Since its emergence in 2021, Storm-0501—also known as Hunters International—has developed into one of the most persistent and advanced ransomware threats in the global cybercrime landscape. Initially surfacing with attacks on U.S. school districts, the group has since diversified its arsenal, tactics, and target base, displaying an adaptive strategy that has kept it relevant and dangerous.
Storm-0501 began its operations by leveraging the Sabbath ransomware strain, hitting educational institutions across the United States. As the group matured, it pivoted towards a ransomware-as-a-service (RaaS) model—a popular approach among modern cybercriminal syndicates. This allowed them to scale operations and outsource parts of the attack chain to affiliates while maintaining control over infrastructure and payloads.
By 2023, the group had evolved. Following the takedown of the Hive RaaS network by international law enforcement agencies, Storm-0501 adapted quickly, adopting the BlackCat ransomware variant in early 2023. Later that year, they introduced their own strain under the Hunters International brand.
Advanced Techniques and Attack Vectors
Storm-0501 distinguishes itself through the creative and technical methods it uses to breach, maintain, and exploit access to victim environments. The group often initiates attacks by stealing credentials or exploiting known vulnerabilities in publicly accessible applications. Notable examples include flaws in widely used enterprise tools such as Zoho ManageEngine and Citrix NetScaler.
Once inside a network, the group employs tools like IcedID malware for credential harvesting, as well as Cobalt Strike for command-and-control (C2) operations. In some cases, Storm-0501 has been observed using custom-built remote monitoring and management (RMM) tools, PowerShell scripts, and unique reverse proxies to tunnel traffic stealthily across compromised networks.
Their usage of scheduled tasks and abuse of legitimate system utilities like Windows Task Scheduler highlight their emphasis on stealth and persistence. In many cases, they avoid using traditional malware altogether, opting instead to live off the land, leveraging existing system tools to execute commands and exfiltrate data.
Geographic and Sectoral Reach

One of the most interesting aspects of Storm-0501’s operations is the breadth of its targeting. The group has launched attacks in over 100 countries, ranging from highly developed economies like the United States, the United Kingdom, Germany, and Australia, to emerging markets such as Kenya, Bangladesh, and Peru.
Industries impacted by Storm-0501 are similarly diverse. Their targets include critical infrastructure and high-value sectors such as government, law enforcement, energy, aerospace and defense, healthcare, and financial services. However, they’ve also hit less traditionally targeted sectors like agriculture, media, and consumer goods, indicating a broad operational scope that seeks to exploit vulnerabilities wherever they may lie.
Evolution of Malware Families
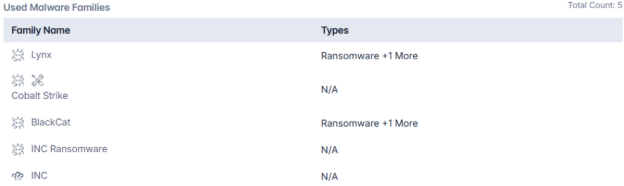
Over time, Storm-0501 has employed a variety of ransomware strains, including BlackCat, INC, and most recently, Lynx ransomware. Lynx, introduced in mid-2024 as a successor to INC, is especially notable for its RaaS deployment model and aggressive tactics. Victims affected by Lynx typically find their files encrypted with a “.lynx” extension and face threats of data leaks if ransom demands are not met. The malware is also designed to delete backups, thereby eliminating conventional recovery options and increasing the likelihood of ransom payments.
Lynx’s flexibility in infection vectors—including phishing emails, drive-by downloads, and compromised credentials—makes it an effective tool for attackers. Meanwhile, the continued reliance on Cobalt Strike, both in its original form and in modified variants like Cobalt Strike Cat, highlights the group’s comfort with complex, modular toolkits that enhance persistence and evade detection.
Tactical Depth and Persistence Mechanisms
Storm-0501’s operations reflect a deep understanding of modern enterprise architectures. Their use of valid, often inactive user accounts for lateral movement is particularly concerning, as it allows them to remain undetected for extended periods. These accounts often provide elevated privileges or access to sensitive systems, making them ideal tools for attackers seeking to deepen their foothold.
Moreover, the group employs multiple persistence techniques, including creating new local accounts on compromised systems and scheduling hidden tasks that evade traditional detection methods. These strategies not only ensure continued access but also complicate remediation efforts for victims.
