Cyble details Storm-1567, an APT behind the Akira Ransomware-as-a-Service, using double extortion tactics to encrypt and exfiltrate data, causing global disruptions.
Storm-1567 is an advanced persistent threat (APT) actor behind the ransomware-as-a-service (RaaS) known as Akira. First spotted targeting Swedish organizations in March 2023, Storm-1567 quickly gained notoriety for employing a “double extortion” strategy that not only encrypts files but also exfiltrates sensitive data before the encryption process, threatening to release this information unless a ransom is paid.
This threat actor is also known by other aliases, including AkiraGOLD, SAHARAPUNK, and SPIDER, each reflecting the group’s adaptability and stealth in its cyber operations. Storm-1567’s tactics, techniques, and procedures (TTPs) align with some of the most notorious ransomware operations to date, drawing comparisons to the infamous Conti malware, and it continues to cause disruptions to organizations worldwide.
Storm-1567 operates as a sophisticated cybercrime syndicate that leverages a Ransomware-as-a-Service (RaaS) model, providing malicious actors with the necessary tools to carry out cyberattacks. This model allows the group to maintain a relatively low profile while enabling affiliates to execute attacks using the Akira ransomware.
The group’s most notorious technique is its double extortion tactic. This involves exfiltrating sensitive data from compromised organizations before initiating encryption. Once the data is stolen, Storm-1567 threatens to release it publicly if the victim does not comply with the ransom demands. This increases the pressure on the target organization to pay, as the risk of data exposure could cause irreparable harm to the victim’s reputation and business operations.
Akira, the group’s ransomware of choice, utilizes the ChaCha encryption algorithm, known for its speed and security, making it an ideal choice for attackers seeking to lock files quickly. The ransomware also takes advantage of Windows Management Instrumentation (WMI) and PowerShell for lateral movement and persistence, allowing the attackers to spread within the network and exfiltrate valuable data with minimal detection.
Targeted Countries and Industries

Cyble Vision Threat Library (Source: Cyble Vision)
Storm-1567, a global ransomware group, targets a wide range of countries and industries, demonstrating its ability to strike organizations across continents. Its attacks are not limited to any specific region, affecting countries in North America, Europe, Asia, Africa, Latin America, and Oceania. Notable countries impacted include the United States, Canada, Brazil, Mexico, Kenya, South Africa, France, Germany, and several others.
The group’s attacks span across a broad array of industries, each with unique vulnerabilities that Storm-1567 exploits for financial gain. Key sectors under threat include aerospace and defense, where sensitive data and intellectual property are prime targets, and agriculture, where supply chain data is vulnerable. The automotive and BFSI industries are also at high risk, with stolen data potentially causing financial and operational damage. Chemical companies, construction firms, and consumer goods industries face similar dangers, as their proprietary information and financial data are valuable targets.
Education, energy, and utilities are particularly vulnerable to disruption, with attacks potentially leading to societal and economic impacts. Food and beverage industries are also at risk due to the sensitive nature of their data. Additionally, government and law enforcement agencies face heightened stakes, as breaches can affect national security and international relations. Healthcare, hospitality, IT, and manufacturing sectors are frequent targets, with cyberattacks disrupting critical services and causing financial losses.
Other industries, such as media and entertainment, metals and mining, pharmaceuticals and biotechnology, and professional services, are also vulnerable to cybercriminal activity. Real estate, retail, technology, telecommunications, and transportation & logistics industries are similarly at risk, with data breaches and system disruptions potentially resulting in operational failures and financial consequences.
The Attack Lifecycle
Storm-1567’s attack methods are notably calculated and efficient, employing various techniques to ensure successful network intrusions and to maximize the financial payoff. Their operations unfold in several stages, each with its own set of methods and tools.
1. Initial Access: Exploiting Compromised Credentials
Storm-1567 typically gains initial access to a target network through the use of compromised credentials. These credentials are often harvested from prior data breaches or weakly secured systems. The group focuses on exploiting external remote services, such as VPNs or Citrix systems, where valid account credentials are used to bypass access controls and enter the network.
Once inside, Storm-1567 operators leverage remote services for ongoing access, which can be difficult to detect. These services allow the group to maintain persistent entry points, making it harder for victims to secure their networks once an attack has been initiated.
