The Qilin ransomware group, also known as Agenda, has quickly gained attention as one of the more sophisticated and dangerous threat actors in the cybercrime landscape. Active since at least 2022, this group has consistently evolved its tactics, techniques, and procedures (TTPs) to target organizations across multiple sectors. Operating as a ransomware-as-a-service (RaaS) entity, Qilin allows affiliate cybercriminals to deploy its ransomware in exchange for a share of the ransom proceeds, often amounting to large sums.
Qilin’s operation is rooted in a typical RaaS model, wherein it provides affiliates with a suite of advanced tools to carry out their attacks. However, what sets Qilin apart from many of its peers is the customization options it offers to its affiliates. The group allows for tailored encryption methods and gives attackers the flexibility to restart systems in Safe Mode, a tactic used to disable security defenses before deploying the ransomware. Moreover, Qilin offers various execution parameters, providing affiliates with considerable control over how and when the ransomware is deployed.
Qilin’s ransomware payloads are highly customizable, making them effective against both Windows and Linux systems. The malware itself is often deployed manually after initial network infiltration. This infiltration occurs via compromised Remote Desktop Protocol (RDP) credentials, phishing attacks, or exploiting vulnerabilities in publicly exposed services. Once inside the victim’s network, the ransomware is executed, and the system is encrypted.
Double-Extortion Strategy
In line with modern ransomware groups, Qilin employs a double-extortion strategy. This means that the group does not only encrypt data but also exfiltrates sensitive files from the victim’s network. If the victim refuses to pay the ransom, the stolen data is published on a dedicated darknet leak site. This tactic increases the pressure on victims, as they now face the possibility of their confidential data being exposed to the public or sold on underground forums.
Ransom demands from Qilin often range in the millions of dollars, and victims are provided with detailed instructions on how to pay, typically in cryptocurrency. As part of their business model, the group also provides negotiation channels, allowing affiliates to communicate directly with the victim. In some instances, partial decryption is offered as a sign of good faith, further adding to the psychological pressure on the victim to comply with the demands.
Targeted Countries and Industries

Cyble Vision Threat Library (Source: Cyble Vision)
Qilin’s operations span across multiple continents, with the group targeting organizations in a diverse set of industries. The countries most affected by Qilin ransomware include the United States, United Kingdom, Germany, France, Canada, and Japan, among others. The group has shown no particular regional bias, instead opting for an indiscriminate approach that allows it to cast a wide net across global targets.
Industries most commonly targeted by Qilin include critical infrastructure sectors like healthcare, manufacturing, education, and energy. The group has also made its presence felt in the aerospace and defense, government, telecommunications, and financial sectors. This broad targeting further highlights the group’s reach and the seriousness of the threat it poses to businesses worldwide.
Advanced Techniques and Tactics
Qilin is a highly sophisticated threat actor with an impressive arsenal of TTPs. One of the key components of Qilin’s attack strategy is its use of valid accounts for initial access. These accounts are often obtained through leaked credentials or purchased on underground forums. Once inside the system, Qilin deploys its ransomware using various methods, including spear-phishing attacks and the exploitation of vulnerabilities in the network.
The group also makes extensive use of scheduled tasks to establish persistence within the target’s network. By creating scheduled tasks, Qilin ensures that its malicious payloads are executed on system startup or at predefined intervals. This persistence is crucial for maintaining control over compromised systems, especially if the victim attempts to mitigate the impact of the attack.
To escalate privileges, Qilin makes use of process injection techniques, injecting malicious code into legitimate system processes. This allows the group to gain higher levels of access and evade detection. Additionally, Qilin may modify group policies or manipulate registry run keys to weaken security defenses and further entrench itself within the victim’s environment.
The group is also adept at evading detection through defense evasion techniques. For example, Qilin may disable Windows event logging or reboot systems into Safe Mode, disabling security defenses before encryption begins. These techniques make it more difficult for victims to detect the attack in its early stages and hinder the efforts of security teams trying to trace the origin of the ransomware.
Conclusion
Qilin remains a major threat in the cybercrime world. Its adaptable ransomware and well-organized RaaS model continue to put organizations worldwide at risk. As state-sponsored groups like Moonstone Sleet increase their involvement, a multi-layered cybersecurity approach is essential.
Platforms like Cyble are crucial in combating these threats. With AI-powered tools for threat intelligence, dark web monitoring, and vulnerability management, Cyble helps businesses stay ahead of cybercriminals. By leveraging Cyble’s real-time detection capabilities, organizations can better defend against the menace of ransomware like Qilin and other cyberattacks.
