format of contact email addresses, the cryptocurrency wallet addresses, and the file extension of encrypted files.
Tools used by ChamelGang
ChamelGang is known to wield an extensive arsenal of tools, including BeaconLoader, Cobalt Strike, and backdoors such as AukDoor and DoorMe. Notably, they have also deployed a ransomware strain known as CatB, which has been linked to attacks on Brazil and India. This connection is evident from shared characteristics in the ransom notes, the format of contact email addresses, the cryptocurrency wallet addresses, and the file extension of encrypted files. These tools encompass 7-Zip, BeaconLoader, Cobalt Strike, DoorMe, FRP, ProxyT, and Tiny SHell.
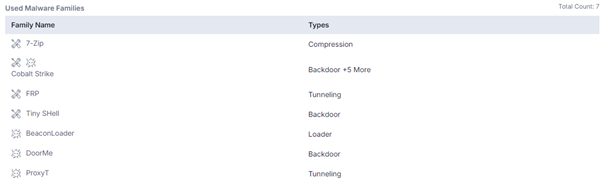
Figure 3 – ChamelGang Tools (Source: Cyble Vision)
BeaconLoader: BeaconLoader is a malware loader designed to stealthily deliver and execute beacons, typically for tools like Cobalt Strike. It facilitates post-exploitation activities such as command-and-control communication, lateral movement, and data exfiltration. BeaconLoader helps attackers maintain persistence and evade detection by minimizing payload size and using obfuscation techniques.
Cobalt Strike: Cobalt Strike is a commercial penetration testing tool used for simulating advanced cyberattacks. It features beacons for command-and-control (C&C) communication, enabling post-exploitation activities like lateral movement, privilege escalation, and data exfiltration. While intended for ethical hacking, Cobalt Strike is often misused by cybercriminals and APT groups to orchestrate real-world attacks.
DoorMe: DoorMe is a stealthy backdoor used by threat actors to persistently access compromised systems. It enables remote control, allowing attackers to execute commands, exfiltrate data, and maintain long-term presence while evading detection.
FRP: FRP (Fast Reverse Proxy) is an open-source tool written in Golang that enables secure tunneling of network traffic, allowing users to bypass firewalls or access internal services from external networks. Attackers often misuse it to maintain covert access to compromised systems.
ProxyT: Attackers use ProxyT, a lightweight tool, to tunnel network traffic through compromised systems, often to evade detection and maintain access to internal networks. It acts as a proxy, facilitating communication between infected hosts and command-and-control servers.
Tiny SHell: Tiny Shell is a lightweight, open-source remote access tool (RAT) used by attackers to gain remote control over compromised systems. It allows command execution, file manipulation, and data exfiltration while maintaining a minimal footprint to avoid detection.
Network
To mask their operations, the attackers carefully designed their network infrastructure to resemble legitimate services. They registered phishing domains mimicking well-known companies like Microsoft, TrendMicro, McAfee, IBM, and Google, including services for support, content delivery, and updates. Additionally, they deployed SSL certificates on their servers that replicated legitimate ones, such as github.com, http://www.ibm.com, jquery.com, and update.microsoft-support.net, further enhancing their ability to blend in and avoid detection while conducting malicious activities.
The malicious implant’s C&C configuration is a JSON object with two keys, which is used to craft DNS over HTTPS (DoH) requests via configured providers and malicious nameservers. It encodes C&C communications into subdomains of the malicious nameserver and sends TXT requests for the generated domain. Since these DoH providers are widely used for legitimate traffic and HTTPS encrypts the requests, blocking or inspecting them without intercepting the traffic is difficult, complicating the detection of anomalous activity like ChamelDoH’s encoded communications.
Conclusion
ChamelGang’s activities showcase a sophisticated blend of advanced techniques and clever obfuscation to infiltrate networks, maintain persistence, and evade detection. By leveraging vulnerabilities like ProxyShell, deploying a wide range of tools, including BeaconLoader, Cobalt Strike, and custom backdoors, and disguising their infrastructure under legitimate services, the group has successfully executed data theft and ransomware campaigns. Their use of DNS over HTTPS (DoH) and other tactics complicates detection, making them a formidable threat. ChamelGang’s operations, targeting critical sectors like energy, underscore the growing risks posed by stealthy, state-linked cyberespionage groups.
Recommendations:
Here are several recommendations to mitigate the risks posed by ChamelGang and similar cyber threats:
Strengthen Network Security: Implement network segmentation to isolate critical systems and limit lateral movement. Use firewalls and intrusion detection/prevention systems (IDPS) to monitor and block suspicious traffic.
Patch Vulnerabilities: Regularly update and patch all software, especially systems known to be exploited by groups like ChamelGang, such as Microsoft products. Conduct routine vulnerability assessments and penetration testing to identify and address potential weaknesses.
Monitor DNS Traffic: Implement DNS monitoring solutions to detect unusual patterns or requests, particularly those involving DNS over HTTPS (DoH). Look for anomalies that may indicate command-and-control communications.
Enhance Endpoint Protection: Use advanced endpoint detection and response (EDR) solutions that incorporate behavioral analysis to identify and respond to potential threats in real-time.
Educate Employees: Conduct regular training sessions on phishing awareness and safe browsing practices to minimize the risk of initial compromise through social engineering attacks.
Implement Multi-Factor Authentication (MFA): Use MFA for accessing critical systems to add an additional layer of security, making it more difficult for attackers to gain unauthorized access.
Develop an Incident Response Plan: Establish and regularly test an incident response plan to ensure quick and effective action in the event of a security breach. Include procedures for identifying and mitigating threats posed by APT groups.
Collaboration and Threat Intelligence Sharing: Engage with cybersecurity organizations and government bodies to share threat intelligence and gain insights into emerging threats and defense best practices.
MITRE attack Techniques Associated with ChamelGang

Figure 4 – MITRE ATT&CK (Source: Cyble Vision)
Exploit Public-Facing Application (T1190): ChamelGang exploited vulnerabilities in web applications (e.g., ProxyShell vulnerabilities in Microsoft products).
Exploitation for Client Execution (T1203): Malicious code execution through compromised applications or documents.
Exploitation for Privilege Escalation (T1068): Utilizing vulnerabilities (e.g., DLL Hijacking) to escalate privileges on compromised systems.
Exploitation for Privilege Escalation (T1068): Utilizing vulnerabilities (e.g., DLL Hijacking) to escalate privileges on compromised systems.
Indicator Removal on Host (T1070): Deleting logs and other indicators to avoid detection.
Archive Collected Data (T1560): Obfuscating data exfiltration methods through encryption or other means.
Data Encrypted for Impact (T1486): Utilizing ransomware (CatB) to encrypt files and demand ransom.