2. Lateral Movement: PowerShell and WMI for Reconnaissance
Once inside the network, Storm-1567 uses tools like PowerShell and WMI to facilitate lateral movement. These tools enable the group to move through the network and gather intelligence on the environment, mapping out valuable systems, files, and data to target for exfiltration. Storm-1567 operators may also deploy other reconnaissance tools like SoftPerfect Network Scanner and SharpHound, which help them gather more detailed information on the compromised network’s structure.
In addition to these tools, Storm-1567 relies on valid accounts to escalate privileges and avoid detection. These accounts may be those of inactive users, former employees, or compromised administrative credentials. The attackers use these to gain elevated privileges and expand their reach within the target network, all while avoiding triggering security alarms.
3. Data Exfiltration and Ransomware Deployment
Before launching the encryption process, Storm-1567 exfiltrates data from the compromised organization. This is done using tools like WinSCP, FileZilla, and Ngrok, which facilitate exfiltration and ensure the stolen data is transferred securely, often using encrypted channels to evade detection.
Once the data is securely exfiltrated, the ransomware is deployed using the ChaCha encryption algorithm to lock files. The encryption process is fast and efficient, making it difficult for victims to recover their files without paying ransom. The group then demands payment in cryptocurrency, threatening to release the stolen data if the ransom is not paid.
4. Double Extortion: A Growing Trend
The most troubling aspect of Storm-1567’s operations is their use of double extortion. This technique involves not only locking the victim’s files but also stealing sensitive data prior to encryption. Once the data is exfiltrated, the attackers demand payment under the threat of publicly releasing the stolen data. This increases the pressure on organizations to pay the ransom, as it raises the risk of exposing confidential information to competitors, clients, or the public.
Storm-1567’s double extortion tactics are part of a broader trend in the world of cybercrime, with many ransomware groups opting to exfiltrate data before encrypting it. This strategy increases the likelihood of a victim paying the ransom, as it adds an extra layer of financial and reputational damage.
Tools and Malware Used by Storm-1567
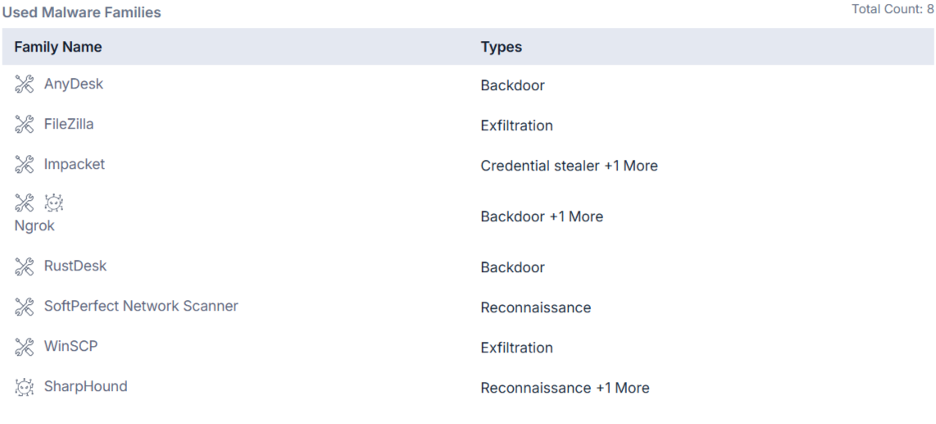 Tools Used by Storm-1567 (Source: Cyble Vision)
Tools Used by Storm-1567 (Source: Cyble Vision)
Storm-1567 employs a variety of tools to facilitate their operations, making their attacks difficult to detect and thwart. These tools are used for everything from lateral movement and reconnaissance to data exfiltration and ransomware deployment. Some of the most notable tools used by the group include:
- AnyDesk: A legitimate remote access tool that is often used by Storm-1567 for command-and-control purposes. Once installed on a compromised system, it allows the group to remotely control and manipulate systems within the network.
- Impacket: A suite of tools used for credential stealing and lateral movement. This tool allows Storm-1567 to manipulate network traffic and gain access to internal systems.
- Ngrok: Used for creating secure tunnels for data exfiltration and command-and-control traffic.