Defensive Measures and Recommendations
- Multi-Factor Authentication (MFA): Implement MFA across all systems, especially for RDP and remote access services, to prevent unauthorized access using stolen or leaked credentials.
- Network Segmentation: Isolate critical systems and sensitive data from less secure areas of the network. This limits lateral movement for ransomware attacks and makes it harder for threat actors like Qilin to access key systems.
- Regular Software Patching: Ensure all systems, especially those with publicly exposed services, are regularly patched. Exploiting unpatched vulnerabilities is a common attack vector for Qilin, so keeping software up-to-date can significantly reduce risk.
- Endpoint Detection and Response (EDR): Deploy EDR solutions to monitor and detect suspicious activities on endpoints. This can help identify ransomware payloads and prevent execution before significant damage occurs.
- User Training and Phishing Simulations: Educate employees on recognizing phishing attempts and other social engineering tactics. Regular phishing simulations can help reinforce the importance of caution when interacting with unsolicited emails or links.
- Ransomware Backup Strategy: Implement a better backup strategy with frequent, isolated backups that are not directly accessible from the network. This helps ensure data can be restored without paying the ransom.
- Disabling Unnecessary Services: Disable unused or unnecessary services, especially RDP, and limit network access to only those who need it. Where possible, use a VPN for remote access to avoid exposing services to the internet.
MITRE Attack Techniques Associated with Qilin Ransomware Group
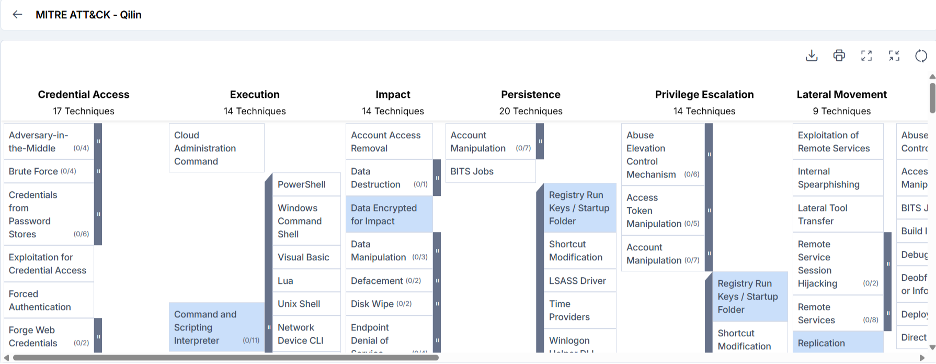
Qilin Ransomware MITRE ATT&CK (Source: Cyble Vision)
- Valid Accounts (T1078): Qilin affiliates gain initial access via leaked or purchased credentials.
- Replication Through Removable Media (T1091): Qilin ransomware spreads through removable media to facilitate lateral movement.
- Spearphishing Link (T1566.002): Qilin affiliates use phishing emails with malicious attachments for initial access.
- Scheduled Task (T1053.005): Qilin ransomware establishes persistence by creating scheduled tasks for malicious payload execution.
- Command and Scripting Interpreter (T1059): Qilin ransomware uses command-line interfaces and scripting interpreters to execute malicious commands and scripts.
- Scheduled Task (T1053.005): Qilin ransomware maintains persistence through scheduled tasks.
- Valid Accounts (T1078): Gaining access via leaked or purchased credentials is a method for persistence.
- Registry Run Keys/Startup Folder (T1547.001): Qilin ransomware adds entries to registry run keys or places executables in startup folders for persistence.
- Scheduled Task (T1053.005): Persistence maintained by scheduled tasks.
- Process Injection (T1055): Qilin ransomware may inject malicious code into legitimate processes to escalate privileges and evade detection.
- Valid Accounts (T1078): Leaked or purchased credentials used for privilege escalation.
- Group Policy Modification (T1484.001): Alters group policies to weaken security configurations.
- Registry Run Keys/Startup Folder (T1547.001): Persistence achieved by modifying registry run keys or placing executables in startup folders.
- Process Injection (T1055): Malicious code injected into processes to evade detection.
- Valid Accounts (T1078): Gaining access through leaked or purchased credentials.
- Modify Registry (T1112): Qilin ransomware modifies registry settings to evade defenses.
- Group Policy Modification (T1484.001): Alters group policies to weaken security.
- Disable Windows Event Logging (T1562.002): Disables event logging to hinder detection and analysis.
- Safe Mode Boot (T1562.009): Reboots systems into Safe Mode to disable security before encryption.
- Credentials In Files (T1552.001): Qilin ransomware searches for and extracts credentials from files.
- Group Policy Preferences (T1552.006): Exploits credentials stored in Group Policy Preferences for privilege escalation.