Links to Other Threat Actors
Storm-0501 does not operate in isolation. There is a growing body of evidence suggesting overlaps in tooling and infrastructure with other notable threat actors such as ALPHV, FIN8, and Earth Alux. This interconnectivity within the cybercriminal ecosystem enhances the capabilities of each group and increases the complexity of attribution and defense.
Additionally, threat intelligence has identified similarities between Storm-0501 and other groups known to originate from countries like China, Russia, and Vietnam. Although definitive attribution remains elusive, such overlaps suggest shared resources or coordination between cybercrime factions.
Conclusion
Storm-0501 has proven to be a highly adaptive and persistent ransomware group, upgrading its tactics and tools to remain effective despite global efforts to contain it. With victims across industries and geographies, it exemplifies the growth of modern cyber threats.
To counter such threats, organizations need real-time, AI-powered threat intelligence. Cyble, a global leader in AI-native cybersecurity, empowers enterprises and governments with advanced platforms like Cyble Vision and Cyble Titan—enabling faster detection, deeper visibility, and proactive defense.
As actors like Storm-0501 continue to adapt, Cyble helps ensure defenders stay informed. Book a FREE DEMO today and discover how Cyble can elevate your cybersecurity posture.
Mitigation and Recommendations
- Leverage solutions like Cyble Vision to monitor emerging ransomware trends, detect early warning indicators, and analyze attacker infrastructure in real time.
- Regularly update and patch systems, especially widely exploited platforms such as Zoho ManageEngine, Citrix NetScaler, and VPN appliances, to close common entry points.
- Enforce multi-factor authentication (MFA), monitor dormant or unused accounts, and apply least-privilege principles to reduce lateral movement opportunities.
- Utilize tools like Cyble Titan for advanced endpoint visibility, threat containment, and behavioral detection to counter malware-less techniques and “living off the land” tactics.
- Detect abuse of Windows Task Scheduler, scripts, and RMM tools by auditing system behavior and implementing anomaly-based detection rules.
- Since initial access often occurs through phishing, train employees to recognize social engineering tactics and report suspicious communications.
- Integrate insights from platforms like Cyble’s Threat Library and CRIL reports to stay updated on malware evolution (e.g., Lynx ransomware) and shared infrastructure among threat groups.
MITRE Attack Techniques Associated with Storm-0501
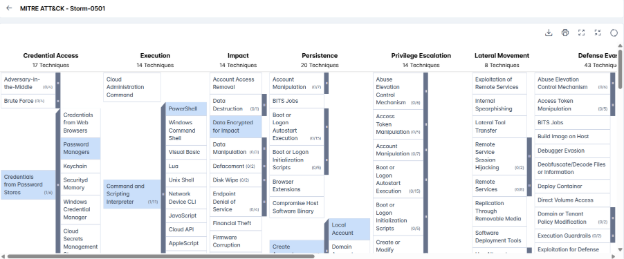
- Valid Accounts (T1078): Adversaries use stolen or inactive user credentials to log into systems and avoid detection, often bypassing authentication controls.
- Exploit Public-Facing Application (T1190): Attackers exploit known vulnerabilities in internet-facing systems (e.g., web servers, Citrix, or Zoho ManageEngine) to gain a foothold in the network.
- Scheduled Task (T1053.005): Malicious tasks are scheduled using Windows Task Scheduler to execute code at specific times or during startup, enabling stealthy operations.
- PowerShell (T1059.001): Attackers use PowerShell scripts to run commands, download payloads, or move laterally without triggering antivirus or touching disk.
- Scheduled Task (T1053.005): Scheduled tasks are reused post-compromise to maintain access over time, sometimes configured to remain hidden from standard admin tools.
- Valid Accounts (T1078): Stolen or dormant user accounts allow attackers to stay inside the network with legitimate access, reducing the chance of detection.
- Local Account (T1136.001): New local accounts are created to maintain long-term access without needing external tools, using commands like net user or dscl.
- Scheduled Task (T1053.005): Tasks are configured to run under privileged accounts, allowing adversaries to escalate permissions without raising red flags.
- Valid Accounts (T1078): Access to privileged credentials gives attackers elevated control, letting them bypass restrictions and access sensitive systems.