- WinSCP and FileZilla: Both tools are used for secure file transfers, allowing the attackers to exfiltrate stolen data with minimal risk of detection.
Conclusion
Storm-1567 is a growing cyber threat using advanced tactics like double extortion and compromised credentials, targeting high-value industries like healthcare and government. To defend against such threats, organizations must implement proactive security measures. Cyble, a leader in AI-driven threat intelligence, provides advanced tools and continuous monitoring to help businesses stay protected at all times. Schedule a demo today to see how Cyble can help protect you against cyber threats such as Storm-1567.
Mitigating the Threat of Storm-1567
Given the advanced nature of Storm-1567’s attack methods, organizations must adopt a multi-layered approach to defense. Below are several key recommendations to help protect against Storm-1567 and similar ransomware groups:
- Strengthen Access Control Measures: Implement multi-factor authentication (MFA) and enforce strong password policies to minimize the risk of credential theft.
- Patch Vulnerabilities Regularly: Maintain an effective patch management program to promptly address vulnerabilities and prevent exploitation.
- Network Segmentation: Use network segmentation to limit lateral movement and restrict attackers’ access to critical systems and data.
- Enhanced Monitoring and Detection: Deploy advanced monitoring tools to detect suspicious activity and stop attacks before they escalate.
- Regular Backups: Perform regular backups and store them securely to ensure data restoration without paying ransom.
MITRE attack Techniques Associated with Storm-1567
 MITRE ATT&CK (Source: Cyble Vision)
MITRE ATT&CK (Source: Cyble Vision)
Initial Access (TA0001) – Valid Accounts (T1078): Adversaries may use compromised credentials to bypass access controls and gain access to systems, remote services, or elevated privileges, including exploiting inactive accounts for stealth.
Initial Access (TA0001) – External Remote Services (T1133): Adversaries may leverage remote services like VPNs and Citrix to gain initial access or maintain persistent access to a network, often requiring valid credentials.
Initial Access (TA0001) – Exploit Public-Facing Application (T1190): Adversaries exploit vulnerabilities in internet-facing applications, such as websites or network devices, to gain access to a network or escalate privileges.
Initial Access (TA0001) – Spearphishing Attachment (T1566.001): Adversaries send spearphishing emails with malicious attachments to exploit vulnerabilities and execute malware on victim systems.
Initial Access (TA0001) – Spearphishing Link (T1566.002): Adversaries send spearphishing emails with malicious links to websites that exploit browser vulnerabilities or prompt users to download malicious content.
Persistence (TA0003) – Valid Accounts (T1078): Compromised credentials may be used to maintain access to systems and services, including exploiting inactive accounts for stealthy persistence.
Persistence (TA0003) – External Remote Services (T1133): Adversaries may use remote services like VPNs or Citrix to maintain persistent access to a network, sometimes via exposed, unauthenticated services.
Persistence (TA0003) – Domain Account (T1136.002): Adversaries create domain accounts to maintain access to systems across an Active Directory environment, bypassing the need for external remote access tools.
Privilege Escalation (TA0004) – Valid Accounts (T1078): Compromised credentials are used to escalate privileges, granting access to higher-level systems or restricted areas within a network.
Defense Evasion (TA0005) – Valid Accounts (T1078): Adversaries use legitimate credentials to evade detection and maintain access without raising alarms, often by exploiting inactive accounts.
Defense Evasion (TA0005) – Disable or Modify Tools (T1562.001): Adversaries disable or tamper with security tools to avoid detection of malware or alter system components to prevent security tools from functioning properly.
Credential Access (TA0006) – OS Credential Dumping (T1003): Adversaries dump credential material from the operating system to obtain login details, which can be used for lateral movement within the network.
Credential Access (TA0006) – LSASS Memory (T1003.001): Adversaries access credentials stored in LSASS process memory, using tools like mimikatz or procdump to extract login details for lateral movement.
Discovery (TA0007) – System Network Configuration Discovery (T1016): Adversaries gather information about network configurations (e.g., IP/MAC addresses) to plan follow-up actions and lateral movement.
Discovery (TA0007) – Remote System Discovery (T1018): Adversaries search for other systems on the network by IP address, hostname, or other identifiers to facilitate lateral movement.